WO2020054612A1 - トランザクション監査システム - Google Patents
トランザクション監査システム Download PDFInfo
- Publication number
- WO2020054612A1 WO2020054612A1 PCT/JP2019/035179 JP2019035179W WO2020054612A1 WO 2020054612 A1 WO2020054612 A1 WO 2020054612A1 JP 2019035179 W JP2019035179 W JP 2019035179W WO 2020054612 A1 WO2020054612 A1 WO 2020054612A1
- Authority
- WO
- WIPO (PCT)
- Prior art keywords
- data
- transaction
- audit
- transaction data
- table information
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Ceased
Links
Images
Classifications
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q20/00—Payment architectures, schemes or protocols
- G06Q20/38—Payment protocols; Details thereof
- G06Q20/382—Payment protocols; Details thereof insuring higher security of transaction
- G06Q20/3821—Electronic credentials
- G06Q20/38215—Use of certificates or encrypted proofs of transaction rights
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3236—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials using cryptographic hash functions
- H04L9/3239—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials using cryptographic hash functions involving non-keyed hash functions, e.g. modification detection codes [MDCs], MD5, SHA or RIPEMD
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/60—Protecting data
- G06F21/64—Protecting data integrity, e.g. using checksums, certificates or signatures
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q20/00—Payment architectures, schemes or protocols
- G06Q20/38—Payment protocols; Details thereof
- G06Q20/382—Payment protocols; Details thereof insuring higher security of transaction
- G06Q20/3825—Use of electronic signatures
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q20/00—Payment architectures, schemes or protocols
- G06Q20/38—Payment protocols; Details thereof
- G06Q20/389—Keeping log of transactions for guaranteeing non-repudiation of a transaction
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q20/00—Payment architectures, schemes or protocols
- G06Q20/38—Payment protocols; Details thereof
- G06Q20/40—Authorisation, e.g. identification of payer or payee, verification of customer or shop credentials; Review and approval of payers, e.g. check credit lines or negative lists
- G06Q20/401—Transaction verification
- G06Q20/4016—Transaction verification involving fraud or risk level assessment in transaction processing
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q40/00—Finance; Insurance; Tax strategies; Processing of corporate or income taxes
- G06Q40/12—Accounting
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/50—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols using hash chains, e.g. blockchains or hash trees
Definitions
- the present disclosure relates to a transaction audit system.
- Transactions business processing
- rules such as contracts between companies and internal regulations.
- a transaction may not be performed according to a rule to be applied, or data related to the transaction may be intentionally falsified.
- application data used for transactions and transaction data output from business systems are managed by a business log management system, etc., and internal auditors and external audit corporations use an audit tool to perform numerical analysis or original analysis. Audits are performed by comparing and verifying transactions.
- Patent Literature 1 discloses a business management system that automatically manages and audits logs without any omissions, including a log collection unit that collects a plurality of logs including information on work in a business from a business system, Based on information about the work included in each log collected by the log collection unit and a condition for classifying the work set in advance, it is specified which log each log belongs to, and belongs to the same business.
- An operation management system comprising: a management book data creation unit that creates data that aggregates logs as management book data.
- Patent Literature 1 since only the result (log) of the transaction is managed, the basis for outputting the result cannot be grasped. Further, when a problem such as a human error or tampering occurs, it is difficult to reproduce the situation at the time of occurrence of the problem, and there is a problem that a great deal of time and cost are required for organizing data for auditing.
- the present disclosure provides a transaction audit system that can ensure the authenticity of data and can perform an audit operation in a short time and at low cost.
- a transaction audit system constitutes a blockchain server, generates a terminal having a blockchain database, an application capable of inputting first transaction data, and generates second transaction data from the first transaction data.
- a transaction auditing system comprising: a database storing master data including automatic deployment rule data for performing the processing; and an audit engine connected to the terminal and the database. Input to the audit engine, the audit engine refers to the master data to generate the second transaction data, and generates the first transaction data and the second transaction data.
- Each data item and its value are decomposed to generate first table information.
- the data item includes at least a data model name, a version number, an application name, a user name, and an operation date and time.
- a block of a block chain is generated based on the first table information and recorded in the block chain database.
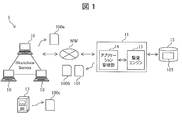
- FIG. 1 is a schematic diagram showing an overall configuration of a transaction audit system according to a first embodiment.
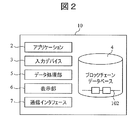
- FIG. 3 is a functional block diagram of a terminal.
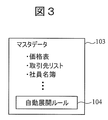
- FIG. 3 is a schematic diagram illustrating an example of master data.
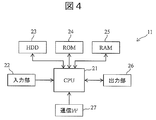
- FIG. 2 is a block diagram illustrating a hardware configuration example of a server device.
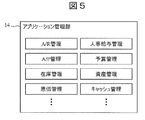
- FIG. 3 is a functional block diagram of an application management unit.
- FIG. 3 is a functional block diagram of an audit engine.
- FIG. 4 is a schematic diagram showing an example of table information.
