WO1996034473A2 - A multi-purpose high speed cryptographically secure sequence generator based on zeta one-way functions - Google Patents
A multi-purpose high speed cryptographically secure sequence generator based on zeta one-way functions Download PDFInfo
- Publication number
- WO1996034473A2 WO1996034473A2 PCT/US1996/003270 US9603270W WO9634473A2 WO 1996034473 A2 WO1996034473 A2 WO 1996034473A2 US 9603270 W US9603270 W US 9603270W WO 9634473 A2 WO9634473 A2 WO 9634473A2
- Authority
- WO
- WIPO (PCT)
- Prior art keywords
- primes
- public key
- zeta
- distributed public
- code
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Ceased
Links
Classifications
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F7/00—Methods or arrangements for processing data by operating upon the order or content of the data handled
- G06F7/58—Random or pseudo-random number generators
- G06F7/582—Pseudo-random number generators
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/06—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols the encryption apparatus using shift registers or memories for block-wise or stream coding, e.g. DES systems or RC4; Hash functions; Pseudorandom sequence generators
- H04L9/065—Encryption by serially and continuously modifying data stream elements, e.g. stream cipher systems, RC4, SEAL or A5/3
- H04L9/0656—Pseudorandom key sequence combined element-for-element with data sequence, e.g. one-time-pad [OTP] or Vernam's cipher
- H04L9/0662—Pseudorandom key sequence combined element-for-element with data sequence, e.g. one-time-pad [OTP] or Vernam's cipher with particular pseudorandom sequence generator
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/30—Public key, i.e. encryption algorithm being computationally infeasible to invert or user's encryption keys not requiring secrecy
- H04L9/3093—Public key, i.e. encryption algorithm being computationally infeasible to invert or user's encryption keys not requiring secrecy involving Lattices or polynomial equations, e.g. NTRU scheme
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F7/00—Methods or arrangements for processing data by operating upon the order or content of the data handled
- G06F7/60—Methods or arrangements for performing computations using a digital non-denominational number representation, i.e. number representation without radix; Computing devices using combinations of denominational and non-denominational quantity representations, e.g. using difunction pulse trains, STEELE computers, phase computers
- G06F7/72—Methods or arrangements for performing computations using a digital non-denominational number representation, i.e. number representation without radix; Computing devices using combinations of denominational and non-denominational quantity representations, e.g. using difunction pulse trains, STEELE computers, phase computers using residue arithmetic
- G06F7/724—Finite field arithmetic
- G06F7/725—Finite field arithmetic over elliptic curves
Definitions
- the present invention relates to the generation of cryptographically secure sequences at very high speed. More particularly, this invention relates to the generation of such sequences with predetermined probability distribution with cryptographic security based on zeta-one-way functions with applications to authentication, key transfer, and public-key cryptography.
- the one-time pad cryptosystem is provably secure from the informationtheoretic point of view introduced by Claude Shannon (C.E. Shannon, Communication theory of secrecy systems, Bell Systems Technical Journal 28 (1949), 657-715) and later refined by Martin Hellman (M.E. Hellman, An extension of Shannon's approach to cryptography, IEEE Transaction on Information Theory v. IT-23 n.3 ( 1977), 289-294).
- the one-time pad system according to Ronald Rivest.
- Rivest points out that one motivation for generating random pseudorandom sequences is for use in the one-time pad cryptosystem (ibid p. 735).
- Rivest ibid p. 737
- Manuel Blum and Silvio Micali introduced the first method for designing provably secure pseudorandom bit generators based on one-way predicates (M. Blum and S.
- Rivest ibid p. 729
- Whitfield Diffie and Martin Hellman in 1976 (W. Diffie and M.E. Hellman, New Directions in Cryptography, IEEE Transactions on Information Theory IT-22 ( 1976), 644-654, also described in U.S. patent number 4,200,700).
- Rivest observes that their general method makes use of trapdoor one-way permutations (ibid p 729) .
- Rivest also observes that the Diffie- Hellman method allows two part ies to establish a shared secret key via a public discussion that anyone can overhear. Rivest himself, together with Adi Shamir and Leonard Adleman, introduced a system known today as the RSA public-key cryptosystem (R. Rivest, A.
- Shamir, and L.M. ADLEMAN A method for obtaining digital signatures and public-key cryptosystems, Communications of the ACM 21 (1978), 120-126, also described in U.S. patent number 4,405,829).
- the pioneering work on probabilistic public-key encryption was performed by Shafi Goldwasser and Silvio Micali (S. Goldwasser and S. Micali, Probabilistic encryption, Journal of Computer and System Sciences 26 (2) (1984), 270-299).
- Goldwasser and Micali employ the intractability of the quadratic residue problem in their constructions.
- the Diffie-Hellman, the RSA and the Goldwasser and Micali systems employ trapdoor one-way functions which have the deficiency that they require non-linear computations in extremely large finite rings.
- the public-key cryptosystem provides dynamic encryption, i .e. a given bit will be encrypted in a totally different manner at each time.
