CN115242514B - Method, system, electronic device, and storage medium for seeking intersection of private sets based on national secrets - Google Patents
Method, system, electronic device, and storage medium for seeking intersection of private sets based on national secrets Download PDFInfo
- Publication number
- CN115242514B CN115242514B CN202210876365.5A CN202210876365A CN115242514B CN 115242514 B CN115242514 B CN 115242514B CN 202210876365 A CN202210876365 A CN 202210876365A CN 115242514 B CN115242514 B CN 115242514B
- Authority
- CN
- China
- Prior art keywords
- ciphertext
- party
- random number
- public key
- local data
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Active
Links
Images
Classifications
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L63/00—Network architectures or network communication protocols for network security
- H04L63/04—Network architectures or network communication protocols for network security for providing a confidential data exchange among entities communicating through data packet networks
- H04L63/0428—Network architectures or network communication protocols for network security for providing a confidential data exchange among entities communicating through data packet networks wherein the data content is protected, e.g. by encrypting or encapsulating the payload
- H04L63/045—Network architectures or network communication protocols for network security for providing a confidential data exchange among entities communicating through data packet networks wherein the data content is protected, e.g. by encrypting or encapsulating the payload wherein the sending and receiving network entities apply hybrid encryption, i.e. combination of symmetric and asymmetric encryption
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/08—Key distribution or management, e.g. generation, sharing or updating, of cryptographic keys or passwords
- H04L9/0861—Generation of secret information including derivation or calculation of cryptographic keys or passwords
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/14—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols using a plurality of keys or algorithms
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/30—Public key, i.e. encryption algorithm being computationally infeasible to invert or user's encryption keys not requiring secrecy
- H04L9/3066—Public key, i.e. encryption algorithm being computationally infeasible to invert or user's encryption keys not requiring secrecy involving algebraic varieties, e.g. elliptic or hyper-elliptic curves
-
- H—ELECTRICITY
- H04—ELECTRIC COMMUNICATION TECHNIQUE
- H04L—TRANSMISSION OF DIGITAL INFORMATION, e.g. TELEGRAPHIC COMMUNICATION
- H04L9/00—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols
- H04L9/32—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials
- H04L9/3236—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials using cryptographic hash functions
- H04L9/3239—Cryptographic mechanisms or cryptographic arrangements for secret or secure communications; Network security protocols including means for verifying the identity or authority of a user of the system or for message authentication, e.g. authorization, entity authentication, data integrity or data verification, non-repudiation, key authentication or verification of credentials using cryptographic hash functions involving non-keyed hash functions, e.g. modification detection codes [MDCs], MD5, SHA or RIPEMD
Landscapes
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Computer Networks & Wireless Communication (AREA)
- Signal Processing (AREA)
- Theoretical Computer Science (AREA)
- Computing Systems (AREA)
- Physics & Mathematics (AREA)
- Mathematical Analysis (AREA)
- Mathematical Optimization (AREA)
- Mathematical Physics (AREA)
- Pure & Applied Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Algebra (AREA)
- Computer Hardware Design (AREA)
- General Engineering & Computer Science (AREA)
- Storage Device Security (AREA)
Abstract
本申请实施例公开了一种基于国密的隐私集合求交方法、系统、电子设备及存储介质,所述方法包括:生成第一国密算法的第一公钥、第一私钥、第一随机数、第二公钥、第二私钥和第二随机数;利用第二国密算法、第一公钥、第一随机数对第一本地数据进行加密,得到第一密文;利用第二国密算法、第二公钥、第二随机数对第二本地数据进行加密,得到第二密文;提取第一密文中的第一部分密文和第二部分密文;提取第二密文中的第三部分密文和第四部分密文,通过第二公钥和第二随机数对第一部分密文进行加密并提取部分密文,得到目标第一部分密文;根据第三部分密文、目标第一部分密文和第二部分密文求交,得到交集结果。采用本申请实施例可扩充国密算法应用场景。
The embodiment of the present application discloses a method, system, electronic device, and storage medium for calculating the intersection of privacy sets based on national secrets. The method includes: generating the first public key, the first private key, the first random number, second public key, second private key, and second random number; use the second national secret algorithm, the first public key, and the first random number to encrypt the first local data to obtain the first ciphertext; use the second Encrypt the second local data with the second national encryption algorithm, the second public key, and the second random number to obtain the second ciphertext; extract the first part of the ciphertext and the second part of the ciphertext in the first ciphertext; extract the second part of the ciphertext The third part of the ciphertext and the fourth part of the ciphertext, the first part of the ciphertext is encrypted by the second public key and the second random number and part of the ciphertext is extracted to obtain the target first part of the ciphertext; according to the third part of the ciphertext, The first part of the ciphertext and the second part of the ciphertext are intersected to obtain the intersection result. The application scenarios of the national secret algorithm can be expanded by adopting the embodiment of the present application.