- FIG. 2 is a schematic diagram illustrating an example of a block chain.
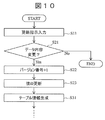
- 9 is a flowchart showing a transaction data recording process.
- 9 is a flowchart illustrating transaction data update processing.
- FIG. 9 is a schematic diagram showing table information generated from updated transaction data.
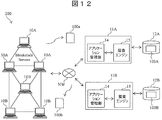
- FIG. 9 is a schematic diagram illustrating an overall configuration of a transaction audit system according to a second embodiment.
- the transaction audit system 1 is a system that is introduced into one company and records transaction data 100 on transactions performed within a company or between companies in a blockchain 102 to audit the transaction.
- Transactions are broadly divided into internal business processes performed based on internal rules of the company and external business processes performed based on external rules such as contract conditions between companies.
- the internal business processing includes, for example, budget management, personnel payroll management, inventory management, cost accounting management, production management, asset management, cash management, and the like.
- the internal rules are, for example, rules based on company rules, accounting standards, in-house rules, ground rules, and the like.
- the base law is an industry-specific law to which a company belongs, such as civil law, criminal law, financial law, and environmental law.
- External business processing includes, for example, sales management, purchasing management, A / R management, A / P management, service providing business management, outsourcing management, financial transaction management, and the like.
- the external rules are, for example, contracts between companies, oral contracts, rules in companies based on contracts between companies, business practices, accounting standards, rules, rules based on the law, and the like. Contracts between companies are not limited to documents, and may be unwritten rules such as oral contracts and business practices.
- FIG. 1 is a schematic diagram showing an overall configuration of a transaction auditing system 1 according to the first embodiment.
- the transaction audit system 1 includes a plurality of terminals 10, a server device 11, a database 12, and a business system 13.
- the terminal 10 is a computer connected to the server device 11 via the network NW, and is used in a company in which the transaction auditing system 1 of the present embodiment is introduced.
- a general-purpose computer for example, a general-purpose computer, a smartphone, a mobile phone, a PDA (Personal Digital Assistant), a tablet, a wearable (Wearable) terminal, and the like can be used.
- the terminals 10 are P2P (Peer to Peer) connected to each other, and have a function as a node of the blockchain server.
- the block chain platform of the transaction auditing system 1 a known one can be adopted.
- FIG. 2 is a functional block diagram of the terminal 10. As shown in FIG. 2, an application 2 for a user to perform a transaction is downloaded from the server device 11 to the terminal 10.
- the terminal 10 includes an input device 3, a blockchain database 4, a data processing unit 5, a display unit 6, and a communication interface 7.
- the input device 3 is, for example, an input device such as a mouse or a keyboard, and is configured to be capable of inputting transaction data 100a (first transaction data) on a GUI screen of the application 2 displayed on the display unit 6.
- the transaction data 100a is data relating to a transaction performed within a company or between companies, and is data input from the application 2 to the server device 11.
- the transaction data 100b (second transaction data) is data generated by the server device 11 according to the input of the transaction data 100a.
- the transaction data 100c (third transaction data) refers to data input from the external business system 13 to the terminal 10 or the server device 11. In this specification, the transaction data 100a to 100c may be collectively referred to as "transaction data 100".
- the transaction data 100 includes, for example, data items such as a data model name, information on the used application 2, an applied rule, a work item name, a version number, a user name, an operation date and time, and the value of each data item.
- the value type of each data item is set in advance according to the data item.
- the data model is information on each work in the business, such as receiving an order from a customer or shipping to a customer.
- the work item is information on a data model such as, for example, an order quantity and a shipment quantity.
- the value of the data item of the applied rule is, for example, the serial number of the rule.
- the data format (data format) of the transaction data 100 is not particularly limited.
- the data format of the transaction data 100a input from the application 2 to the server device 11 is, for example, a table information format.
- the data format of the transaction data 100c input from the external business system 13 to the server device 11 may be different from the format of the table information.
- the data processing unit 5 performs data processing for the terminal 10 to function as a node of the blockchain server.
- the data processing unit 5 calculates a hash value using a predetermined hash function based on the table information 101 received from the server device 11, and outputs the calculated hash value to the server device 11.
- the table information 101 is data generated by the server device 11 based on the transaction data 100 and recorded in the block chain 102. Details of the table information 101 will be described later.
- the data processing unit 5 generates a block of the block chain 102 based on the table information 101 received from the server device 11, and records the generated block in the block chain database 4.
- the data processing unit 5 may record the table information 101 generated from all the transaction data 100 in one block chain 102, or may create a plurality of block chains 102 and May be recorded in one block chain 102 for each.
- the block chain 102 is generated for each relevant transaction data 100, for example, the block chain 102 that records only the transaction data 100 shared by the used application 2 or the block that records only the update history of the master data 103 It can be divided into chains 102 and the like.
- the data processing unit 5 may record the same table information 101 in a plurality of block chains 102 at the same time. As a result, the history of the transaction data 100 can be used for a plurality of purposes, such as for internal use or between companies.
