WO2021149632A1 - 携帯可能な認証デバイス、icカードおよび認証システム - Google Patents
携帯可能な認証デバイス、icカードおよび認証システム Download PDFInfo
- Publication number
- WO2021149632A1 WO2021149632A1 PCT/JP2021/001453 JP2021001453W WO2021149632A1 WO 2021149632 A1 WO2021149632 A1 WO 2021149632A1 JP 2021001453 W JP2021001453 W JP 2021001453W WO 2021149632 A1 WO2021149632 A1 WO 2021149632A1
- Authority
- WO
- WIPO (PCT)
- Prior art keywords
- card
- authentication
- registrant
- user
- information
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Ceased
Links
Images
Classifications
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/30—Authentication, i.e. establishing the identity or authorisation of security principals
- G06F21/31—User authentication
- G06F21/34—User authentication involving the use of external additional devices, e.g. dongles or smart cards
- G06F21/35—User authentication involving the use of external additional devices, e.g. dongles or smart cards communicating wirelessly
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/30—Authentication, i.e. establishing the identity or authorisation of security principals
- G06F21/31—User authentication
- G06F21/32—User authentication using biometric data, e.g. fingerprints, iris scans or voiceprints
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F21/00—Security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F21/30—Authentication, i.e. establishing the identity or authorisation of security principals
- G06F21/45—Structures or tools for the administration of authentication
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06K—GRAPHICAL DATA READING; PRESENTATION OF DATA; RECORD CARRIERS; HANDLING RECORD CARRIERS
- G06K19/00—Record carriers for use with machines and with at least a part designed to carry digital markings
- G06K19/06—Record carriers for use with machines and with at least a part designed to carry digital markings characterised by the kind of the digital marking, e.g. shape, nature, code
- G06K19/067—Record carriers with conductive marks, printed circuits or semiconductor circuit elements, e.g. credit or identity cards also with resonating or responding marks without active components
- G06K19/07—Record carriers with conductive marks, printed circuits or semiconductor circuit elements, e.g. credit or identity cards also with resonating or responding marks without active components with integrated circuit chips
- G06K19/0716—Record carriers with conductive marks, printed circuits or semiconductor circuit elements, e.g. credit or identity cards also with resonating or responding marks without active components with integrated circuit chips at least one of the integrated circuit chips comprising a sensor or an interface to a sensor
- G06K19/0718—Record carriers with conductive marks, printed circuits or semiconductor circuit elements, e.g. credit or identity cards also with resonating or responding marks without active components with integrated circuit chips at least one of the integrated circuit chips comprising a sensor or an interface to a sensor the sensor being of the biometric kind, e.g. fingerprint sensors
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06K—GRAPHICAL DATA READING; PRESENTATION OF DATA; RECORD CARRIERS; HANDLING RECORD CARRIERS
- G06K19/00—Record carriers for use with machines and with at least a part designed to carry digital markings
- G06K19/06—Record carriers for use with machines and with at least a part designed to carry digital markings characterised by the kind of the digital marking, e.g. shape, nature, code
- G06K19/067—Record carriers with conductive marks, printed circuits or semiconductor circuit elements, e.g. credit or identity cards also with resonating or responding marks without active components
- G06K19/07—Record carriers with conductive marks, printed circuits or semiconductor circuit elements, e.g. credit or identity cards also with resonating or responding marks without active components with integrated circuit chips
- G06K19/073—Special arrangements for circuits, e.g. for protecting identification code in memory
- G06K19/07309—Means for preventing undesired reading or writing from or onto record carriers
- G06K19/07345—Means for preventing undesired reading or writing from or onto record carriers by activating or deactivating at least a part of the circuit on the record carrier, e.g. ON/OFF switches
- G06K19/07354—Means for preventing undesired reading or writing from or onto record carriers by activating or deactivating at least a part of the circuit on the record carrier, e.g. ON/OFF switches by biometrically sensitive means, e.g. fingerprint sensitive
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q20/00—Payment architectures, schemes or protocols
- G06Q20/30—Payment architectures, schemes or protocols characterised by the use of specific devices or networks
- G06Q20/34—Payment architectures, schemes or protocols characterised by the use of specific devices or networks using cards, e.g. integrated circuit [IC] cards or magnetic cards
- G06Q20/341—Active cards, i.e. cards including their own processing means, e.g. including an IC or chip
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06Q—INFORMATION AND COMMUNICATION TECHNOLOGY [ICT] SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES; SYSTEMS OR METHODS SPECIALLY ADAPTED FOR ADMINISTRATIVE, COMMERCIAL, FINANCIAL, MANAGERIAL OR SUPERVISORY PURPOSES, NOT OTHERWISE PROVIDED FOR
- G06Q20/00—Payment architectures, schemes or protocols
- G06Q20/38—Payment protocols; Details thereof
- G06Q20/40—Authorisation, e.g. identification of payer or payee, verification of customer or shop credentials; Review and approval of payers, e.g. check credit lines or negative lists
- G06Q20/401—Transaction verification
- G06Q20/4014—Identity check for transactions
- G06Q20/40145—Biometric identity checks
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06V—IMAGE OR VIDEO RECOGNITION OR UNDERSTANDING
- G06V40/00—Recognition of biometric, human-related or animal-related patterns in image or video data
- G06V40/10—Human or animal bodies, e.g. vehicle occupants or pedestrians; Body parts, e.g. hands
- G06V40/12—Fingerprints or palmprints
- G06V40/13—Sensors therefor
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06V—IMAGE OR VIDEO RECOGNITION OR UNDERSTANDING
- G06V40/00—Recognition of biometric, human-related or animal-related patterns in image or video data
- G06V40/10—Human or animal bodies, e.g. vehicle occupants or pedestrians; Body parts, e.g. hands
- G06V40/12—Fingerprints or palmprints
- G06V40/1365—Matching; Classification
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06V—IMAGE OR VIDEO RECOGNITION OR UNDERSTANDING
- G06V40/00—Recognition of biometric, human-related or animal-related patterns in image or video data
- G06V40/50—Maintenance of biometric data or enrolment thereof
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06V—IMAGE OR VIDEO RECOGNITION OR UNDERSTANDING
- G06V40/00—Recognition of biometric, human-related or animal-related patterns in image or video data
- G06V40/50—Maintenance of biometric data or enrolment thereof
- G06V40/55—Performing matching on a personal external card, e.g. to avoid submitting reference information
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04W—WIRELESS COMMUNICATION NETWORKS
- H04W12/00—Security arrangements; Authentication; Protecting privacy or anonymity
- H04W12/40—Security arrangements using identity modules
- H04W12/47—Security arrangements using identity modules using near field communication [NFC] or radio frequency identification [RFID] modules
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F2221/00—Indexing scheme relating to security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F2221/21—Indexing scheme relating to G06F21/00 and subgroups addressing additional information or applications relating to security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F2221/2117—User registration
-
- G—PHYSICS
- G06—COMPUTING OR CALCULATING; COUNTING
- G06F—ELECTRIC DIGITAL DATA PROCESSING
- G06F2221/00—Indexing scheme relating to security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F2221/21—Indexing scheme relating to G06F21/00 and subgroups addressing additional information or applications relating to security arrangements for protecting computers, components thereof, programs or data against unauthorised activity
- G06F2221/2141—Access rights, e.g. capability lists, access control lists, access tables, access matrices
Definitions
- Embodiments of the present invention relate to a portable authentication device, an IC card and an authentication system.