Description
技术领域technical field
本申请涉及隐私计算技术领域以及计算机技术领域,具体涉及一种基于国密的隐私集合求交方法、系统、电子设备及存储介质。The present application relates to the technical field of privacy computing and the field of computer technology, and in particular to a method, system, electronic device and storage medium for solving a privacy set based on national secrets.
背景技术Background technique
随着人工智能的发展,数据的价值越来越受到重视。隐私集合求交(private setintersection,PSI)是指参与方在不泄露额外信息的前提下,得到各自持有数据的交集,是隐私计算领域一个重要技术,在隐私保护的实名认证、联合风控、数据探查等领域具有良好的应用前景。With the development of artificial intelligence, the value of data is getting more and more attention. Private set intersection (private setintersection, PSI) means that the participants obtain the intersection of their own data without disclosing additional information. It is an important technology in the field of privacy computing. Fields such as data exploration have good application prospects.
目前的隐私集合求交技术鲜有采用国密的方案,这使得PSI技术在一些安全性和自主可控性要求较高的场景无法适用,如涉及大型银行,国家机关等的合作场景。The current privacy set intersection technology rarely adopts national secret solutions, which makes PSI technology unsuitable for some scenarios that require high security and autonomous controllability, such as cooperation scenarios involving large banks and state agencies.
发明内容Contents of the invention
本申请实施例提供了一种基于国密的隐私集合求交方法、系统、电子设备及存储介质,可以扩充国密算法的应用场景。The embodiment of the present application provides a method, system, electronic device, and storage medium for calculating a private set intersection based on national secrets, which can expand the application scenarios of national secret algorithms.
第一方面,本申请实施例提供一种基于国密的隐私集合求交方法,应用于两方计算系统,所述两方计算系统包括第一方和第二方,所述第一方对应第一本地数据,所述第二方对应第二本地数据;所述方法包括:In the first aspect, the embodiment of the present application provides a privacy set intersection method based on national secrets, which is applied to a two-party computing system. The two-party computing system includes a first party and a second party, and the first party corresponds to the second party. A local data, the second party corresponds to the second local data; the method includes:
通过所述第一方生成第一国密算法的加解密处理参数,得到第一公钥、第一私钥和第一随机数;Generate the encryption and decryption processing parameters of the first national secret algorithm by the first party to obtain the first public key, the first private key and the first random number;
通过所述第二方生成所述第一国密算法的加解密处理参数,得到第二公钥、第二私钥和第二随机数;generating encryption and decryption processing parameters of the first national secret algorithm by the second party to obtain a second public key, a second private key and a second random number;
通过所述第一方利用第二国密算法、所述第一公钥、所述第一随机数对所述第一本地数据进行加密处理,得到第一密文;Encrypting the first local data by the first party using the second national secret algorithm, the first public key, and the first random number to obtain a first ciphertext;
通过所述第二方利用所述第二国密算法、所述第二公钥、所述第二随机数对所述第二本地数据进行加密处理,得到第二密文;Encrypting the second local data by the second party using the second national secret algorithm, the second public key, and the second random number to obtain a second ciphertext;
通过所述第一方提取所述第一密文中的第一部分密文和第二部分密文,将所述第一部分密文发送给所述第二方;extracting the first part of the ciphertext and the second part of the ciphertext from the first ciphertext by the first party, and sending the first part of the ciphertext to the second party;