- the display unit 6 is configured to display a GUI screen of the application 2 and other information.
- the communication interface 7 is an interface for connecting the terminal 10 to the network NW and transmitting and receiving various data.
- the server device 11 includes an application management unit 14 that manages the application 2 and an audit engine 15 that executes various procedures for operating the transaction audit system 1 according to a program.
- the application management unit 14 and the audit engine 15 are connected so that data can be exchanged with each other. Detailed configurations and functions of the application management unit 14 and the audit engine 15 will be described later.
- the application management unit 14 and the audit engine 15 may be stored in the same server device 11 as shown in FIG. 1 or may be stored in different server devices.
- the database 12 is connected to the server device 11 as an external storage of the server device 11 and stores the master data 103. Note that the database 12 may be a storage unit stored in the server device 11.
- the business system 13 is a computer outside the blockchain server configured by the terminal 10 and is connected to the terminal 10 and the server device 11 via the network NW.
- the business system 13 is a system for performing a transaction, and is configured to be able to input the transaction data 100c to the terminal 10 or the server device 11 through a cooperation function such as RESTful @ API or WebXML.
- FIG. 3 is a schematic diagram showing an example of the master data 103.
- the master data 103 is data referred to in various transactions, and includes, for example, a price list, a business partner list, an employee list, and the like, as shown in FIG.
- the master data 103 includes data items such as a master name such as a price list, a business partner list, and an employee list, a data model name, a version number, a user name that has generated and updated, an operation date and time, and the like. And the value of each data item.
- the master data 103 includes the automatic expansion rule data 104 of the transaction data 100a.
- the automatic deployment rule data 104 is described based on rules such as the above internal rules and external rules.
- the automatic deployment rule data 104 is referred to by the audit engine 15 to automatically generate, update, and delete new transaction data 100b from the transaction data 100a input from the application 2.
- the transaction data 100a input from the terminal 10 includes the rule exception approval content as a data item. May be included.
- FIG. 4 is a block diagram illustrating a hardware configuration example of the server device 11.
- the server device 11 includes, for example, a CPU 21, an input unit 22, a hard disk drive (HDD) 23, a ROM 24, a RAM 25, an output unit 26, and a communication interface 27.
- the components shown in FIG. 4 may employ the same components as those generally known.
- the CPU 21 executes various procedures for operating each function of the audit engine 15 described below according to a program.
- the program is stored in the hard disk drive 23 and / or the ROM 24 and read out by the CPU 21.
- the input unit 22 is an interface that receives an input of the transaction data 100 a from the terminal 10 and outputs it to the CPU 21.
- the output unit 26 is an interface that outputs the transaction data 100 b and the table information 101 generated by the audit engine 15 to the terminal 10. It is.
- the communication interface 27 is an interface that receives the input of the transaction data 100c from the business system 13 and outputs the transaction data 100c to the CPU 21, and outputs various data generated as necessary to the business system 13.
- the communication interface 27 has a function as an interface for downloading the application 2 from the application management unit 14 to the terminal 10.
- FIG. 5 is a functional block diagram of the application management unit 14.
- the application management unit 14 manages various applications 2 for executing transactions in the terminal 10 as shown in FIG.
- the application 2 is downloaded to the terminal 10 via the network NW.
- the application 2 includes, for example, an A / R management application, an A / P management application, an inventory management application, a cost management application, a personnel payroll management application, a budget management application, an asset management application, and a cash management application.
- the A / R management application is an application that manages receivables such as accounts receivable and receivable.
- an A / R management application manages receivables (such as accounts receivable) generated by sales until collection.
- the A / P management application is a module that manages debts such as accounts payable and accounts payable.
- the A / P management application manages accounts payable (such as accounts payable) generated by purchasing goods until payment is executed.
- the inventory management application is an application that manages, for example, stocks of raw materials, products, commodities, and the like handled by a company, and monetary evaluation on the stocks.
- the cost management application is an application that manages the cost of products, goods, services, and the like handled by companies.
- HR payroll management applications include, for example, hiring, raising and raising employees, managing HR until retirement, salaries, bonuses, retirement benefits, allowances, insurance, pensions, and other money paid to or for employees. Is an application that manages
- the budget management application is an application that manages various budgets of a company, for example.
- the asset management application is an application that manages, for example, various assets owned by a company.
- the cache management application is, for example, an application that manages a cache held by a company.
- FIG. 6 is a functional block diagram of the audit engine 15. As shown in FIG. 6, the audit engine 15 includes an input unit 151, a data generation / update unit 152, a table information generation unit 153, an output unit 154, an audit unit 155, and a communication interface 156.
- the input unit 151 is an interface that receives an input of the transaction data 100a from the input unit 22.
- the communication interface 156 is an interface that receives an input of the transaction data 100c from the communication interface 27, and includes, for example, a RESTful @ API and a WebXML function.