- a usage-restricted device As a system for operating a device that needs to restrict users such as medical devices, the operation of the device (hereinafter referred to as a usage-restricted device) is performed only by a preset (designated) person or a qualified person. There is an authentication system to allow. In the conventional authentication system, when it is confirmed that the person is registered in a higher-level device such as a usage-restricted device or a server connected to the usage-restricted device, the use of the usage-restricted device is permitted.
- IC cards that perform fingerprint authentication have been put into practical use. With IC cards, biometric information can be managed securely, and biometric authentication with high security is realized. However, the conventional IC card only outputs the biometric information of the user and the result of biometric authentication with the registrant, and cannot confirm whether or not the registrant has the authority to use the device itself.
- a portable authentication device an IC card and an authentication system that can supply the result of biometric authentication of a person who has the authority to use the device to the device.
- the authentication device includes a sensor, a communication interface, a memory, and a processor.
- the sensor acquires biometric information.
- the communication interface communicates with the device.
- the memory stores feature point information (template) of the registrant's biometric information used for biometric authentication and management information indicating a device for which the registrant has usage authority.
- the processor authenticates whether the user who has acquired the biometric information is a registrant who has the authority to use the device communicating by the communication interface, and transmits the authentication result to the device communicating by the communication interface.
- FIG. 1 is a block diagram showing a configuration example of an IC card as a portable authentication device according to the embodiment and an authentication system including the IC card.
- FIG. 2 is a diagram showing a first configuration example of data held by the IC card according to the embodiment.
- FIG. 3 is a diagram showing a first configuration example of data held by the IC card according to the embodiment.
- FIG. 4 is a diagram showing a first configuration example of data held by the IC card according to the embodiment.
- FIG. 5 is a diagram showing a second configuration example of data held by the IC card according to the embodiment.
- FIG. 6 is a diagram showing a second configuration example of data held by the IC card according to the embodiment.
- FIG. 1 is a block diagram showing a configuration example of an IC card as a portable authentication device according to the embodiment and an authentication system including the IC card.
- FIG. 2 is a diagram showing a first configuration example of data held by the IC card according to the embodiment.
- FIG. 3 is a
- FIG. 7 is a diagram showing a second configuration example of data held by the IC card according to the embodiment.
- FIG. 8 is a diagram showing a third configuration example of data held by the IC card according to the embodiment.
- FIG. 9 is a timing chart showing an operation example of the IC card and the authentication system including the IC card according to the embodiment.
- FIG. 10 is a diagram showing a configuration example of data held by an IC card according to a modified example of the embodiment.
- the portable electronic device such as an IC card according to the embodiment is a portable authentication device that securely performs a person authentication process using biometric information acquired from a user.
- the IC card includes a fingerprint sensor as a biological sensor that acquires an image (fingerprint image) of a person's fingerprint, and performs an authentication process using the fingerprint image acquired by the fingerprint sensor.
- FIG. 1 shows a configuration example of the authentication system 10 including the IC card 2 according to the embodiment.
- the authentication system 10 is a system including an IC card 2 and a plurality of types of restricted use devices 1 (1A, 1B, 1C, ).
- the usage restriction device 1 is a device that is permitted to be used by a specific person.
- the usage restriction device 1 may be one that is permitted to be used by a preset person, or may be one that is permitted to be used by a person having a specific qualification.
- the usage restriction device 1 has a function of communicating with the IC card 2 as a portable authentication device.
- the usage restriction device 1 is a device that can be used by the person when it is authenticated by the IC card 2 that the person is permitted to use the own device.
- the usage restriction device 1 may be a medical device or the like that can be operated by a preset person, or may be a device that can be operated by a qualified person.
- the usage restriction device 1 includes a processor 11, a ROM 12, a RAM 13, a data memory 14, a reader / writer 15, and a processing unit 16.
- the processor 11 controls each part and executes various processes.
- the processor 11 is, for example, a CPU (central processing unit).
- the processor 11 realizes control of each part and various processes by executing a program stored in the ROM 11 or the data memory 14.
- the ROM 12 is a non-volatile memory for storing non-rewritable data.
- the ROM 12 stores a program, control data, or the like.
- the RAM 13 is a volatile memory that temporarily stores data.
- the data memory 14 is a rewritable non-volatile memory.
- the data memory 14 is realized by an HDD (hard disk drive data), an SSD (solid state drive), or the like.
- the reader / writer 15 is an interface for communicating with the IC card 2.
- the reader / writer 15 supplies power to the IC card 2, supplies clocks, resets, and sends / receives data.
- the reader / writer 15 is configured by an interface corresponding to the communication method of the IC card 2.
- the reader / writer 15 is composed of a contact portion for physically and electrically connecting to the contact portion of the IC card 2.
- the reader / writer 15 is composed of an antenna for wireless communication with the IC card 2, a communication control unit, and the like.
- the processing unit 16 executes processing when the use is permitted by the IC card 2.
- the processing unit 16 may execute processing when it is authenticated that the person is a preset person in the IC card 2, or is a person having a predetermined qualification in the IC card 2. May be executed when is authenticated.
- the processing unit 16 may include a processing mechanism for executing or assisting a medical practice, or is driven according to the operation of a person (qualified person) having a driving (operation) license. It may include a drive mechanism.
- the IC card 2 is a portable authentication device having a function of performing authentication by biometric information (biometric authentication).
- biometric authentication biometric authentication
- the IC card 2 operates by the electric power supplied from the reader / writer 15 of the usage restriction device 1, and executes the process according to the command from the reader / writer 15. Further, the IC card 2 supplies the reader / writer 15 with a response indicating the processing result for the command from the reader / writer 15.
- the IC card 2 has a card-shaped main body C made of plastic or the like.
- the IC card 2 has a module M and a biosensor (fingerprint sensor) 27 connected to the module M built in the main body C.
- the module M is integrally formed with the IC chip Ca, the communication interface 25, and the MPU 26 connected to each other, and is embedded in the main body C of the IC card 2.
- the IC chip Ca includes a processor 21, a ROM 22, a RAM 23, a data memory 24, and the like.
- the processor 21 connects to the ROM 22, the RAM 23, the data memory 24, the communication interface 25, and the MPU 26 via a data bus or the like.
- the MPU 26 is connected to the biosensor 27 via a data bus or the like.
- the IC card 2 may have a configuration as required in addition to the configuration shown in FIG. 1, or a specific configuration may be excluded from the IC card 2.