通过所述第二方提取所述第二密文中的第三部分密文和第四部分密文,通过所述第二公钥和所述第二随机数对所述第一部分密文进行加密,得到参考第一部分密文,提取所述参考第一部分密文的部分密文,得到目标第一部分密文;将所述第三部分密文和所述目标第一部分密文发送给所述第一方;Extracting the third part of the ciphertext and the fourth part of the ciphertext in the second ciphertext by the second party, encrypting the first part of the ciphertext by using the second public key and the second random number, Obtaining the first partial ciphertext of the reference, extracting the partial ciphertext of the reference first partial ciphertext, and obtaining the target first partial ciphertext; sending the third partial ciphertext and the target first partial ciphertext to the first party ;
通过所述第一方根据所述第三部分密文、所述目标第一部分密文和所述第二部分密文进行求交运算,得到交集结果。An intersection result is obtained by the first party performing an intersection operation according to the third part of the ciphertext, the target first part of the ciphertext, and the second part of the ciphertext.
第二方面,本申请实施例提供了一种两方计算系统,应用于两方计算系统,所述两方计算系统包括第一方和第二方,所述第一方对应第一本地数据,所述第二方对应第二本地数据;其中,In the second aspect, the embodiment of the present application provides a two-party computing system, which is applied to the two-party computing system, the two-party computing system includes a first party and a second party, the first party corresponds to the first local data, The second party corresponds to the second local data; wherein,
所述第一方,用于生成第一国密算法的加解密处理参数,得到第一公钥、第一私钥和第一随机数;The first party is used to generate the encryption and decryption processing parameters of the first national secret algorithm, and obtain the first public key, the first private key and the first random number;
所述第二方,用于生成所述第一国密算法的加解密处理参数,得到第二公钥、第二私钥和第二随机数;The second party is used to generate encryption and decryption processing parameters of the first national secret algorithm to obtain a second public key, a second private key and a second random number;
所述第一方,用于利用第二国密算法、所述第一公钥、所述第一随机数对所述第一本地数据进行加密处理,得到第一密文;The first party is configured to use the second national secret algorithm, the first public key, and the first random number to encrypt the first local data to obtain a first ciphertext;
所述第二方,用于利用所述第二国密算法、所述第二公钥、所述第二随机数对所述第二本地数据进行加密处理,得到第二密文;The second party is configured to use the second national secret algorithm, the second public key, and the second random number to encrypt the second local data to obtain a second ciphertext;
通过所述第一方,用于提取所述第一密文中的第一部分密文和第二部分密文,将所述第一部分密文发送给所述第二方;through the first party, for extracting the first part of the ciphertext and the second part of the ciphertext in the first ciphertext, and sending the first part of the ciphertext to the second party;
通过所述第二方,用于提取所述第二密文中的第三部分密文和第四部分密文,通过所述第二公钥和所述第二随机数对所述第一部分密文进行加密,得到参考第一部分密文,提取所述参考第一部分密文的部分密文,得到目标第一部分密文;将所述第三部分密文和所述目标第一部分密文发送给所述第一方;Through the second party, for extracting the third part of the ciphertext and the fourth part of the ciphertext in the second ciphertext, using the second public key and the second random number to pair the first part of the ciphertext Encrypt to obtain the first part of the ciphertext for reference, extract the part of the ciphertext for the reference first part of the ciphertext, and obtain the first part of the target ciphertext; send the third part of the ciphertext and the first part of the target ciphertext to the first party;
所述第一方,用于根据所述第三部分密文、所述目标第一部分密文和所述第二部分密文进行求交运算,得到交集结果,将所述交集结果发送给所述第二方。The first party is configured to perform an intersection operation according to the third part of the ciphertext, the first part of the target ciphertext, and the second part of the ciphertext to obtain an intersection result, and send the intersection result to the second party.