- the data generation / update unit 152 When the transaction data 100a is input, the data generation / update unit 152 generates new transaction data 100b with reference to the master data 103 and the automatic deployment rule data 104, and outputs the new transaction data 100b to the table information generation unit 153. Further, the data generation / update unit 152 transmits the generated transaction data 100b to the terminal 10 via the output unit 154 and the application management unit 14, and causes the terminal 10 to display the transaction data 100b on the GUI screen of the application 2.
- the user inputs order data (transaction data 100a) on the GUI screen of the application 2 for managing the order and shipping.
- the order data includes, for example, data items such as a data model name, an application name, a version number of the order data, a requester name, a product name, a serial number, an order quantity, a user name, and a date and time of creating the order data.
- the data generating / updating unit 152 automatically generates shipping data (transaction data 100b) from order data with reference to the master data 103 and the automatic expansion rule data 104.
- the shipping data includes, for example, data items such as a data model name, an application name, an application rule, a version number of the shipping data, a shipping destination, a product name, a serial number, a shipping quantity, a delivery date, a user name, and a date and time when the shipping data was created.
- data items having the same contents are inherited by the same data item name.
- the automatic deployment rule data 104 indicates “shipping quantity” in the shipping data. Is described so that the value of the data item is “10 ⁇ Y”. Also, if there is a rule “commodity X is shipped within two weeks after receiving an order” between other companies, for example, the automatic deployment rule data 104 includes a data item “delivery date” in the shipping data, It is described to add a data item related to the rule.
- the transaction data 100, the master data 103, or the automatic deployment rule data 104 When there is a change in rules, such as a change in contract, a change in business specifications, or a change in the operation of another company, an input error in the transaction data 100a, or an error in the generated transaction data 100b.
- the transaction data 100, the master data 103, or the automatic deployment rule data 104 must be updated.
- the data item to be updated and its value are input to the data generation / update unit 152 as an update instruction, for example, by operating the terminal 10 of the user.
- the data generation / update unit 152 updates the transaction data 100, the master data 103, or the automatic deployment rule data 104 in accordance with an update instruction from the terminal 10, and outputs the updated data to the table information generation unit 153.
- the table information generation unit 153 decomposes the input transaction data 100a and the generated transaction data 100b into data items and values irrespective of the data format, utilizing an XDF (Extended @ Dynamic @ Form) framework.
- Information 101a and 101b (sometimes simply referred to as “table information 101 (first table information)”) are generated.
- the XDF framework is a function that dynamically handles menu items, screen designs, and data models based on data model definitions, screen definitions, file output definitions, and file input definitions. By using the XDF framework, it is possible to define a data model of a type that records the item values of the data model as separate lines instead of the database columns.
- FIG. 7 is a schematic diagram showing an example of the table information 101.
- the table information 101 includes data items such as a data model name, an application name, an application rule, a version number, a task item, a value, and a previous value (if any).
- data items such as a data model name, an application name, an application rule, a version number, a task item, a value, and a previous value (if any).
- the name of the user who performed the operation, the operation time, and the like are included.
- the table information generation unit 153 converts the table information 101 based on the transaction data 100a and the rule exception approval content. Generate.
- the table information generation unit 153 When the transaction data 100c is input from the business system 13, the table information generation unit 153 generates the table information 101 based only on the transaction data 100c. In this case, since the application and the applied rule through which the transaction data 100c is generated in the business system 13 are unknown, such information is not included in the table information 101.
- the output unit 154 outputs the table information 101 generated by the table information generation unit 153 to the terminal 10.
- the data processing unit 5 of the terminal 10 generates a hash value from the received table information 101 using a predetermined hash function, and transmits the hash value to the audit unit 155 of the audit engine 15 via the communication interface 7.
- FIG. 8 is a schematic diagram illustrating an example of the block chain 102.
- the block chain 102 includes, for each block, table information 101, a hash value of the immediately preceding block, and a nonce. Nonce refers to any value.
- the auditing unit 155 compares the hash value to be generated based on the block chain 102 stored in the block chain database 4 of the terminal 10 with the hash value received from the terminal 10 and determines that the block chain 102 And verify that they have not been tampered with or deleted without going through When determining that the blockchain 102 has been tampered with, the auditing unit 155 transmits a warning to the output unit 154.
- the output unit 154 transmits the warning received from the inspection unit 155 to the terminal 10 and causes the display unit 6 to display the warning.
- a method of displaying a warning for example, a method of displaying a warning in a message box on the display unit 6, a method of displaying a tampered or deleted portion in red on the GUI screen of the application 2 or the block chain 102, or the like may be adopted. it can.
- the transaction data 100a and 100b are all decomposed into predetermined data items and their values, and the unified table information 101 is obtained.
- all data can be recorded in the block chain 102 in the same format without depending on a specific data format.
- the application rule is also recorded in the block chain 102 as a data item, the basis of the transaction data 100 can be grasped.
- FIG. 9 is a flowchart illustrating a recording process of the transaction data 100 according to the present embodiment.
- step S1 the user inputs the transaction data 100a from the GUI screen of the application 2 downloaded to the terminal 10.
- the input transaction data 100a is transmitted to the input unit 151 of the audit engine 15 via the communication interface 7 and the network NW.