- the processor 21 functions as a control unit that controls the entire IC card 2.
- the processor 21 performs various processes based on the control program and the control data stored in the ROM 22 or the data memory 24.
- the processor 21 executes various processes according to the operation control of the IC card 2 or the operation mode of the IC card 2 by executing the program stored in the ROM 22.
- the processor 21 may be a processor that realizes control and information processing of each part in the IC card 2 by executing a program. It should be noted that some of the various functions realized by the processor 21 executing the program may be realized by the hardware circuit. In this case, the processor 21 controls the functions performed by the hardware circuits.
- ROM 22 is a non-volatile memory that stores control programs, control data, and the like in advance.
- the ROM 22 is incorporated in the IC card 2 in a state where the control program, control data, and the like are stored in the manufacturing stage.
- the control program and control data stored in the ROM 22 are incorporated in advance according to the specifications of the IC card 2.
- the RAM 23 is a volatile memory.
- the RAM 23 temporarily stores data and the like being processed by the processor 21.
- the RAM 23 functions as a calculation buffer, a reception buffer, and a transmission buffer.
- the calculation buffer temporarily holds the results of various arithmetic processes executed by the processor 21.
- the reception buffer holds command data and the like received from the reader / writer 15 via the communication interface 25.
- the transmission buffer holds a message (response data) or the like to be transmitted to the reader / writer 15 via the communication interface 25.
- the data memory 24 is composed of a non-volatile memory such as a flash ROM capable of writing and rewriting data.
- the data memory 24 stores a control program, an application, and various data according to the operational use of the IC card 2. For example, in the data memory 24, a program file, a data file, and the like are created. A control program and various data are written in each created file.
- the data memory 24 stores the feature point information (template) 24a of the biometric information obtained from the biometric information of the registrant as the dictionary data of the biometric (fingerprint) authentication.
- the feature point information 24a of the biological information is, for example, feature point information as a feature amount extracted from the biological information of the registrant.
- the data memory 24 stores feature point information 24a of biometric information for each registrant.
- the IC card 2 may register the feature point information 24a of biometric information for one specific registrant, or the feature point information 24a (24a1, 24a1) of a plurality of biometric information corresponding to a plurality of registrants. 24a2, 42a3, ...) may be registered.
- the data memory 24 has a management table 24b showing the usage restriction device 1 that can be used by the user (registrant).
- the management table 24b stores information indicating the relationship with the usage-restricted device that is permitted to be used by the registrant in which the feature point information 24a of the biological information is registered.
- the management table 24b may store data indicating the relationship between the registrant and the usage authority of the restricted use device.
- the management table 24b may store information indicating a usage-restricted device that can be used for each registrant, or may store information indicating a registrant who has usage authority for each usage-restricted device.
- Information indicating the association between a plurality of registrants and the usage authority of a plurality of restricted devices may be stored.
- the management table 24b may store the qualifications of the registrant and the usage authority of the usage-restricted device for various qualifications in association with each other.
- the communication interface 25 is an interface for transmitting and receiving data to and from the reader / writer 15. That is, the communication interface 25 is an interface for transmitting / receiving data to / from the restricted use device 1 through the reader / writer 15.
- the communication interface 25 is composed of a communication control unit and a contact unit for physically and electrically contacting the reader / writer 15 to transmit and receive signals.
- the IC card 2 is activated by receiving an operating power supply and an operating clock from the reader / writer 15 via the contact portion.
- the communication interface 25 is composed of a communication control unit such as a modulation / demodulation circuit for performing wireless communication with the reader / writer 15 and an antenna.
- a communication control unit such as a modulation / demodulation circuit for performing wireless communication with the reader / writer 15 and an antenna.
- the IC card 2 receives radio waves from the reader / writer 15 via an antenna, a modulation / demodulation circuit, and the like.
- the IC card 2 is activated by generating an operating power supply and an operating clock from the radio wave by a power supply unit (not shown).
- the biological sensor 27 acquires the biological information of the operator.
- the biosensor 27 is, for example, a fingerprint sensor.
- the fingerprint sensor as the biosensor 27 acquires a fingerprint image from the operator's finger.
- the fingerprint sensor as the biological sensor 27 includes a CCD sensor and the like. Further, the fingerprint sensor 27 may be provided with a sensor or the like that detects a change in the electric capacity.
- the fingerprint sensor 27 transmits a fingerprint image to the MPU 26.
- the biosensor 27 is assumed to be a fingerprint sensor, and the user's finger can be placed at the reading position of the fingerprint sensor in a state where the IC card 2 is set in the reader / writer 15 of the usage restriction device 1.
- the MPU 26 (Micro Processing Unit) processes the fingerprint image from the fingerprint sensor 27.
- the MPU 26 has a configuration including a processor, RAM, ROM, and the like.
- the process realized by the MPU 26 described in the present embodiment can be realized by the processor 21 in the IC chip Ca using the ROM 22, the RAM 23, and the like. Therefore, the process executed by the MPU 26 described below may be executed by the processor 21.
- the MPU 26 extracts feature point information (information indicating the coordinates of the feature points and the feature amount) from the fingerprint image from the fingerprint sensor 27.
- the MPU 26 transmits the extracted feature point information to the processor 21.
- the processor 21 may perform the process of extracting the feature point information from the fingerprint image acquired by the fingerprint sensor 27 as described above.
- the processor 21 collates the feature point information extracted from the fingerprint image acquired by the fingerprint sensor 27 transmitted from the MPU 26 with the feature point information of the fingerprint image registered in the data memory 24 or the like. For example, the processor 21 calculates the similarity between the feature point information extracted from the fingerprint image acquired by the fingerprint sensor 27 and the feature point information of the registered fingerprint image as the similarity between the fingerprint images according to a predetermined algorithm. do.
- the degree of similarity is an index indicating that the higher the degree of similarity, the higher the similarity between fingerprint images.
- the processor 21 reads and holds the feature point information of the fingerprint image registered in the data memory 24 or the like.
- the processor 21 collates the feature point information sent from the MPU 26 with the feature point information held in the processor 21 to calculate the similarity between the two.
- the processor 21 determines the success or failure of the authentication by comparing the calculated similarity with the threshold value for authentication as a collation process (authentication process). For example, if the calculated similarity is equal to or higher than the authentication threshold value, the processor 21 is regarded as the same person (authentication success), and if the similarity degree is less than the authentication threshold value, it is not recognized as the same person (authentication failure). By doing so, the result of the authentication process is obtained.
- the MPU 26 may perform the collation process between the fingerprint image acquired by the fingerprint sensor 27 and the registered fingerprint image. For example, the MPU 26 may calculate the similarity between the fingerprint image acquired by the fingerprint sensor 27 and the registered fingerprint image by the collation process, and transmit the calculated similarity to the processor 21. Further, the MPU 26 may transmit the success or failure of the authentication to the processor 21 by comparing the calculated similarity with the threshold value for the authentication.