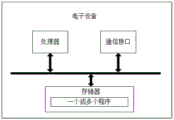
第三方面,本申请实施例提供一种电子设备,包括处理器、存储器、通信接口以及一个或多个程序,其中,上述一个或多个程序被存储在上述存储器中,并且被配置由上述处理器执行,上述程序包括用于执行本申请实施例第一方面中的步骤的指令。In a third aspect, an embodiment of the present application provides an electronic device, including a processor, a memory, a communication interface, and one or more programs, wherein the one or more programs are stored in the memory and are configured to be processed by the above-mentioned The above program includes instructions for executing the steps in the first aspect of the embodiments of the present application.
第四方面,本申请实施例提供了一种计算机可读存储介质,其中,上述计算机可读存储介质存储用于电子数据交换的计算机程序,其中,上述计算机程序使得计算机执行如本申请实施例第一方面中所描述的部分或全部步骤。In a fourth aspect, the embodiment of the present application provides a computer-readable storage medium, wherein the above-mentioned computer-readable storage medium stores a computer program for electronic data exchange, wherein the above-mentioned computer program enables the computer to execute Some or all of the steps described in one aspect.
第五方面,本申请实施例提供了一种计算机程序产品,其中,上述计算机程序产品包括存储了计算机程序的非瞬时性计算机可读存储介质,上述计算机程序可操作来使计算机执行如本申请实施例第一方面中所描述的部分或全部步骤。该计算机程序产品可以为一个软件安装包。In a fifth aspect, the embodiment of the present application provides a computer program product, wherein the computer program product includes a non-transitory computer-readable storage medium storing a computer program, and the computer program is operable to enable the computer to execute the program as implemented in the present application. Some or all of the steps described in the first aspect. The computer program product may be a software installation package.
实施本申请实施例,具备如下有益效果:Implementing the embodiment of the present application has the following beneficial effects:
可以看出,本申请实施例中所描述的基于国密的隐私集合求交方法、系统、电子设备及存储介质,应用于两方计算系统,该两方计算系统包括第一方和第二方,第一方对应第一本地数据,第二方对应第二本地数据;通过第一方生成第一国密算法的加解密处理参数,得到第一公钥、第一私钥和第一随机数;通过第二方生成第一国密算法的加解密处理参数,得到第二公钥、第二私钥和第二随机数;通过第一方利用第二国密算法、第一公钥、第一随机数对第一本地数据进行加密处理,得到第一密文;通过第二方利用第二国密算法、第二公钥、第二随机数对第二本地数据进行加密处理,得到第二密文;通过第一方提取第一密文中的第一部分密文和第二部分密文,将第一部分密文发送给第二方;通过第二方提取第二密文中的第三部分密文和第四部分密文,通过第二公钥和第二随机数对第一部分密文进行加密,得到参考第一部分密文,提取参考第一部分密文的部分密文,得到目标第一部分密文;将第三部分密文和目标第一部分密文发送给第一方;通过第一方根据第三部分密文、目标第一部分密文和第二部分密文进行求交运算,得到交集结果,采用了国密算法,可以更自主可控,另外也扩充国密算法的应用场景。It can be seen that the national secret-based privacy set intersection method, system, electronic equipment, and storage medium described in the embodiments of this application are applied to a two-party computing system, which includes a first party and a second party , the first party corresponds to the first local data, and the second party corresponds to the second local data; the encryption and decryption processing parameters of the first national secret algorithm are generated by the first party to obtain the first public key, the first private key and the first random number ;The encryption and decryption processing parameters of the first national secret algorithm are generated by the second party to obtain the second public key, the second private key and the second random number; the second party uses the second national secret algorithm, the first public key, the second A random number encrypts the first local data to obtain the first ciphertext; the second party uses the second national secret algorithm, the second public key, and the second random number to encrypt the second local data to obtain the second Ciphertext; the first part of the ciphertext and the second part of the ciphertext are extracted by the first party, and the first part of the ciphertext is sent to the second party; the third part of the ciphertext in the second ciphertext is extracted by the second party and the fourth part of the ciphertext, encrypt the first part of the ciphertext with the second public key and the second random number, obtain the reference first part of the ciphertext, extract the part of the ciphertext referring to the first part of the ciphertext, and obtain the target first part of the ciphertext; Send the third part of the ciphertext and the first part of the target ciphertext to the first party; the first party performs an intersection operation based on the third part of the ciphertext, the first part of the target ciphertext and the second part of the ciphertext to obtain the intersection result, using With the national secret algorithm, it can be more autonomous and controllable, and it also expands the application scenarios of the national secret algorithm.