- the input unit 151 outputs the transaction data 100a to the data generation / update unit 152.
- step S2 upon receiving the transaction data 100a, the data generating / updating unit 152 generates new transaction data 100b with reference to the master data 103 stored in the database 12.
- the data generation / update unit 152 outputs the transaction data 100a and 100b to the table information generation unit 153.
- the transaction data 100a and 100b include data items related to the applied rules.
- the transaction data 100b generated by the data generation / update unit 152 is shipping data.
- step S3 the table information generation unit 153 decomposes the transaction data 100a and 100b into data items and their values using the XDF framework, and generates the table information 101.
- the table information generation unit 153 transmits the table information 101 to the communication interface 7 of the terminal 10 via the output unit 154.
- the communication interface 7 outputs the table information 101 to the data processing unit 5.
- step S4 the data processing unit 5 generates a hash value from the table information 101, and transmits the hash value to the audit unit 155 of the audit engine 15 via the communication interface 7.
- step S5 the data processing unit 5 records the table information 101 and the hash value of the immediately preceding block in the block of the block chain 102, and stores them in the block chain database 4.
- step S6 the inspection unit 155 compares the hash value received from the terminal 10 in step S4 with the hash value calculated from the blocks of the block chain 102 stored in the block chain database 4. If these hash values are the same, it is determined that the blockchain 102 stored in the blockchain database 4 has not been tampered with or deleted without going through a legitimate process, and the recording process ends.
- step S7 the auditing unit 155 determines that the blockchain 102 stored in the blockchain database 4 has been tampered with or deleted without going through a legitimate process, and the output unit 154.
- a warning is transmitted to the terminal 10 via the terminal.
- the terminal 10 receives the warning via the communication interface 7, displays the warning on the display unit 6, and ends the recording process.
- FIG. 10 is a flowchart showing a process of updating the transaction data 100.
- the transaction data 100b is updated.
- step S11 the user inputs an instruction to update the transaction data 100 from the GUI screen of the application 2.
- step S21 the data generating / updating unit 152 determines whether the instruction to update the transaction data 100b input in step S1 changes the content recorded in the block chain 102.
- step S21 If the update instruction is to change the content recorded in the block chain 102 (Yes in step S21), the data generation / update unit 152 adds +1 to the version number of the transaction data 100b in step S22.
- step S23 the data generation / update unit 152 changes the data items to be changed in the transaction data 100b, such as the update date and time, the name of the updater, and the value to be changed, and their values.
- the data generation / update unit 152 refers to the master data 103 and automatically changes the data item to be changed of the generated transaction data 100b and its value.
- step S31 based on the updated transaction data 100b, the table information generation unit 153 uses the XDF framework to update the updated data item and its value and the table information 101c including the pre-updated data item and its value.
- FIG. 11 is a schematic diagram showing table information 201 (second table information) generated according to the update of the transaction data 100b. As shown in FIG. 11, when the transaction data 100b is updated, the table information 201 includes the pre-update table information 101a and 101b and the table information 101c generated by the update.
- step S31 the recording process on the block chain 102 is performed based on the table information 201 in the same manner as in step S4 and subsequent steps in FIG.
- step S21 if the update instruction does not change the content recorded in the block chain 102 (No in step S21), the process after step S21 is not performed, and the recording process ends.
- the table information generation unit 153 when updating the transaction data 100a, the master data 103, or the automatic expansion rule data 104, the user issues an update instruction, the table information generation unit 153 generates the table information 201, and the block information is generated based on the table information 201. The recording process on the chain 102 is performed.
- the transaction auditing system 1 records the history of generation and update of the transaction data 100, the master data 103, and the automatic deployment rule data 104 as the blockchain 102. These data can be protected, and the authenticity of the data can be ensured. As described above, since only the transaction history is targeted for protection by the blockchain 102, the load at the time of executing the transaction can be reduced.
- the rule when the rule is changed, it is not necessary to change the program of the transaction auditing system 1, and the history can be recorded by changing the master data 103 or the automatic deployment rule data 104, so that the data verification at a later date is easy. is there.
- the auditing operation can be performed at a low cost without requiring much time for organizing the transaction data 100.
- the blockchain 102 guarantees that there is no unauthorized alteration or deletion, and the state can be obtained. You can also get the background. Therefore, it is easy to match the figures in the financial statements with the transaction data on which it is based in the auditing work of the company, and the transaction data is based on which rules, when, by which user, and how. It is possible to verify whether any operation has been performed. Further, it is possible to reproduce arbitrary data existing at a certain point in time on a common mechanism.
- the transaction audit system 200 of the present embodiment is different from the first embodiment in that the transaction audit system 200 is introduced to a plurality of companies and records the transaction data 100 of the plurality of companies.
- the components of the transaction auditing system 200 are the same as those of the first embodiment, and thus the description is omitted.
- FIG. 12 is a schematic diagram showing the overall configuration of the transaction auditing system 200 of the present embodiment.
- the transaction auditing system 200 is installed in two companies A and B.