- stream cipher code based on zeta-one-way functions can be generated by arithmetic operations in small finite fields, i.e., finite fields whose number of elements is at most polynomial in the logarithm of the analytic conductor of the associated zeta function. This allows for easy implementat ion of the algorithms on low level computing devices with table driven modules.
- the present invention provides a high performance, high integrity, cryptographically secure sequence generator based on zeta one-way functions for pseudorandom sequence generation, authentication, key transfer by public discussion, and public key encryption.
- the system according to the invention is particularly suited towards implementation using currently available digital technology, commercially popular microprocessor based systems, and other affordable digital components. Significant portions of the system may be implemented and significant portions of the method according to the invention may be performed by software in a microcomputer based system or by hardware installed in such systems or other communication devices and combined with facsimile transmission components or communication terminals. BRIEF DESCRIPTION OF THE DRAWINGS
- Fig. 1 shows a zeta function chooser.
- Fig. 2 shows a zeta coefficient generator
- Fig. 3 shows a zeta pseudorandom number generator.
- Fig. 4 shows a zeta function authenticator
- Fig. 5 shows a Hasse-Weil pseudorandom number generator.
- Fig. 6 shows a specific Hasse-Weil pseudorandom number generator.
- Fig. 7 shows a public key transfer system.
- Fig. 8 shows a public key encryption system.
- Fig. 9 shows a zeta communication system with two stations.
- Fig. 10 shows a schematic diagram of the basic zeta function machine.
- Fig. 11 shows a zeta apparatus in pseudorandom sequence generator mode.
- Fig. 13 shows the zeta apparatus in an authentication mode.
- Fig. 14 shows the zeta apparatus in a key transfer mode.
- Fig. 15 shows the zeta apparatus in send-receive mode.
- n ⁇ 0 be an integer and define where for an arbitrary real number x ⁇ 0, [x] denotes the greatest integer less than or equal to x.
- d 2 (n) we refer to n .
- n t the bit size of n .
- n t the norm
- of a vector (n 1 , n 2 , . . . , n t ) N t as
- feasibly computed in polynomial time in condition (ii) and feasible polynomial time in condition (iii) means that the output may be created within the bounds of the technology employed and within the time bounds dictated by the purposes of the computation.
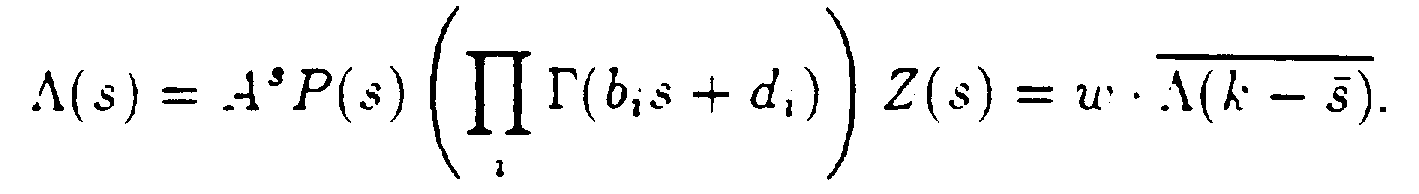
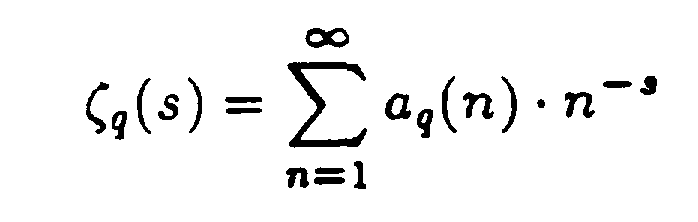
- the feasible polynomial time Selberg class Z consists of zeta functions Z(s) which are given as Dirichlet series
- a in the functional equat ion is called the analyt ic conductor of the zeta function.
- Z B C Z be a bounded subclass.
- the class Z B is said to be focused on (B, 2B) if for every zeta function in Z B its conductor A ⁇ (B, 2B).
- Hasse -Weil C Z of all zeta functions of Hasse-Weil type (see, D. Husemoller, Elliptic Curves, graduate Texts in Mathematics 111, Springer-Verlag, New York (1987), 291-293). Fix a large integer B. We now explicitly describe the one-way function based on a fixed bounded subclass
- the zeta functions in Z Hasse-Weil can be ordered by vectors of non-negative integers determined by the polynomial equations defining the variety associated to the zeta function in Z Hasse-Weil .
- Our one-way function is the function f where
- the Hasse-Weil zeta one-way functions are a special case of the more general Jacquet-Langlands zeta one-way functions which we now briefly describe.
- the Jacquet-Langlands class of zeta functions denoted Z J-L ⁇ Z, consists of zeta functions associated to cuspidal automorphic forms on reductive groups (see Stephen S. Gelbart, Automorphic Forms on A dele Groups, Annals of Mathematics Studies 83 Princeton University Press and University of Tokyo Press, Princeton, New Jersey (1975), 108-121). Similarly as above, it is possible to define a zeta one-way function for this class.