附图说明Description of drawings
为了更清楚地说明本申请实施例或现有技术中的技术方案,下面将对实施例或现有技术描述中所需要使用的附图作简单地介绍,显而易见地,下面描述中的附图仅仅是本申请的一些实施例,对于本领域普通技术人员来讲,在不付出创造性劳动的前提下,还可以根据这些附图获得其他的附图。In order to more clearly illustrate the technical solutions in the embodiments of the present application or the prior art, the following will briefly introduce the drawings that need to be used in the description of the embodiments or the prior art. Obviously, the accompanying drawings in the following description are only These are some embodiments of the present application. Those skilled in the art can also obtain other drawings based on these drawings without creative work.
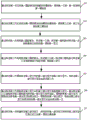
图1是本申请实施例提供的一种用于实现基于国密的隐私集合求交方法的两方计算系统的结构示意图;FIG. 1 is a schematic structural diagram of a two-party computing system for implementing a private set intersection method based on national secrets provided by an embodiment of the present application;
图2是本申请实施例提供的一种基于国密的隐私集合求交方法的流程示意图;Fig. 2 is a schematic flow diagram of a method for intersecting a private set based on national secrets provided by an embodiment of the present application;
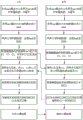
图3是本申请实施例提供的另一种基于国密的隐私集合求交方法的流程示意图;Fig. 3 is a schematic flow diagram of another method for finding intersection of privacy sets based on national secrets provided by the embodiment of the present application;
图4是本申请实施例提供的一种电子设备的结构示意图。FIG. 4 is a schematic structural diagram of an electronic device provided by an embodiment of the present application.
具体实施方式Detailed ways
为了使本技术领域的人员更好地理解本申请方案,下面将结合本申请实施例中的附图,对本申请实施例中的技术方案进行清楚、完整地描述,显然,所描述的实施例仅仅是本申请一部分实施例,而不是全部的实施例。基于本申请中的实施例,本领域普通技术人员在没有作出创造性劳动前提下所获得的所有其他实施例,都属于本申请保护的范围。In order to enable those skilled in the art to better understand the solution of the present application, the technical solution in the embodiment of the application will be clearly and completely described below in conjunction with the accompanying drawings in the embodiment of the application. Obviously, the described embodiment is only It is a part of the embodiments of this application, not all of them. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of this application.
本申请的说明书和权利要求书及上述附图中的术语“第一”、“第二”等是用于区别不同对象,而不是用于描述特定顺序。此外,术语“包括”和“具有”以及它们任何变形,意图在于覆盖不排他的包含。例如包含了一系列步骤或单元的过程、方法、系统、产品或设备没有限定于已列出的步骤或单元,而是可选地还包括没有列出的步骤或单元,或可选地还包括对于这些过程、方法、产品或设备固有的其他步骤或单元。The terms "first", "second" and the like in the specification and claims of the present application and the above drawings are used to distinguish different objects, rather than to describe a specific order. Furthermore, the terms "include" and "have", as well as any variations thereof, are intended to cover a non-exclusive inclusion. For example, a process, method, system, product or device comprising a series of steps or units is not limited to the listed steps or units, but optionally also includes unlisted steps or units, or optionally further includes For other steps or units inherent in these processes, methods, products or devices.