- a plurality of terminals 10A owned by the company A and a plurality of terminals 10B owned by the company B are connected to each other via P2P (Peer to Peer), and each have a function as a node of the blockchain server.
- P2P Peer to Peer
- the companies A and B have server devices 11A and 11B and databases 12A and 12B, respectively.
- the terminals 10A and 10B and the server devices 11A and 11B are connected to the same network NW.
- Master database 103A is stored in database 12A of company A
- master data 103B is stored in database 12B of company B.
- a user belonging to the company A inputs the transaction data 100a from the terminal A, refers to the master data 103A, and generates the transaction data 100b, outputs the transaction data 100b to the terminal 10B or the server device 11B of the company B. Can be.
- the transaction auditing system 200 of the present embodiment can record the transaction data 100 of a plurality of companies in the blockchain 102.
- the causal relationship of the inter-company transaction can be retroactively verified, and the authenticity of the inter-company transaction is further ensured.
- the transaction data 100 of a plurality of companies exists on the common block chain 102, it can be used as a reference base for information such as AI.
- the transaction data 100 is recorded in the tamper-proof blockchain 102 together with the rules applied when the transaction data is generated. If the value is different from the expected value, it can be inferred that the applied rule has an error. Further, when a certain data item of certain transaction data 100 has a value different from an intended value even though the applied rule is correct, it is presumed that the program for operating the audit engine 15 has an error. Can be.
Landscapes
- Engineering & Computer Science (AREA)
- Business, Economics & Management (AREA)
- Accounting & Taxation (AREA)
- Computer Security & Cryptography (AREA)
- Theoretical Computer Science (AREA)
- Finance (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Strategic Management (AREA)
- General Business, Economics & Management (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Health & Medical Sciences (AREA)
- Bioethics (AREA)
- General Health & Medical Sciences (AREA)
- Computer Hardware Design (AREA)
- Software Systems (AREA)
- General Engineering & Computer Science (AREA)
- Development Economics (AREA)
- Economics (AREA)
- Marketing (AREA)
- Technology Law (AREA)
- Management, Administration, Business Operations System, And Electronic Commerce (AREA)
- Debugging And Monitoring (AREA)
Abstract
Description
図1~3を参照して、第1の実施形態に係るトランザクション監査システム1の全体構成について説明する。本実施形態に係るトランザクション監査システム1は、1つの企業に導入され、企業内又は企業間で行われるトランザクションに関するトランザクションデータ100をブロックチェーン102に記録することにより、トランザクションを監査するシステムである。
図12を参照して、第2の実施形態に係るトランザクション監査システム200について説明する。本実施形態のトランザクション監査システム200は、複数の企業に導入され、複数の企業におけるトランザクションデータ100を記録する点で、第1の実施形態と異なる。トランザクション監査システム200の構成要素は、第1の実施形態と同様であるため、説明を省略する。
2…アプリケーション
3…入力デバイス
4…ブロックチェーンデータベース
5…データ処理部
6…表示部
7…通信インタフェース
10…端末
11…サーバ装置
12…データベース
13…業務システム
14…アプリケーション管理部
15…監査エンジン
100…トランザクションデータ
101、201…テーブル情報
102…ブロックチェーン
103…マスタデータ
151…入力部
152…データ生成・更新部
153…テーブル情報生成部
154…出力部
155…監査部
156…通信インタフェース
Claims (5)
- ブロックチェーンサーバを構成し、ブロックチェーンデータベースと、第1のトランザクションデータを入力可能なアプリケーションとを有する端末と、
前記第1のトランザクションデータから第2のトランザクションデータを生成するための自動展開ルールデータを備えるマスタデータを格納するデータベースと、
前記端末及び前記データベースに接続される監査エンジンと、を備えるトランザクション監査システムであって、
前記端末により、前記第1のトランザクションデータを前記監査エンジンに入力し、
前記監査エンジンにより、前記マスタデータを参照して前記第2のトランザクションデータを生成し、
前記第1のトランザクションデータ及び前記第2のトランザクションデータをそれぞれデータ項目及びその値に分解して、第1のテーブル情報を生成し、
前記データ項目は、少なくともデータモデル名、バージョン番号、アプリケーション名、ユーザ名及び操作日時を含み、
前記端末により、前記第1のテーブル情報に基づいてブロックチェーンのブロックを生成し、前記ブロックチェーンデータベースに記録することを特徴とするトランザクション監査システム。 - 前記監査エンジンは、さらに前記ブロックチェーンが改ざんされていないかを監査することを特徴とする請求項1記載のトランザクション監査システム。
- 前記端末により、前記第1のトランザクションデータ、前記第2のトランザクションデータ又は前記マスタデータの更新指示を前記監査エンジンに入力し、
前記監査エンジンにより、前記バージョン番号に1を足し、前記データ項目及びその値を前記更新指示に従って更新し、第2のテーブル情報を生成し、
前記端末により、前記第2のテーブル情報に基づいて前記ブロックチェーンのブロックを生成し、前記ブロックチェーンデータベースに記録することを特徴とする請求項1記載のトランザクション監査システム。 - 前記監査エンジンに接続される業務システムをさらに備え、
前記業務システムにより、第3のトランザクションデータを前記監査エンジンに入力することを特徴とする請求項1記載のトランザクション監査システム。 - 複数の企業に導入されることを特徴とする請求項1乃至4いずれか1項記載のトランザクション監査システム。