- a pseudorandom number generator based on q with uniform probability distribut ion function pdf is a feasible polynomial time algorithm whose outputs are sequences
- the zeta pseudorandom number generator based on q and Hasse-Weil zeta function ⁇ (s) simply outputs the sequence ⁇ q (2), ⁇ q (3), ⁇ q (5), ⁇ q (7), ⁇ q (11), ⁇ q (13), ⁇ q (17), ... running over the list of the precomputed positive integral primes.
- the Zeta Pseudorandom Number Generator ZPNG The Zeta Pseudorandom Number Generator ZPNG:
- the Zeta Function Chooser 20 which accepts as inputs: k 10, and a pair (q, pdf) 11 consisting of a positive integer q ⁇ 2 and a rational probability distribution pdf on q symbols.
- the input 11 goes to the Abelian Variety Classifier 12 which chooses a class of abelian varieties V.
- the input k 10, together with the output V of 12 is presented to the Fast Abelian Variety Generator 13 which generates a particular abelian variety v ⁇ V and outputs the zeta code associated to v. This completes the description of the Zeta Function Chooser 20 encapsulated in figure 1.
- ZCG 30 accepts as inputs, an input password k 10. a pair (q. pdf) 11 consisting of a positive integer q ⁇ 2 and a rational probability distribution function pdf on q symbols, and a monotone increasing sequence 22 of 6 positive prime integers (P 1 ,P 2 , ... ,P s ). Inputs 10 and 11 are presented to the Zeta Function Chooser 20 which outputs the zeta code for producing a zeta function
- the data, zcs, is then forwarded to the q-Reducer 31 which computes the new sequence zcsq ⁇ (P1), ⁇ (P 2 ),... , ⁇ (p s ) (mod q),
- the final output zcsq will be a pseudorandom sequence on the q symbols ⁇ 0, 1.2, ... , q— 1 ⁇ with probability distribution pdf. This completes the description of the Zeta Pseudorandom Number Generator ZPNG.
- the Zeta Pseudorandom Number Generator ZPNG 41 Upon receiving the inputs k (0), s, 40, the Zeta Pseudorandom Number Generator ZPNG 41 outputs zeta code which is transformed by the Zeta Code Transformer 42 and converted to suitable input for the Fast Abelian Variety Generator 13 which generates the abelian variety v(s) and computes the zeta code k(s) associated to v(s).
- This information is sent to the Public Key Announcer 43 which announces the public key k(s) for the state s.
- the public and private keys k(s), v(s) are then sent to the Authenticator 44 which publicly announces v(s) if authentication is required.
- the input is a positive rational integer k, 50 which uniquely determines a pair of integers ⁇ , b satisfying b 3 — 27 ⁇ 2 0.
- the pair of integers ( ⁇ , b) may be produced from the input k , 50, by employing a one-way function.
- the Fast Elliptic Curve Generator 51 generates the elliptic curve
- the Hasse-Weil Zeta Function Coefficient Producer 52 has 2 inputs: the elliptic curve E outputted by 51 (which in the general case is referred to as the zeta code in figure 2), and the input (p 1 , . . . ,p s ), 53.
- the Hasse-Weil Zeta Function Coefficient Producer 52 (see, D. Husemoller, Elliptic Curves, graduate Texts in Mathematics 111 , Springer-Verlag, New York (1987), 291- 293) then outputs the coefficients ⁇ (p 1 ), . . , ⁇ (p s )
- the inputs k, 50 and (p 1 , . . . , p s ), 53 are sent to the Hasse-Weil Zeta Function Coefficient Generator 60 which ouputs the zeta coefficients ⁇ (p 1 ), . . . , a(p s ). These are sent to the 2-Reducer 61 which reduces each of these coefficients (mod 2) ⁇ (P 1 ) whil ⁇ (P s ) (mod 2).
- the Prime Chooser 71 Upon receiving the input 70 of a positive integer r, the Prime Chooser 71 randomly chooses r primes p i t , P i 2 . P i 3 , . . . P i r in the set p. (the second party chooses r' primes These are sent to the Multiplier
- the Jacobi Symbol Generator 73 computes the vector where
- the Jacobi Symbol Generator sends the vector of Jacobi symbols to the Public Key Announcer 74.
- the Public Key Announcer 74 publicly announces the vector
- Jacobi Symbol Chooser 75 the Jacobi Symbol Chooser chooses the vector of Jacobi symbols
- the Jacobi Symbol Generator 73 Up n receiving the input the Jacobi Symbol Generator 73 generates the list of Jacobi symbols This list is then sent to the Encryptor 81.
- the Jacobi Symbol Chooser 75 upon receiving the public encryption key then
- the Multiplier 72 then multiplies these symbols and transfers the product k to the Encryptor 81.
- the Encryptor 81 then produces the list of plus and minus ones given by
- the Zeta Apparatus is illustrated in figure 9. It includes identical subsystems, A and B, which communicate through Communication Modules 95 (which receive and transmit code) and which also communicate with off-line Prime Storers 91, 92.
- Prime Storers 91 , 92 store and produce disjoint sets of primes (determined by Artin reciprocity) from a predetermined algebraic number field. For example, in the special case where the algebraic number field is the rational number field, we may take the set of primes stored in 91 to be the primes congruent to 1 modulo 8, and the set of primes stored in 92, the primes congruent to 5 modulo 8.