- the IC card 2 may be provided with a display unit that displays various information according to the control from the processor 21.
- the display unit may be a light (for example, an LED (Light Emitting Diode) light) that lights up according to the control from the processor 21.
- the IC card 2 stores the feature point information 24a and the management table 24b of the biometric information for each registrant in the data memory 24.
- the IC card 2 may register the feature point information 24a of the biometric information of one registrant, or may register the feature point information 24a1, 24a2, ... Of the biometric information for a plurality of registrants. You may try to register.
- the management table 24b may store information indicating the relationship between the registrant and the usage-restricted device having the usage authority.
- the feature point information 24a and the management table 24b of the biometric information of the registrant registered in the IC card 2 as the portable authentication device according to the embodiment will be described.
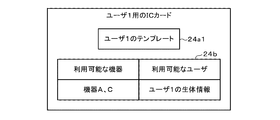
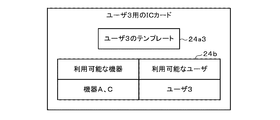
- FIG. 2 to 4 are diagrams showing a configuration example of the feature point information 24a and the management table 24b of the biometric information of the registrant in the IC card 2 issued for each individual user (registrant).
- FIG. 2 shows an example of the feature point information 24a and the management table 24b of the biometric information of the registrant in the IC card (IC card for the user 1) 2 issued to the user 1.
- FIG. 3 shows an example of the feature point information 24a and the management table 24b of the biometric information of the registrant in the IC card (IC card for the user 2) 2 issued to the user 2.
- FIG. 4 shows an example of the feature point information 24a and the management table 24b of the biometric information of the registrant in the IC card (IC card for the user 3) 2 issued to the user 3.
- the feature point information 24a of the biometric information of the registrant which is the dictionary data for biometric authentication of the user 1, and the use for which the user 1 has the usage authority.
- a management table 24b for storing information indicating the restricted device 1 is stored.
- the user 1 who can perform biometric authentication using the feature point information 24a of the biometric information of the registrant has the authority to use the device A and the device C.
- the data memory 24 of the IC card 2 contains the feature point information 24a of biometric information, which is the dictionary data for biometric authentication of the user 2, and the usage restriction device 1 to which the user 2 has the usage authority.
- a management table 24b for storing information indicating the above is stored. In the management table 24b shown in FIG. 3, it is shown that the user 2 who can perform biometric authentication using the feature point information 24a of the biometric information has the right to use the device B and the device C.
- the data memory 24 of the IC card 2 contains the feature point information 24a of biometric information, which is the dictionary data for biometric authentication of the user 3, and the usage restriction device 1 to which the user 3 has the usage authority.
- a management table 24b for storing information indicating the above is stored.
- the management table 24b shown in FIG. 3 it is shown that the user 3 who can perform biometric authentication using the feature point information 24a of the biometric information has the right to use the device A and the device C.
- the IC card 2 possessed by each user is provided with the feature point information 24a of the biometric information of the user who is the owner and the device that can be used by the user. Register the information to be shown.
- This makes it possible to provide an IC card 2 that can confirm not only biometric authentication for the registrant who is the owner but also the devices that can be used by the registrant (user).
- the feature point information 24a and the management table 24b of the registrant's biometric information as shown in FIGS.
- FIG. 5 to 7 are diagrams showing a configuration example of the feature point information 24a and the management table 24b of the registrant's biometric information in the IC card 2 issued for each use-restricted device.
- FIG. 5 shows an example of the feature point information 24a and the management table 24b of the registrant's biometric information in the IC card (IC card for the device A) 2 issued to the device A.
- FIG. 6 shows an example of the feature point information 24a and the management table 24b of the registrant's biometric information in the IC card (IC card for the device B) 2 issued to the device B.
- FIG. 7 shows an example of the feature point information 24a and the management table 24b of the registrant's biometric information in the IC card (IC card for the device C) 2 issued to the device C.
- the feature point information 24a1 of the biometric information of the user 1 who has the authority to use the device A and the feature point information 24a2 of the biometric information of the user 2 are stored in the data memory 24 of the device A.
- a management table 24b that stores information indicating a user who has usage authority is stored.
- the users who have the authority to use the device A are the user 1 of the feature point information 24a1 of the biometric information and the user 2 of the feature point information 24a2 of the biometric information.
- the data memory 24 of the IC card 2 stores information indicating the user who has the right to use the device B together with the feature point information 24a2 of the biometric information of the user 2 who has the right to use the device B.
- the management table 24b is stored. In the management table 24b shown in FIG. 6, it is shown that the user who has the authority to use the device B is the user 2 of the feature point information 24a2 of the biometric information.
- the data memory 24 of the IC card 2 contains the feature point information 24a1 of the biometric information of the user 1 who has the authority to use the device C, the feature point information 24a2 of the biometric information of the user 2, and the living body of the user 3.
- a management table 24b for storing information indicating a user who has the authority to use the device C is stored.
- the users who have the authority to use the device C are the user 1 of the feature point information 24a1 of the biometric information, the user 2 of the feature point information 24a2 of the biometric information, and the user of the feature point information 24a3 of the biometric information. It is shown to be 3.
- the IC card 2 issued (set) for each usage-restricted device contains the user who can use the usage-restricted device and the feature point information of the biometric information of each user. be registered.
- the feature point information 24a and the management table 24b of the registrant's biometric information as shown in FIGS. 5 to 7 are transferred to the IC card 2 for each device. By registering, it is possible to confirm the device used in the IC card 2 and biometric authentication of the user as described later.
- FIG. 8 is a diagram showing a configuration example of the feature point information 24a and the management table 24b of the registrant's biometric information in the IC card 2 issued to one system.
- FIG. 8 shows an example of the feature point information 24a and the management table 24b of the registrant's biometric information in the IC card (IC card for master) 2 issued to the entire system having the three devices A, B, and C. Is shown.
- the data memory 24 of the IC card 2 is provided with feature point information 24a1, 24a2, 24a3 of biometric information for three people and information indicating users who have usage authority for each of the three devices.
- the management table 24b to be stored is stored.
- the feature point information 24a1, 24a2, and 24a3 of the biometric information shown in FIG. 8 are dictionary data for biometric authentication of the user 1, the user 2, and the user 3, respectively. Further, in the management table 24b shown in FIG. 8, the users who have the usage authority of the device A are the user 1 and the user 2, the users who have the usage authority of the device B are the user 2, and the users have the usage authority of the device C. It is shown that the users are user 1, user 2, and user 3.
- the IC card 2 issued (set) to the entire system including the plurality of usage-restricted devices has the user who can use the usage-restricted device and the feature point information of the biometric information of each user. And are registered.
- the feature point information 24a and the management table 24b of the registrant's biometric information as shown in FIG. 8 are transferred to the IC card 2.
- the IC card having the configurations shown in FIGS. 2 to 4 and the configurations shown in FIGS. 5 to 7 are provided.
- An IC card and an IC card having the configuration shown in FIG. 8 may be issued respectively.