Priority Applications (3)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| US17/272,868 US20210272113A1 (en) | 2018-09-11 | 2019-09-06 | Transaction audit system |
| JP2020545990A JP7057588B2 (ja) | 2018-09-11 | 2019-09-06 | トランザクション監査システム |
| EP19859718.9A EP3851993A4 (en) | 2018-09-11 | 2019-09-06 | Transaction audit system |
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| JP2018169990 | 2018-09-11 | ||
| JP2018-169990 | 2018-09-11 |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| WO2020054612A1 true WO2020054612A1 (ja) | 2020-03-19 |
Family
ID=69777640
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| PCT/JP2019/035179 Ceased WO2020054612A1 (ja) | 2018-09-11 | 2019-09-06 | トランザクション監査システム |
Country Status (4)
| Country | Link |
|---|---|
| US (1) | US20210272113A1 (ja) |
| EP (1) | EP3851993A4 (ja) |
| JP (1) | JP7057588B2 (ja) |
| WO (1) | WO2020054612A1 (ja) |
Cited By (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN112907243A (zh) * | 2021-02-09 | 2021-06-04 | 工银科技有限公司 | 区块链交易审计方法及装置 |
| US20220011743A1 (en) * | 2020-07-08 | 2022-01-13 | Vmware, Inc. | Malicious object detection in 3d printer device management |
| CN114661734A (zh) * | 2020-12-23 | 2022-06-24 | 上海唯链信息科技有限公司 | 基于区块链的数据审核方法、装置、设备及存储介质 |
| US11669772B2 (en) | 2019-11-05 | 2023-06-06 | Vmware, Inc. | 3D printer device management using machine learning |
| JP2024008114A (ja) * | 2022-07-07 | 2024-01-19 | トヨタ自動車株式会社 | データ管理装置およびデータ管理システム |
Families Citing this family (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN114358727A (zh) * | 2021-12-30 | 2022-04-15 | 山东易构软件技术股份有限公司 | 基于大数据平台的高速收费稽核辅助系统 |
| CN115757415B (zh) * | 2022-11-24 | 2025-03-11 | 北京火山引擎科技有限公司 | 一种数据处理方法、装置、计算机设备及存储介质 |
| US12591557B2 (en) * | 2023-06-28 | 2026-03-31 | Klickklack Information Security Co., Ltd. | Blockchain audit system |
Citations (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US6006242A (en) * | 1996-04-05 | 1999-12-21 | Bankers Systems, Inc. | Apparatus and method for dynamically creating a document |
| US20140101262A1 (en) * | 2012-10-05 | 2014-04-10 | Oracle International Corporation | Method and system for communicating within a messaging architecture using dynamic form generation |
| JP2016224819A (ja) | 2015-06-02 | 2016-12-28 | 日本電信電話株式会社 | 業務管理システム、業務管理方法および業務管理プログラム |
| US20180006831A1 (en) * | 2016-02-04 | 2018-01-04 | Nasdaq Technology Ab | Systems and methods for storing and sharing transactional data using distributed computing systems |
| US20180227119A1 (en) * | 2017-02-09 | 2018-08-09 | International Business Machines Corporation | Managing a database management system using a blockchain database |
Family Cites Families (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US8396811B1 (en) * | 1999-02-26 | 2013-03-12 | Syncada Llc | Validation approach for auditing a vendor-based transaction |
| KR101784454B1 (ko) * | 2015-09-25 | 2017-10-11 | 쿠팡 주식회사 | 쇼핑 서비스 제공 장치, 방법 및 컴퓨터 판독 가능한 기록 매체 |
| US20170228371A1 (en) * | 2016-02-05 | 2017-08-10 | Manifold Technology, Inc. | Blockchain-enhanced database |
| US11037095B2 (en) * | 2017-09-11 | 2021-06-15 | Accenture Global Solutions Limited | Distributed ledger technology for freight system |
| US20190303541A1 (en) * | 2018-04-02 | 2019-10-03 | Ca, Inc. | Auditing smart contracts configured to manage and document software audits |
-
2019
- 2019-09-06 EP EP19859718.9A patent/EP3851993A4/en not_active Withdrawn
- 2019-09-06 JP JP2020545990A patent/JP7057588B2/ja active Active
- 2019-09-06 US US17/272,868 patent/US20210272113A1/en not_active Abandoned
- 2019-09-06 WO PCT/JP2019/035179 patent/WO2020054612A1/ja not_active Ceased
Patent Citations (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US6006242A (en) * | 1996-04-05 | 1999-12-21 | Bankers Systems, Inc. | Apparatus and method for dynamically creating a document |
| US20140101262A1 (en) * | 2012-10-05 | 2014-04-10 | Oracle International Corporation | Method and system for communicating within a messaging architecture using dynamic form generation |
| JP2016224819A (ja) | 2015-06-02 | 2016-12-28 | 日本電信電話株式会社 | 業務管理システム、業務管理方法および業務管理プログラム |
| US20180006831A1 (en) * | 2016-02-04 | 2018-01-04 | Nasdaq Technology Ab | Systems and methods for storing and sharing transactional data using distributed computing systems |