- the main components of the Zeta Apparatus are: identical Zeta Machines 90 which perform arithmetic computations; the Communication Modules 95 for information exchange between subsystems A, B; Collection/Distribution Modules 93 for internally storing and routing data within a subsystem; Feature Modules 94 for specifying required modes of operation.
- the Zeta Apparatus operates in the following modes: Pseudorandom Sequence Generator Mode; Authentication Mode; Key Transfer Mode; Send/Receive Mode: Privacy Enhancer Mode (this mode operates in conjunct ion with the latter three modes).
- the most basic operating mode of the Zeta Apparatus is as a pseudorandom sequence generator. This mode of operation is readily employed in the operation of stream ciphers, and is utilized in the other modes of operation of the Zeta Apparatus.
- the higher modes of operation refer to authentication, key exchange by public discussion and message transfer employing public key encryption. These higher modes of operation can be enhanced by a unique feature employed in t he Zeta Apparatus allowing users of the Zeta Apparatus to employ private keys for enhanced security.
- the Zeta Machine operates in the following manner.
- the Prime Chooser 71 requests a set of primes (denoted P-set) from the Prime Storer 100. After receiving P-set, Prime Chooser 71 chooses a subset of P-set (denoted P-subset) and sends P-subset to both the Multiplier 72 and the Artin Symbol Chooser 102.
- the Multiplier 72 produces from P-subset the conductor which is the product of the primes in P-subset.
- the conductor is sent to the Artin Symbol Generator 101 which then requests an additional set of primes (denoted Auxiliary P-set) from the Prime Storer 100 and then computes from the conductor and Auxiliary P-set the Artin symbol list which is then sent to the Store and Forward Module 103.
- the primes of the P- set and or the Auxiliary P-set may be generated or calculated according to predetermined criteria or retrieved over a communication channel.
- the Artin Symbol Chooser 102 upon receiving P-subset from Prime Chooser 71 and an External P-set, produces Artin symbol sub-list which is then sent to the Multiplier 72 which simply multiplies the Artin symbols in the Artin symbol sub-list producing the keycode which is sent to the Store and Forward Module 103.
- Figure 11 represents the Feature Module 94 which includes three submod- ules: Privacy Enhancer Submodule 110: Authenticator Submodule 111 ; Bit Corrector Submodule 112.
- the Feature Module 94 configures its submodules 110, 111. 112 according to the specified mode of operation of the Zeta Apparat us.
- Modes of Operation Figure 12 illustrates the operation of the Zeta Apparatus in Pseudorandom Sequence Generator Mode.
- the Prime Chooser 71 requests a set of primes (denoted P-set) from the Prime Storer 100. After receiving P-set, Prime Chooser 71 chooses a subset of P-set (denoted P-subset) and sends P-subset to the Multiplier 72.
- the Multiplier 72 produces from P- subset the conductor which is the product of the primes in P-subset.
- the conductor is sent to the Artin Symbol Generator 101 which then requests the primes Auxiliary P-set from the Prime Storer 100 and then computes from the conductor and P-set the Artin symbol list which is then sent to the Privacy Enhancer Submodule 110.
- the Privacy Enhancer Submodule 110 produces the Privacy enhanced Artin symbol list and sends it to the Store and Forward Module 103.
- the Privacy Enhancer Submodule 110 is in one of two states: ON or OFF. If it is ON, it permutes the Artin symbol list employing a oneway permutation known privately to both subsystems A, B. If it is OFF, it simply transmits the Artin symbol list to the Store and Forward Module 103.
- Figure 13 illustrates the Zeta Apparatus in Authentication Mode.
- subsystem B is in Pseudorandom Generator Mode and transmits P- set, P-subset and Privacy enhanced Artin symbol list to subsystem A which then operates as follows.
- Subsystem A computes from the received inputs P-set and P-subset the Privacy enhanced Artin symbol list and sends it to the Authenticator Submodule 111 which compares it to the Privacy enhanced Artin symbol list transmitted by subsystem B . If these lists agree then authentication is confirmed.
- Figure 14 illustrates the Zeta Apparatus in Key Transfer Mode. In this mode of operat ion, subsystems A . B operate symmetrically, so it is enough to restrict this description to subsystem A.
- Store and Forward Modules and Transmitters and Receivers are omitted in order to simplify the figure, labeled lightning bolts indicate transmissions.
- the Prime Chooser 71 requests a set of primes (denoted P-set(A)) from the Prime Storer 91. After receiving P-set(A), Prime Chooser 71 chooses a subset of P-set(A) (denoted P-subset(A)) and sends P-subset(A) to the Multiplier 72.
- the Multiplier 72 produces from P-subset(A) the conductor(A) which is the product of the primes in P-subset(A).
- the conductor(A) is sent to the Artin Symbol Generator 101 which then requests the primes P-set(B) (transmitted by subsystem B) from the Prime Storer 92 and then computes from the conductor(A) and P-set(B) the Artin symbol list(A) which is then sent to the Privacy Enhancer Submodule 110.