- the IC card for each user is issued. Even if a problem occurs or the IC card for each user is lost, it is possible to realize an operation in which the restricted device can be used with the master IC card.
- FIG. 9 is a timing chart for explaining an operation example of the authentication system 10 according to the embodiment.
- a user who intends to use a certain usage restriction device 1 sets an IC card 2 for biometric (fingerprint) authentication in a reader / writer 15 of the usage restriction device 1.
- the usage restriction device 1 supplies electric power for operation to the IC card 2 set in the reader / writer 15 (ST10).
- the IC card 2 is activated (activated) by receiving electric power supplied from the reader / writer 15 via the communication interface 25 (ST11).
- the processor 21 of the IC card 2 When the processor 21 of the IC card 2 is activated by the electric power from the reader / writer 15, the initial response is transmitted to the reader / writer 15.
- the reader / writer 15 supplies electric power for operation to the set IC card 2 and receives an initial response from the IC card 2.
- the reader / writer 15 Upon receiving the initial response, the reader / writer 15 performs mutual authentication with the IC card 2 to establish a communication state.
- the processor 11 of the usage-restricted device 1 transmits the device ID as the identification information of the usage-restricted device 1 and authenticates the user on the IC card 2. Is sent (ST12).
- the processor 21 of the IC card 2 registers the feature point information of the biometric information of the person who has the usage authority of the usage-restricted device 1 indicated by the received device ID in the IC card 2. (ST13).
- the processor 21 refers to the management table 24b and confirms whether or not the biometric information of the person who has the usage authority for the usage-restricted device of the device ID is registered, so that the usage-restricted device 1 is concerned.
- the IC card 2 is used to determine whether or not the device can be used (ST14).
- the processor 21 when the biometric information of a person who has the authority to use the device of the received device ID is registered, the processor 21 is assumed to be a device that can be used by the usage restriction device 1 in which the IC card 2 is set. Further, when the biometric information of the person who has the authority to use the device of the received device ID is not registered, the processor 21 is assumed to be a device in which the usage restriction device 1 in which the IC card 2 is set cannot be used.
- the processor 21 uses the fact that the restricted device 1 is an unusable device. Respond to restriction device 1 (ST20). In this case, the usage-restricted device 1 in which the IC card 2 is set is in a state in which the processing unit 16 cannot execute the process in response to the response that the device cannot be used as described above.
- the processor 21 activates the fingerprint sensor 27 as a biosensor through the MPU 26, and the fingerprint sensor 27 Acquires a fingerprint image as biometric information of the user (ST15).
- the user assumes that the finger having the fingerprint used for authentication is placed at the reading position of the fingerprint sensor 27.
- the MPU 26 may detect that a finger is placed at the reading position of the fingerprint sensor 27 and read the fingerprint image by the fingerprint sensor 27.
- the processor 21 and the MPU 26 perform biometric (fingerprint) authentication using the acquired fingerprint image (ST16).
- the MPU 26 extracts feature point information from the fingerprint image acquired by the fingerprint sensor 27, and transmits the extracted feature point information to the processor 21.
- the processor 21 acquires the feature point information of the user's fingerprint image read by the fingerprint sensor 27 from the MPU 26.
- the processor 21 collates the feature point information of the acquired user's fingerprint image with the feature point information of the registrant's fingerprint image registered in the data memory 24.
- the processor 21 calculates the similarity between the feature point information of the fingerprint image of the user and the feature point information of the fingerprint image of the registrant, and the user is the registrant depending on whether or not the calculated similarity is equal to or higher than the threshold for authentication. It is determined whether or not it is.
- the processor 21 uses the restricted device 1 in which the user (that is, the registrant) matching the registrant is indicated by the device ID. It is determined whether or not the user has the right to use the user (ST17).
- the processor 21 uses the usage-restricted device 1 in which the user who puts his / her finger on the fingerprint sensor 27 is indicated by the device ID.
- the communication interface 25 responds to the reader / writer 15 of the usage restriction device 1 that the registrant who can use the user is authenticated (ST18).
- the processor 11 of the usage restriction device 1 When the IC card 2 receives a response that the user has been authenticated by the reader / writer 15, the processor 11 of the usage restriction device 1 permits the operation of the processing unit 16 and the processing requested by the user. Is in an executable state (ST19). In this case, the processor 11 of the usage restriction device 1 records in the memory 14 the history information indicating the usage content executed by the user together with the information indicating the user who is permitted to use the IC card 2 based on the authentication result (ST20). ..
- the processor 21 cannot confirm that the user has the usage authority, or , The fact that the usage-restricted device 1 is unavailable is used as a response to the usage-restricted device 1 (ST21).
- the processor 11 of the usage restriction device 1 When the IC card 2 receives a response that the user cannot be authenticated as a registrant or that the usage restriction device 1 is an unusable device, the processor 11 of the usage restriction device 1 is a processing unit. The operation of 16 is disabled, and the user cannot use the usage-restricted device 1 (ST22). In this case, the processor 11 of the usage restriction device 1 may record in the memory 14 the history information indicating that the use is disabled due to the result of the authentication in the IC card 2.
- the registrant registered in the IC card is the usage-restricted device. It is confirmed whether or not the user has the right to use the device, and whether or not the user is a registrant who has the right to use the restricted device is confirmed by biometric authentication acquired by the biometric sensor.
- the IC card can be prevented from being used by a person who does not have the usage authority, and the user has the usage authority by biometric authentication. It can be confirmed that the person has. As a result, the IC card can surely confirm the use of the device and prevent spoofing by biometric authentication, so that it is possible to surely use the device whose use is restricted by a person who has the authority to use the IC card.
- the IC card confirms the user's usage authority for the device and the registrant (patient or identification) for which the user has the usage authority. Operator) Performs biometric authentication to confirm the identity of the patient with biometric information.
- the IC card can be allowed to perform medical treatment by the restricted device when the biometric authentication with the person who has the authority to use the restricted device is successful, and the IC card can be associated with the registrant. It is possible to ensure that medical treatment is provided by the correct usage restriction device.
- the management table 24b of the IC card 2 stores information indicating the qualification possessed by the registrant and information indicating the qualification that the use of each usage-restricted device is permitted.
- an example of confirming whether or not the use-restricted device can be used based on the qualification possessed by the user will be described.
- the configurations other than the management table 24b can be realized by the same configurations as those in the above-described embodiment, detailed description thereof will be omitted.
- FIG. 10 is a diagram showing a configuration example of the feature point information 24a and the management table 24b of the biometric information of the registrant in the IC card 2 when confirming the usage authority of the usage-restricted device based on the qualification information.
- the data memory 24 of the IC card 2 includes a management table 24b including feature point information 24a1, 24a2, 24a3 of biometric information for three people, and a first table 24b1 and a second table 24b2. Is memorized.
- the first table 24b1 stores information indicating qualifications required when using each usage-restricted device (devices A, B, C).