在本文中提及“实施例”意味着,结合实施例描述的特定特征、结构或特性可以包含在本申请的至少一个实施例中。在说明书中的各个位置出现该短语并不一定均是指相同的实施例,也不是与其它实施例互斥的独立的或备选的实施例。本领域技术人员显式地和隐式地理解的是,本文所描述的实施例可以与其它实施例相结合。Reference herein to an "embodiment" means that a particular feature, structure, or characteristic described in connection with the embodiment can be included in at least one embodiment of the present application. The occurrences of this phrase in various places in the specification are not necessarily all referring to the same embodiment, nor are separate or alternative embodiments mutually exclusive of other embodiments. It is understood explicitly and implicitly by those skilled in the art that the embodiments described herein can be combined with other embodiments.
本申请实施例所描述计算节点可以为电子设备,电子设备可以包括智能手机(如Android手机、iOS手机、Windows Phone手机等)、平板电脑、掌上电脑、行车记录仪、服务器、笔记本电脑、移动互联网设备(MID,Mobile Internet Devices)或穿戴式设备(如智能手表、蓝牙耳机)等,上述仅是举例,而非穷举,包含但不限于上述电子设备,该电子设备也可以为云服务器,或者,该电子设备也可以为计算机集群。本申请实施例中,结果方、发送方均可以为上述电子设备。The computing node described in the embodiment of this application can be an electronic device, and the electronic device can include a smart phone (such as an Android phone, an iOS phone, a Windows Phone, etc.), a tablet computer, a palmtop computer, a driving recorder, a server, a notebook computer, a mobile Internet Devices (MID, Mobile Internet Devices) or wearable devices (such as smart watches, Bluetooth headsets), etc., the above are only examples, not exhaustive, including but not limited to the above-mentioned electronic devices, which can also be cloud servers, or , the electronic device can also be a computer cluster. In this embodiment of the present application, both the result party and the sender may be the above-mentioned electronic devices.
本申请实施例中,国密算法即为国家商用密码算法。是由国家密码管理局认定和公布的密码算法标准及其应用规范,其中部分密码算法已经成为国际标准。如SM系列密码,SM代表商密,即商业密码,是指用于商业的、不涉及国家秘密的密码技术。In the embodiment of this application, the National Encryption Algorithm is the National Commercial Encryption Algorithm. It is a cryptographic algorithm standard and its application specification recognized and published by the State Cryptography Administration, some of which have become international standards. Such as the SM series of ciphers, SM stands for commercial secrets, that is, commercial ciphers, which refer to cryptographic techniques that are used for commerce and do not involve state secrets.
下面对本申请实施例进行详细介绍。The following describes the embodiments of the present application in detail.
相关技术中的PSI技术大多可分为4类:基于公钥的方案,基于不经意传输(ObliviousTransfer,OT)的方案,基于同态加密(homomorphic encryption,HE)的方案和基于混淆电路(garbled circuit,GC)的方案。对应的,目前的国密算法中的公钥加密算法(sm2)可应用于基于公钥的PSI方案。相关技术中的隐私集合求交技术尚未采用国密的方案,这使得PSI技术在一些安全性和自主可控性要求较高的场景无法适用,如涉及大型银行,国家机关等的合作场景。Most of the PSI technologies in related technologies can be divided into four categories: schemes based on public keys, schemes based on Oblivious Transfer (OT), schemes based on homomorphic encryption (HE) and schemes based on garbled circuits, GC) scheme. Correspondingly, the public key encryption algorithm (sm2) in the current national secret algorithm can be applied to the PSI scheme based on the public key. The privacy set intersection technology in related technologies has not yet adopted the national secret solution, which makes the PSI technology unsuitable for some scenarios that require high security and autonomous controllability, such as cooperation scenarios involving large banks and state agencies.