- the Privacy Enhancer Submodule 110 then sends Privacy enhanced Artin symbol list (A) to the transmitter which transmits this list (upon request) to the Artin Symbol Chooser 102 of subsystem B.
- the Prime Chooser 71 also sends P-subset(A) to the Artin Symbol Chooser 102 which then requests Privacy enhanced Artin symbol list(B) from subsystem B.
- Artin Symbol Chooser 102 computes Artin symbol sublist(A) and sends this sublist to the Multiplier 72.
- the Multiplier 72 then multiplies the Artin symbols in Artin symbol sub-list(A) which is the key code.
- the key code will be identical in both subsystems and is then sent to the Store and Forward Module 103.
- P-set(A) and P-set(B) may be stored in both subsystems, generated in each subsystem according to a predetermined or specified criteria or transmitted to a subsystem from an accessible storage or generation facility.
- Figure 15 illustrat es the Zeta A pparat us in Send/Receive Mode.
- Store and Forward Modules and Transmitters and Receivers are omitted in order to simplify the figure.
- Labeled lightning bolts indicate transmissions.
- the Prime Chooser 71 requests a set of primes (denoted P-set(A)) from the Prime Storer 91.
- Prime Chooser 71 chooses a subset of P-set(A) (denoted Psubset(A)) and sends P-subset(A) to the Multiplier 72.
- the Multiplier 72 produces from P-subset(A) the conductor(A) which is the product of the primes in P-subset(A).
- the conducior(A) is sent to the Artin Symbol Generator 101 which then requests the primes P-set(B) (transmitted by subsystem B) from the Prime Storer 92 and then computes from the conductor(A) and P-set(B) the Artin symbol list(A) which is then sent to the Bit Corrector Submodule 112.
- the Prime Chooser 71 also sends P-subset(A) to the Artin Symbol Chooser 102 which then requests Privacy enhanced Artin symbol list(B) from subsystem B.
- Artin Symbol Chooser 102 computes Artin symbol sub-list(A) and sends this sublist to the Multiplier 72.
- the Bit Corrector Submodule 112 modifies the Artin symbol list(A ) (as previously discussed in t he sect ion on t he Public Key Encryption Scheme ) and sends this modified Art in symbol list to the Privacv Enhancer Submodule 110.
- the Privacy Enhancer Submodule 110 then sends this list to the transmitter which transmits this list (upon request) to the Artin Symbol Chooser 102 of subsystem B.
- the privacy enhancer submodules illustrated in figures 11-15 may be omitted from the respective embodiments.
- the privacy enhancer is an optional and advantageous feature in certain applications.
Landscapes
- Engineering & Computer Science (AREA)
- Theoretical Computer Science (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Mathematical Optimization (AREA)
- Signal Processing (AREA)
- Mathematical Analysis (AREA)
- Computer Networks & Wireless Communication (AREA)
- Pure & Applied Mathematics (AREA)
- Computer Security & Cryptography (AREA)
- Algebra (AREA)
- Computing Systems (AREA)
- Mathematical Physics (AREA)
- Computational Mathematics (AREA)
- General Engineering & Computer Science (AREA)
- Mobile Radio Communication Systems (AREA)
- Control Of Eletrric Generators (AREA)
Abstract
Description
Claims
Priority Applications (3)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| JP8529780A JPH11502321A (en) | 1995-03-09 | 1996-03-11 | Multipurpose fast encryption secure sequence generator based on zeta directional function |
| EP96929645A EP0872079A2 (en) | 1995-03-09 | 1996-03-11 | A multi-purpose high speed cryptographically secure sequence generator based on zeta one-way functions |
| AU68947/96A AU711911B2 (en) | 1995-03-09 | 1996-03-11 | A multi-purpose high speed cryptographically secure sequence generator based on zeta-one-way functions |
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US08/400,928 US5577124A (en) | 1995-03-09 | 1995-03-09 | Multi-purpose high speed cryptographically secure sequence generator based on zeta-one-way functions |
| US08/400,928 | 1995-03-09 |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| WO1996034473A2 true WO1996034473A2 (en) | 1996-10-31 |
| WO1996034473A3 WO1996034473A3 (en) | 1996-12-27 |
Family
ID=23585578
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| PCT/US1996/003270 Ceased WO1996034473A2 (en) | 1995-03-09 | 1996-03-11 | A multi-purpose high speed cryptographically secure sequence generator based on zeta one-way functions |
Country Status (6)
| Country | Link |
|---|---|
| US (2) | US5577124A (en) |
| EP (1) | EP0872079A2 (en) |
| JP (1) | JPH11502321A (en) |
| AU (1) | AU711911B2 (en) |
| CA (1) | CA2214903A1 (en) |
| WO (1) | WO1996034473A2 (en) |