- the second table 24b2 stores information indicating the qualifications of each registrant (users 1, 2, 3).
- the processor 21 of the IC card 2 shown in FIG. 10 can identify that the user 1 and the user 3 have the right to use the device A by referring to the management table 24b.
- the device B can determine from the first table 24b1 that the qualification required for use is ⁇ , and can determine from the second table 24b2 that the user having the qualification ⁇ is the user 2. That is, the processor 21 of the IC card 2 shown in FIG. 10 can identify that the user 2 has the right to use the device B by referring to the management table 24b.
- the processor 21 of the IC card 2 shown in FIG. 10 can identify that the users 1, 2, and 3 have the right to use the device C by referring to the management table 24b.
- the authentication system according to the modified example can realize the same processing in the same flow as the processing shown in FIG. 9 described above.
- the processing of ST13 in FIG. 9 is a device that can be used by the usage restriction device in which the IC card is set by referring to the information registered in the management table 24b as shown in FIG. It should be confirmed based on the qualification of the registrant.
- the processing of ST13 in FIG. 9 is a device that can be used by the usage restriction device in which the IC card is set by referring to the information registered in the management table 24b as shown in FIG. It should be confirmed based on the qualification of the registrant.
- an IC card as a portable authentication device that can confirm the users who can use each device based on the qualifications of each registrant. Can be provided.
Landscapes
- Engineering & Computer Science (AREA)
- Theoretical Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Computer Hardware Design (AREA)
- General Engineering & Computer Science (AREA)
- Business, Economics & Management (AREA)
- Software Systems (AREA)
- Microelectronics & Electronic Packaging (AREA)
- Multimedia (AREA)
- Human Computer Interaction (AREA)
- Computer Networks & Wireless Communication (AREA)
- Accounting & Taxation (AREA)
- Strategic Management (AREA)
- General Business, Economics & Management (AREA)
- Automation & Control Theory (AREA)
- Finance (AREA)
- Signal Processing (AREA)
- Collating Specific Patterns (AREA)
- Financial Or Insurance-Related Operations Such As Payment And Settlement (AREA)
- Credit Cards Or The Like (AREA)
Abstract
Description
実施形態に係るICカードなどの携帯可能電子装置は、ユーザから取得する生体情報を用いてセキュアに人物の認証処理を行う携帯可能な認証デバイスである。本実施形態において、ICカードは、人物の指紋の画像(指紋画像)を取得する生体センサとしての指紋センサを具備し、指紋センサで取得する指紋画像を用いて認証処理を行う。
図1が示すように、認証システム10は、ICカード2と複数種類の利用制限機器1(1A、1B、1C、…)とを含むシステムである。利用制限機器1は、特定の人物に対して利用が許可される機器である。例えば、利用制限機器1は、予め設定した人物に対して利用が許可されるものであっても良いし、特定の資格を有する人物に対して利用が許可されるものであっても良い。
図1に示す構成例において、利用制限機器1は、プロセッサ11、ROM12、RAM13、データメモリ14、リーダライタ15および処理部16を有する。
プロセッサ11は、各部の制御および各種の処理などを実行する。プロセッサ11は、例えば、CPU(central processing unit)である。プロセッサ11は、ROM11またはデータメモリ14に記憶されたプログラムを実行することにより各部の制御および各種の処理を実現する。
データメモリ14は、書き換え可能な不揮発性のメモリである。データメモリ14は、HDD(ハードディスクドライブデータ)あるいはSSD(ソリッドステートドライブ)などで実現される。
ICカード2は、生体情報による認証(生体認証)を実行する機能を有する携帯可能な認証デバイスである。実施形態に係る認証システムにおいて、ICカード2は、利用制限機器1のリーダライタ15から供給される電力によって動作し、リーダライタ15からのコマンドに従って処理を実行する。また、ICカード2は、リーダライタ15からのコマンドに対する処理結果を示すレスポンスをリーダライタ15へ供給する。
なお、ICカード2は、図1が示すような構成の他に必要に応じた構成を具備したり、ICカード2から特定の構成が除外されたりしてもよい。
なお、プロセッサ21がプログラムを実行することにより実現する各種の機能のうちの一部は、ハードウエア回路により実現されるものであっても良い。この場合、プロセッサ21は、ハードウエア回路により実行される機能を制御する。
以下、本実施形態では、一例としてICカード2が接触型のICカードである場合を想定して説明するものとするが、ICカード2が非接触型のICカードであっても同様に実現可能なものである。また、生体センサ27は、指紋センサであるものとし、ICカード2が利用制限機器1のリーダライタ15にセットされた状態でユーザの指が指紋センサの読取位置に置けるようにするものとする。
プロセッサ21は、データメモリ24などに登録されている指紋画像の特徴点情報を読み込んで保持する。プロセッサ21は、MPU26から送られる特徴点情報とプロセッサ21内に保持した特徴点情報とを照合して両者の類似度を算出する。
類似度を算出すると、プロセッサ21は、照合処理(認証処理)として、算出した類似度と認証用の閾値とを比較することにより認証の成否を判定する。例えば、プロセッサ21は、算出した類似度が認証用の閾値以上であれば同一人物である(認証成功)とし、類似度が認証用の閾値未満であれば同一人物と認めない(認証失敗)とすることにより認証処理の結果を得る。
上述した構成例によれば、ICカード2は、データメモリ24において、登録者ごとの生体情報の特徴点情報24aと管理テーブル24bと記憶する。上述したように、ICカード2は、1人の登録者の生体情報の特徴点情報24aを登録するようにしても良いし、複数の登録者に対する生体情報の特徴点情報24a1、24a2、…を登録するようにしても良い。また、管理テーブル24bは、登録者と利用権限を有する利用制限機器との関係を示す情報を記憶するものであれば良い。
図2は、ユーザ1に対して発行されるICカード(ユーザ1用のICカード)2における登録者の生体情報の特徴点情報24aと管理テーブル24bとの例を示す。図3は、ユーザ2に対して発行されるICカード(ユーザ2用のICカード)2における登録者の生体情報の特徴点情報24aと管理テーブル24bとの例を示す。図4は、ユーザ3に対して発行されるICカード(ユーザ3用のICカード)2における登録者の生体情報の特徴点情報24aと管理テーブル24bとの例を示す。
図5は、機器Aに対して発行されるICカード(機器A用のICカード)2における登録者の生体情報の特徴点情報24aと管理テーブル24bとの例を示す。図6は、機器Bに対して発行されるICカード(機器B用のICカード)2における登録者の生体情報の特徴点情報24aと管理テーブル24bとの例を示す。図7は、機器Cに対して発行されるICカード(機器C用のICカード)2における登録者の生体情報の特徴点情報24aと管理テーブル24bとの例を示す。
図8は、3つの機器A、B、Cを有するシステム全体に対して発行されるICカード(マスタ用のICカード)2における登録者の生体情報の特徴点情報24aと管理テーブル24bとの例を示す。