| US20180227119A1 (en) * | 2017-02-09 | 2018-08-09 | International Business Machines Corporation | Managing a database management system using a blockchain database |
Non-Patent Citations (1)
| Title |
|---|
| See also references of EP3851993A4 |
Cited By (6)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US11669772B2 (en) | 2019-11-05 | 2023-06-06 | Vmware, Inc. | 3D printer device management using machine learning |
| US20220011743A1 (en) * | 2020-07-08 | 2022-01-13 | Vmware, Inc. | Malicious object detection in 3d printer device management |
| US12093017B2 (en) * | 2020-07-08 | 2024-09-17 | Omnissa, Llc | Malicious object detection in 3D printer device management |
| CN114661734A (zh) * | 2020-12-23 | 2022-06-24 | 上海唯链信息科技有限公司 | 基于区块链的数据审核方法、装置、设备及存储介质 |
| CN112907243A (zh) * | 2021-02-09 | 2021-06-04 | 工银科技有限公司 | 区块链交易审计方法及装置 |
| JP2024008114A (ja) * | 2022-07-07 | 2024-01-19 | トヨタ自動車株式会社 | データ管理装置およびデータ管理システム |
Also Published As
| Publication number | Publication date |
|---|---|
| EP3851993A4 (en) | 2022-04-27 |
| JP7057588B2 (ja) | 2022-04-20 |
| US20210272113A1 (en) | 2021-09-02 |
| EP3851993A1 (en) | 2021-07-21 |
| JPWO2020054612A1 (ja) | 2021-08-30 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| JP7057588B2 (ja) | トランザクション監査システム | |
| Sreenivasan et al. | Modeling the enablers of sourcing risks faced by startups in COVID-19 era | |
| CN111177275A (zh) | 基于区块链的管理方法、终端、装置及存储介质 | |
| US10956911B2 (en) | System and method of managing data injection into an executing data processing system | |
| US20130226318A1 (en) | Process transformation and transitioning apparatuses, methods and systems | |
| US20150356477A1 (en) | Method and system for technology risk and control | |
| US20100211413A1 (en) | Revising containerized processing logic for use in insurance claim processing | |
| US20230385248A1 (en) | System, Method, and Computer Program Products for Modeling Complex Hierarchical Metadata with Multi-Generational Terms | |
| US11625502B2 (en) | Data processing systems for identifying and modifying processes that are subject to data subject access requests | |
| CN108711104A (zh) | 基于区块链的实物资产信息流转方法、装置和设备 | |
| US20250103562A1 (en) | Data migration factory | |
| Vallemoni | Data lineage and metadata in payment ecosystems: Auditability and regulatory readiness across the life cycle | |
| Maurizio et al. | EAI and SOA: factors and methods influencing the integration of multiple ERP systems (in an SAP environment) to comply with the Sarbanes‐Oxley Act | |
| Klijn et al. | Event knowledge graphs for auditing: a case study | |
| JP2007122388A (ja) | 会計システムと会計方法、及びプログラム | |
| Krajka et al. | The impact of blockchain technology on operational and strategic risks in the supply chain-a systematic literature review | |
| US20210398232A1 (en) | System and method for implementing a market data contract analytics tool | |
| JP6943407B2 (ja) | 業務管理システム、及び業務管理方法 | |
| Antonio | The Effectiveness of Continuous Auditing Implementation: Developing Automated Audit Systems for Fraud and Error Detections | |
| KR101505079B1 (ko) | 정보보호업무 지원시스템 및 방법 | |
| US9489438B2 (en) | Systems and methods for visualizing master data services information | |
| Kolhe | Blockchain-based smart contracts for business process automation | |
| Varma et al. | MS excel functions as supply chain fraud detector | |
| Gatling et al. | Enterprise information management with SAP | |
| Bhat | UNLOCKING THE POWER OF DATA: THE CRITICAL ROLE OF MASTER DATA MANAGEMENT IN INSURANCE |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| 121 | Ep: the epo has been informed by wipo that ep was designated in this application |
Ref document number: 19859718 Country of ref document: EP Kind code of ref document: A1 |
|
| ENP | Entry into the national phase |
Ref document number: 2020545990 Country of ref document: JP Kind code of ref document: A |
|
| NENP | Non-entry into the national phase |
Ref country code: DE |
|
| ENP | Entry into the national phase |
Ref document number: 2019859718 Country of ref document: EP Effective date: 20210412 |
|
| WWW | Wipo information: withdrawn in national office |
Ref document number: 2019859718 Country of ref document: EP |