Cited By (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US7098322B2 (en) | 1998-04-29 | 2006-08-29 | Vlaams Interuniversitair Instituut Voor Biotechnologie Vzw | CD40-interacting and TRAF-interacting proteins |
Families Citing this family (53)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| EP0693836A1 (en) * | 1994-06-10 | 1996-01-24 | Sun Microsystems, Inc. | Method and apparatus for a key-management scheme for internet protocols. |
| US5577124A (en) * | 1995-03-09 | 1996-11-19 | Arithmetica, Inc. | Multi-purpose high speed cryptographically secure sequence generator based on zeta-one-way functions |
| FR2737370B1 (en) * | 1995-07-27 | 1997-08-22 | Bull Cp8 | CRYPTOGRAPHIC COMMUNICATION METHOD |
| AU743461B2 (en) * | 1995-07-27 | 2002-01-24 | Cp8 Technologies | Cryptographic communication process |
| CA2263588C (en) | 1996-08-19 | 2005-01-18 | Ntru Cryptosystems, Inc. | Public key cryptosystem method and apparatus |
| US6266771B1 (en) | 1997-02-10 | 2001-07-24 | The Regents Of The University Of California | Probabilistic signature scheme |
| US7212632B2 (en) | 1998-02-13 | 2007-05-01 | Tecsec, Inc. | Cryptographic key split combiner |
| US6885747B1 (en) | 1997-02-13 | 2005-04-26 | Tec.Sec, Inc. | Cryptographic key split combiner |
| US6694433B1 (en) * | 1997-05-08 | 2004-02-17 | Tecsec, Inc. | XML encryption scheme |
| US6044388A (en) * | 1997-05-15 | 2000-03-28 | International Business Machine Corporation | Pseudorandom number generator |
| US6240183B1 (en) | 1997-06-19 | 2001-05-29 | Brian E. Marchant | Security apparatus for data transmission with dynamic random encryption |
| US6236728B1 (en) | 1997-06-19 | 2001-05-22 | Brian E. Marchant | Security apparatus for data transmission with dynamic random encryption |
| US6094486A (en) * | 1997-06-19 | 2000-07-25 | Marchant; Brian E. | Security apparatus for data transmission with dynamic random encryption |
| CA2310588A1 (en) * | 1997-12-05 | 1999-06-17 | Secured Information Technology, Inc. | Transformation methods for optimizing elliptic curve cryptographic computations |
| US8077870B2 (en) * | 1998-02-13 | 2011-12-13 | Tecsec, Inc. | Cryptographic key split binder for use with tagged data elements |
| US7095852B2 (en) | 1998-02-13 | 2006-08-22 | Tecsec, Inc. | Cryptographic key split binder for use with tagged data elements |
| US7079653B2 (en) * | 1998-02-13 | 2006-07-18 | Tecsec, Inc. | Cryptographic key split binding process and apparatus |
| US7111173B1 (en) | 1998-09-01 | 2006-09-19 | Tecsec, Inc. | Encryption process including a biometric unit |
| RU2153191C2 (en) | 1998-09-29 | 2000-07-20 | Закрытое акционерное общество "Алкорсофт" | Method for blind production of digital rsa signature and device which implements said method |
| US6684330B1 (en) * | 1998-10-16 | 2004-01-27 | Tecsec, Inc. | Cryptographic information and flow control |
| RU2157001C2 (en) | 1998-11-25 | 2000-09-27 | Закрытое акционерное общество "Алкорсофт" | Method for conducting transactions |
| US7095851B1 (en) | 1999-03-11 | 2006-08-22 | Tecsec, Inc. | Voice and data encryption method using a cryptographic key split combiner |
| CA2368307C (en) * | 1999-03-11 | 2007-05-22 | Tecsec, Incorporated | Voice and data encryption method using a cryptographic key split combiner |
| US6668265B1 (en) * | 1999-03-29 | 2003-12-23 | Communications Research Laboratory, Ministry Of Posts And Telecommunications | Apparatus and method for outputting sequence of vectors, data recording medium, and carrier wave signal |
| KR100345685B1 (en) * | 1999-11-15 | 2002-07-27 | 한국전자통신연구원 | Key generating method, and encryption and decryption system and its method by using the braid operation |
| US7190787B1 (en) * | 1999-11-30 | 2007-03-13 | Intel Corporation | Stream cipher having a combiner function with storage based shuffle unit |
| KR20000024419A (en) * | 2000-02-12 | 2000-05-06 | 배민관 | A new public key cryptosystem : BMG |
| US6718038B1 (en) * | 2000-07-27 | 2004-04-06 | The United States Of America As Represented By The National Security Agency | Cryptographic method using modified fractional fourier transform kernel |
| CA2325615A1 (en) * | 2000-11-10 | 2002-05-10 | Robert F. Enenkel | Method and apparatus for evaluating polynomials and rational functions |
| US20020073345A1 (en) * | 2000-12-11 | 2002-06-13 | Joseph Esfahani | Secure indentification method and apparatus |
| US6691141B2 (en) * | 2001-04-13 | 2004-02-10 | Science Applications International Corp. | Method and apparatus for generating random number generators |
| DE10229811A1 (en) * | 2002-07-03 | 2004-01-15 | Deutsche Telekom Ag | Encryption method based on factorization |