図8に示す例において、ICカード2のデータメモリ24には、3人分の生体情報の特徴点情報24a1、24a2、24a3と、3つの各機器に対して利用権限を有するユーザを示す情報を格納する管理テーブル24bとが記憶される。
図9は、実施形態に係る認証システム10の動作例について説明するためのタイミングチャートである。
ある利用制限機器1を利用しようとするユーザは、生体(指紋)認証を行うICカード2を利用制限機器1のリーダライタ15にセットする。利用制限機器1は、リーダライタ15にセットされたICカード2へ動作用の電力を供給する(ST10)。ICカード2は、通信インターフェース25を介してリーダライタ15から供給される電力を受けて活性化(起動)する(ST11)。
上述した実施形態では、ICカードに生体情報の特徴点情報が登録されている登録者が機器IDで特定される機器の利用権限を有するか否かを確認したが、機器IDで特定される機器を利用する資格を登録者が有しているか否かを確認するようにしても良い。この場合、ICカード2の管理テーブル24bには、登録者が有する資格を示す情報と各利用制限機器の利用が許可される資格を示す情報とが記憶される。
以下、上述した実施形態の変形例として、ユーザが有する資格に基づいて利用制限機器が利用可能な否かを確認する例について説明する。
なお、変形例に係る認証システム10は、管理テーブル24b以外の構成は上述した実施形態と同様な構成で実現できるため、詳細な説明を省略するものとする。
図10に示す構成例において、ICカード2のデータメモリ24には、3人分の生体情報の特徴点情報24a1、24a2、24a3と、第1テーブル24b1および第2テーブル24b2からなる管理テーブル24bとが記憶される。第1テーブル24b1は、各利用制限機器(機器A、B、C)を利用する場合に必要な資格を示す情報が格納される。第2テーブル24b2は、各登録者(ユーザ1、2、3)が有する資格を示す情報が格納される。
以上のような変形例によれば、複数の登録者に対する生体認証だけでなく、各登録者が有する資格に基づいて各機器が利用可能なユーザを確認できる携帯可能な認証デバイスとしてのICカードを提供できる。
Claims (7)
- 生体情報を取得するセンサと、
機器と通信する通信インターフェースと、
生体認証に用いる登録者の生体情報の特徴点情報と前記登録者が利用権限を有する機器を示す管理情報とを記憶するメモリと、
前記センサが生体情報を取得したユーザが前記通信インターフェースにより通信する機器の利用権限を有する前記登録者であるかを認証し、前記認証の結果を前記通信インターフェースにより通信する前記機器へ送信するプロセッサと、
を備える携帯可能な認証デバイス。 - 前記メモリは、特定の登録者の生体情報の特徴点情報と、前記特定の登録者に利用権限が与えられている機器を示す管理情報と、を記憶する、
請求項1に記載の携帯可能な認証デバイス。 - 前記メモリは、複数の登録者の生体情報の特徴点情報と、特定の機器に対して利用権限を有する登録者を示す管理情報と、を記憶する、
請求項1に記載の携帯可能な認証デバイス。 - 前記メモリは、複数の登録者の生体情報の特徴点情報と、複数の機器に対して利用権限を有する登録者を示す管理情報と、を記憶する、
請求項1に記載の携帯可能な認証デバイス。 - 前記センサは、生体情報としての指紋画像を取得する指紋センサである、
請求項1乃至4の何れか1項に記載の携帯可能な認証デバイス。 - 指紋情報を取得する指紋センサと、
機器と通信する通信インターフェースと、指紋認証に用いる登録者の指紋画像の特徴点情報と前記登録者が利用権限を有する機器を示す管理情報とを記憶するメモリと、前記指紋センサが指紋情報を取得したユーザが前記通信インターフェースにより通信する機器の利用権限を有する前記登録者であるかを認証し、前記認証の結果を前記通信インターフェースにより通信する前記機器へ送信するプロセッサと、を備えるモジュールと、
前記指紋センサと前記モジュールとを接続した状態を内蔵した本体と、
を備えるICカード。 - 利用制限機器と携帯可能な認証デバイスとを有する認証システムであって、
前記利用制限機器は、
前記携帯可能な認証デバイスと通信するリーダライタと、
前記リーダライタを介して通信する前記携帯可能な認証デバイスにユーザが利用権限を有する人物であるかの認証を要求し、前記携帯可能な認証デバイスによる認証結果に応じて当該利用制限機器の動作を制限するプロセッサと、を備え、
前記携帯可能な認証デバイスは、
生体情報を取得するセンサと、
前記利用制限機器と通信する通信インターフェースと、
生体認証に用いる登録者の生体情報の特徴点情報と前記登録者が利用権限を有する機器を示す管理情報とを記憶するメモリと、
前記センサが生体情報を取得したユーザが前記通信インターフェースにより通信する前記利用制限機器の利用権限を有する前記登録者であるかを認証し、前記認証の結果を前記通信インターフェースにより通信する前記利用制限機器へ送信するプロセッサと、を備える、
認証システム。
Priority Applications (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| EP21744137.7A EP4095751A4 (en) | 2020-01-20 | 2021-01-18 | PORTABLE AUTHENTICATION DEVICE, IC CARD AND AUTHENTICATION SYSTEM |
| US17/867,936 US20220350873A1 (en) | 2020-01-20 | 2022-07-19 | Portable authentication device, ic card and authentication system |
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| JP2020006637A JP7414545B2 (ja) | 2020-01-20 | 2020-01-20 | 携帯可能な認証デバイス、icカードおよび認証システム |
| JP2020-006637 | 2020-01-20 |
Related Child Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| US17/867,936 Continuation US20220350873A1 (en) | 2020-01-20 | 2022-07-19 | Portable authentication device, ic card and authentication system |
Publications (1)
| Publication Number | Publication Date |
|---|---|
| WO2021149632A1 true WO2021149632A1 (ja) | 2021-07-29 |
Family
ID=76992387
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| PCT/JP2021/001453 Ceased WO2021149632A1 (ja) | 2020-01-20 | 2021-01-18 | 携帯可能な認証デバイス、icカードおよび認証システム |
Country Status (4)
| Country | Link |
|---|---|
| US (1) | US20220350873A1 (ja) |
| EP (1) | EP4095751A4 (ja) |
| JP (1) | JP7414545B2 (ja) |
| WO (1) | WO2021149632A1 (ja) |
Families Citing this family (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JP7399727B2 (ja) * | 2020-01-30 | 2023-12-18 | 株式会社東芝 | 認証デバイスおよび認証システム |
| US12367269B2 (en) * | 2022-09-14 | 2025-07-22 | Capital One Services, Llc | Biometric authentication-based token |
Citations (6)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JPH11134302A (ja) | 1997-10-31 | 1999-05-21 | Mitsubishi Electric Corp | 端末のアクセス制御装置および認証カード |
| JP2010286936A (ja) * | 2009-06-10 | 2010-12-24 | Hitachi Ltd | 半導体素子および認証装置、認証システム |
| US20150178489A1 (en) * | 2013-12-20 | 2015-06-25 | Orange | Method of authentication of at least one user with respect to at least one electronic apparatus, and a device therefor |
| WO2016035402A1 (ja) * | 2014-09-02 | 2016-03-10 | Necソリューションイノベータ株式会社 | 認証装置、認証システム、認証方法及びプログラム |
| JP2016115098A (ja) * | 2014-12-15 | 2016-06-23 | 株式会社MoriX | 指紋認証付スマートカードとこれを用いた決済方法 |
| JP2018018324A (ja) * | 2016-07-28 | 2018-02-01 | 株式会社東芝 | Icカードおよび携帯可能電子装置 |
Family Cites Families (9)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JP4285368B2 (ja) * | 2004-08-25 | 2009-06-24 | セイコーエプソン株式会社 | Icカード、認証システムおよび認証方法 |
| WO2008041286A1 (en) * | 2006-09-29 | 2008-04-10 | Fujitsu Limited | Information processor and information management method |
| KR20160072682A (ko) * | 2014-12-15 | 2016-06-23 | 삼성전자주식회사 | 생체 정보를 이용한 인증 방법 및 이를 위한 전자 장치 |
| WO2017008013A1 (en) * | 2015-07-09 | 2017-01-12 | Mastercard International Incorporated | Systems and methods for use in authenticating individuals, in connection with providing access to the individuals |
| JP2018005271A (ja) * | 2016-06-27 | 2018-01-11 | 株式会社東芝 | サーバ、icカード処理装置、および、icカード処理システム |
| JP2018005272A (ja) * | 2016-06-27 | 2018-01-11 | 株式会社東芝 | Icカード、携帯可能電子装置、及びicカードの制御方法 |
| JP2018045330A (ja) * | 2016-09-12 | 2018-03-22 | 株式会社東芝 | Icカード及び携帯可能電子装置 |
| JP6946031B2 (ja) * | 2017-03-22 | 2021-10-06 | 株式会社東芝 | Icカード、およびicカードの制御方法 |
| US20200026829A1 (en) * | 2018-07-17 | 2020-01-23 | Sensormatic Electronics, LLC | Biometric access control identification card |
-
2020
- 2020-01-20 JP JP2020006637A patent/JP7414545B2/ja active Active
-
2021
- 2021-01-18 WO PCT/JP2021/001453 patent/WO2021149632A1/ja not_active Ceased
- 2021-01-18 EP EP21744137.7A patent/EP4095751A4/en not_active Withdrawn
-
2022
- 2022-07-19 US US17/867,936 patent/US20220350873A1/en active Pending
Patent Citations (6)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| JPH11134302A (ja) | 1997-10-31 | 1999-05-21 | Mitsubishi Electric Corp | 端末のアクセス制御装置および認証カード |
| JP2010286936A (ja) * | 2009-06-10 | 2010-12-24 | Hitachi Ltd | 半導体素子および認証装置、認証システム |
| US20150178489A1 (en) * | 2013-12-20 | 2015-06-25 | Orange | Method of authentication of at least one user with respect to at least one electronic apparatus, and a device therefor |
| WO2016035402A1 (ja) * | 2014-09-02 | 2016-03-10 | Necソリューションイノベータ株式会社 | 認証装置、認証システム、認証方法及びプログラム |
| JP2016115098A (ja) * | 2014-12-15 | 2016-06-23 | 株式会社MoriX | 指紋認証付スマートカードとこれを用いた決済方法 |
| JP2018018324A (ja) * | 2016-07-28 | 2018-02-01 | 株式会社東芝 | Icカードおよび携帯可能電子装置 |
Non-Patent Citations (1)
| Title |
|---|
| See also references of EP4095751A4 |
Also Published As
| Publication number | Publication date |
|---|---|
| EP4095751A4 (en) | 2024-01-24 |
| JP7414545B2 (ja) | 2024-01-16 |
| EP4095751A1 (en) | 2022-11-30 |
| US20220350873A1 (en) | 2022-11-03 |
| JP2021114145A (ja) | 2021-08-05 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN100437635C (zh) | 安全的生物身份验证 | |
| JP4673065B2 (ja) | アイデンティティの秘密保護された生物測定学的検査 | |
| US20080296371A1 (en) | Method of activating a fingerprint identification process of a smart card according to a given condition and a device thereof | |
| US10528857B2 (en) | IC card, portable electronic device, and information processing method | |
| US20190180018A1 (en) | Portable electronic device | |
| EP1759337A1 (en) | Smart card for passport, electronic passport, and method, system, and apparatus for authenticating person holding smart card or electronic passport | |
| EP3657368B1 (en) | Ic card, portable electronic device, ic card processing method and program | |
| US20180189773A1 (en) | Multifunction card including biometric data, card payment terminal, and card payment system | |
| CN101268479A (zh) | 生物统计激活的射频识别标签 | |
| JP2007522580A (ja) | 無線データ転送をするためのポータブルデータキャリア、外部装置、システムおよび方法 | |
| US20220350873A1 (en) | Portable authentication device, ic card and authentication system | |
| US10523669B2 (en) | Server, IC card processing apparatus, and IC card processing system | |
| US20240214207A1 (en) | Information management system, authentication device, and personal information server | |
| JP4089294B2 (ja) | 個人認証システム及び個人認証用端末装置 | |
| US20230214474A1 (en) | Portable electronic device and ic card | |
| JP2022143852A (ja) | リモート発行システムおよびデータ生成サーバ | |
| JP2023044913A (ja) | 携帯可能電子装置、icカードおよびデータ開示設定用のプログラム | |
| JP2006163492A (ja) | 決済システム | |
| JP2006268570A (ja) | セキュリティカード及びセキュリティカードシステム | |
| US20240048554A1 (en) | Remote issuance system and data generation server | |
| JP2004110365A (ja) | Icカード及びicカード更新方法 | |
| WO2026053591A1 (ja) | セキュリティシステムおよびセキュリティデバイスの使用方法 | |
| JP2022000729A (ja) | Icカード及び携帯可能電子装置 | |
| JP4516038B2 (ja) | 情報処理装置及び無線入力装置の認証方法 | |
| JP2022145432A (ja) | リモート発行システムおよびデータ生成サーバ |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| 121 | Ep: the epo has been informed by wipo that ep was designated in this application |
Ref document number: 21744137 Country of ref document: EP Kind code of ref document: A1 |
|
| NENP | Non-entry into the national phase |
Ref country code: DE |
|
| ENP | Entry into the national phase |
Ref document number: 2021744137 Country of ref document: EP Effective date: 20220822 |
|
| WWW | Wipo information: withdrawn in national office |
Ref document number: 2021744137 Country of ref document: EP |
|
| WWG | Wipo information: grant in national office |
Ref document number: 11202251337W Country of ref document: SG |
|
| WWP | Wipo information: published in national office |
Ref document number: 11202251337W Country of ref document: SG |