| CN101099329B (en) | 2004-11-11 | 2012-12-26 | 塞尔蒂卡姆公司 | A new trapdoor one-way function based on elliptic curves and its application to shorter signatures and asymmetric encryption |
| US7680268B2 (en) | 2005-03-15 | 2010-03-16 | Microsoft Corporation | Elliptic curve point octupling using single instruction multiple data processing |
| US7702098B2 (en) * | 2005-03-15 | 2010-04-20 | Microsoft Corporation | Elliptic curve point octupling for weighted projective coordinates |
| US8719324B1 (en) * | 2005-04-28 | 2014-05-06 | Cetin K. Koc | Spectral modular arithmetic method and apparatus |
| US8183980B2 (en) * | 2005-08-31 | 2012-05-22 | Assa Abloy Ab | Device authentication using a unidirectional protocol |
| US8180047B2 (en) * | 2006-01-13 | 2012-05-15 | Microsoft Corporation | Trapdoor pairings |
| US20090153290A1 (en) * | 2007-12-14 | 2009-06-18 | Farpointe Data, Inc., A California Corporation | Secure interface for access control systems |
| EP2316180A4 (en) | 2008-08-11 | 2011-12-28 | Assa Abloy Ab | Secure wiegand communications |
| EP2157526B1 (en) * | 2008-08-14 | 2014-04-30 | Assa Abloy Ab | RFID reader with embedded attack detection heuristics |
| US8244909B1 (en) * | 2009-06-18 | 2012-08-14 | Google Inc. | Method, apparatus and networking equipment for performing flow hashing using quasi cryptographic hash functions |
| US10148285B1 (en) | 2012-07-25 | 2018-12-04 | Erich Schmitt | Abstraction and de-abstraction of a digital data stream |
| US10795858B1 (en) | 2014-02-18 | 2020-10-06 | Erich Schmitt | Universal abstraction and de-abstraction of a digital data stream |
| KR102520502B1 (en) * | 2016-08-02 | 2023-04-12 | 엑스-로고스, 엘엘씨 | Method and system for enhanced data-centric encryption system using geometric algebra |
| US10452877B2 (en) | 2016-12-16 | 2019-10-22 | Assa Abloy Ab | Methods to combine and auto-configure wiegand and RS485 |
| TWI760546B (en) * | 2017-08-23 | 2022-04-11 | 安地卡及巴布達商區塊鏈控股有限公司 | Computer-implemented system and method for highly secure, high speed encryption and transmission of data |
| US11146397B2 (en) * | 2017-10-31 | 2021-10-12 | Micro Focus Llc | Encoding abelian variety-based ciphertext with metadata |
| US11526927B1 (en) * | 2018-12-05 | 2022-12-13 | Amazon Technologies, Inc. | Distributed numeric sequence generation |
| US11416806B1 (en) | 2018-12-05 | 2022-08-16 | Amazon Technologies, Inc. | Distributed numeric sequence generation |
| US11764943B2 (en) | 2020-08-10 | 2023-09-19 | Algemetric, Inc. | Methods and systems for somewhat homomorphic encryption and key updates based on geometric algebra for distributed ledger/blockchain technology |
| WO2022061188A1 (en) | 2020-09-17 | 2022-03-24 | X-Logos, LLC | Methods and systems for distributed computation within a fully homomorphic encryption scheme using p-adic numbers |
| US11546142B1 (en) * | 2021-12-22 | 2023-01-03 | Bakhtgerey Sinchev | Cryptography key generation method for encryption and decryption |
Family Cites Families (6)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US4200770A (en) * | 1977-09-06 | 1980-04-29 | Stanford University | Cryptographic apparatus and method |
| US4405829A (en) * | 1977-12-14 | 1983-09-20 | Massachusetts Institute Of Technology | Cryptographic communications system and method |
| US5272755A (en) * | 1991-06-28 | 1993-12-21 | Matsushita Electric Industrial Co., Ltd. | Public key cryptosystem with an elliptic curve |
| US5159632A (en) * | 1991-09-17 | 1992-10-27 | Next Computer, Inc. | Method and apparatus for public key exchange in a cryptographic system |
| US5373558A (en) * | 1993-05-25 | 1994-12-13 | Chaum; David | Desinated-confirmer signature systems |
| US5577124A (en) * | 1995-03-09 | 1996-11-19 | Arithmetica, Inc. | Multi-purpose high speed cryptographically secure sequence generator based on zeta-one-way functions |
-
1995
- 1995-03-09 US US08/400,928 patent/US5577124A/en not_active Expired - Fee Related
-
1996
- 1996-03-11 WO PCT/US1996/003270 patent/WO1996034473A2/en not_active Ceased
- 1996-03-11 EP EP96929645A patent/EP0872079A2/en not_active Withdrawn
- 1996-03-11 JP JP8529780A patent/JPH11502321A/en active Pending
- 1996-03-11 CA CA002214903A patent/CA2214903A1/en not_active Abandoned
- 1996-03-11 AU AU68947/96A patent/AU711911B2/en not_active Ceased
- 1996-11-19 US US08/752,033 patent/US5751808A/en not_active Expired - Fee Related
Non-Patent Citations (2)
| Title |
|---|
| A.M.S. ABSTRACTS, SPECIAL SESSION ON ANALYTICAL NUMBER THEORY, SPRING MEETING OF THE AMERICAN MATHEMATICAL SOCIETY , vol. 15, no. 3, April 1994, NEW YORK, page 349 XP000604391 ANSHEL ET AL.: "ZETA FUNCTIONS, ONE-WAY FUNCTIONS AND CRYPTOGRAPHY" cited in the application * |
| HUSEM\LLER: "ELLIPTIC CURVES" 1987 , SPRINGER , NEW YORK XP002017339 cited in the application Ÿ2. ZETA FUNCTIONS OF CURVES OVER Q see page 291 - page 293 * |
Cited By (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US7098322B2 (en) | 1998-04-29 | 2006-08-29 | Vlaams Interuniversitair Instituut Voor Biotechnologie Vzw | CD40-interacting and TRAF-interacting proteins |
Also Published As
| Publication number | Publication date |
|---|---|
| JPH11502321A (en) | 1999-02-23 |
| EP0872079A2 (en) | 1998-10-21 |
| CA2214903A1 (en) | 1996-10-31 |
| WO1996034473A3 (en) | 1996-12-27 |
| AU6894796A (en) | 1996-11-18 |
| US5577124A (en) | 1996-11-19 |
| AU711911B2 (en) | 1999-10-21 |
| US5751808A (en) | 1998-05-12 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| AU711911B2 (en) | A multi-purpose high speed cryptographically secure sequence generator based on zeta-one-way functions | |
| US5220606A (en) | Cryptographic system and method | |
| US6490352B1 (en) | Cryptographic elliptic curve apparatus and method | |
| Damgård | Towards practical public key systems secure against chosen ciphertext attacks | |
| US6411715B1 (en) | Methods and apparatus for verifying the cryptographic security of a selected private and public key pair without knowing the private key | |
| JP3862500B2 (en) | High-speed elliptic curve encryption method and apparatus by direct embedding method | |
| EP0503119B1 (en) | Public key cryptographic system using elliptic curves over rings | |
| Nguyen et al. | Lattice reduction in cryptology: An update | |
| US5463690A (en) | Method and apparatus for public key exchange in a cryptographic system | |
| US5159632A (en) | Method and apparatus for public key exchange in a cryptographic system | |
| CA2262549C (en) | Accelerating public-key cryptography by precomputing randomly generated pairs | |
| US7649999B2 (en) | Method and apparatus for establishing a key agreement protocol | |
| EP0635956A2 (en) | Encryption apparatus, communication system using the same and method therefor | |
| Mao | Guaranteed correct sharing of integer factorization with off-line shareholders | |
| CN101087195A (en) | Cyclotomic polynomial construction of discrete logarithm cryptosystems over finite fields | |
| US20020041684A1 (en) | Public-key encryption and key-sharing methods | |
| Vanstone et al. | Elliptic curve cryptosystems using curves of smooth order over the ring Z/sub n | |
| JP3658004B2 (en) | Communications system | |
| EP0973293A2 (en) | Public-key cryptography with increased protection against selective ciphertext attack | |
| JP3816558B2 (en) | Cryptosystem | |
| JP2002252610A (en) | Encryption device and decryption device, and public key encryption system and public key decryption system | |
| EP1148675A1 (en) | Public key cryptograph and key sharing method | |
| JP3278790B2 (en) | Public key encryption method and public key encryption system | |
| JP2002023626A (en) | Public key encryption method and communication system using public key encryption | |
| Liu | Computation over encrypted data |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| AK | Designated states |
Kind code of ref document: A2 Designated state(s): AL AM AT AU AZ BB BG BR BY CA CH CN CZ DE DK EE ES FI GB GE HU IS JP KE KG KP KR KZ LK LR LS LT LU LV MD MG MK MN MW MX NO NZ PL PT RO RU SD SE SG SI SK TJ TM TR TT UA UG US UZ VN AM AZ BY KG KZ MD RU TJ TM |
|
| AL | Designated countries for regional patents |
Kind code of ref document: A2 Designated state(s): KE LS MW SD SZ UG AT BE CH DE DK ES FI FR GB GR IE IT LU MC NL PT SE BF BJ CF CG CI CM GA GN |
|
| DFPE | Request for preliminary examination filed prior to expiration of 19th month from priority date (pct application filed before 20040101) | ||
| 121 | Ep: the epo has been informed by wipo that ep was designated in this application | ||
| ENP | Entry into the national phase |
Ref document number: 2214903 Country of ref document: CA Ref country code: CA Ref document number: 2214903 Kind code of ref document: A Format of ref document f/p: F |
|
| ENP | Entry into the national phase |
Ref country code: JP Ref document number: 1996 529780 Kind code of ref document: A Format of ref document f/p: F |
|
| WWE | Wipo information: entry into national phase |
Ref document number: 1996929645 Country of ref document: EP |
|
| REG | Reference to national code |
Ref country code: DE Ref legal event code: 8642 |
|
| WWP | Wipo information: published in national office |
Ref document number: 1996929645 Country of ref document: EP |
|
| WWW | Wipo information: withdrawn in national office |
Ref document number: 1996929645 Country of ref document: EP |