请参阅图1,图1是本申请实施例提供的一种用于实现基于国密的隐私集合求交方法的两方计算系统的架构示意图,如图所示,本两方计算系统可以包括第一方和第二方;所述第一方对应第一本地数据,所述第二方对应第二本地数据;基于该两方计算系统可以实现如下功能:Please refer to Figure 1. Figure 1 is a schematic diagram of the architecture of a two-party computing system for implementing a privacy set intersection method based on national secrets provided by an embodiment of the present application. As shown in the figure, the two-party computing system may include the first One party and a second party; the first party corresponds to the first local data, and the second party corresponds to the second local data; based on the two parties, the computing system can realize the following functions:
通过所述第一方生成第一国密算法的加解密处理参数,得到第一公钥、第一私钥和第一随机数;Generate the encryption and decryption processing parameters of the first national secret algorithm by the first party to obtain the first public key, the first private key and the first random number;
通过所述第二方生成所述第一国密算法的加解密处理参数,得到第二公钥、第二私钥和第二随机数;generating encryption and decryption processing parameters of the first national secret algorithm by the second party to obtain a second public key, a second private key and a second random number;
通过所述第一方利用第二国密算法、所述第一公钥、所述第一随机数对所述第一本地数据进行加密处理,得到第一密文;Encrypting the first local data by the first party using the second national secret algorithm, the first public key, and the first random number to obtain a first ciphertext;
通过所述第二方利用所述第二国密算法、所述第二公钥、所述第二随机数对所述第二本地数据进行加密处理,得到第二密文;Encrypting the second local data by the second party using the second national secret algorithm, the second public key, and the second random number to obtain a second ciphertext;
通过所述第一方提取所述第一密文中的第一部分密文和第二部分密文,将所述第一部分密文发送给所述第二方;extracting the first part of the ciphertext and the second part of the ciphertext from the first ciphertext by the first party, and sending the first part of the ciphertext to the second party;
通过所述第二方提取所述第二密文中的第三部分密文和第四部分密文,通过所述第二公钥和所述第二随机数对所述第一部分密文进行加密,得到参考第一部分密文,提取所述参考第一部分密文的部分密文,得到目标第一部分密文;将所述第三部分密文和所述目标第一部分密文发送给所述第一方;Extracting the third part of the ciphertext and the fourth part of the ciphertext in the second ciphertext by the second party, encrypting the first part of the ciphertext by using the second public key and the second random number, Obtaining the first partial ciphertext of the reference, extracting the partial ciphertext of the reference first partial ciphertext, and obtaining the target first partial ciphertext; sending the third partial ciphertext and the target first partial ciphertext to the first party ;
通过所述第一方根据所述第三部分密文、所述目标第一部分密文和所述第二部分密文进行求交运算,得到交集结果,将所述交集结果发送给所述第二方。The first party performs an intersection operation according to the third part of the ciphertext, the first part of the target ciphertext, and the second part of the ciphertext to obtain an intersection result, and send the intersection result to the second square.
可选的,所述通过所述第一方利用第二国密算法、所述第一公钥、所述第一随机数对所述第一本地数据进行加密处理,得到第一密文,包括:Optionally, the first party encrypts the first local data using the second national secret algorithm, the first public key, and the first random number to obtain the first ciphertext, including :
通过所述第一方利用所述第二国密算法对所述第一本地数据进行哈希运算,得到第一哈希运算结果;performing a hash operation on the first local data by the first party using the second national secret algorithm to obtain a first hash operation result;
利用所述第一公钥和所述第一随机数对所述第一哈希运算结果进行加密处理,得到所述第一密文。Encrypting the first hash operation result by using the first public key and the first random number to obtain the first ciphertext.
可选的,所述通过所述第二方利用所述第二国密算法、所述第二公钥、所述第二随机数对所述第二本地数据进行加密处理,得到第二密文,包括:Optionally, the second party uses the second national secret algorithm, the second public key, and the second random number to encrypt the second local data to obtain a second ciphertext ,include:
通过所述第二方利用所述第二国密算法对所述第二本地数据进行哈希运算,得到第二哈希运算结果;performing a hash operation on the second local data by the second party using the second national secret algorithm to obtain a second hash operation result;
利用所述第二公钥和所述第二随机数对所述第二哈希运算结果进行加密处理,得到所述第二密文。Encrypting the second hash operation result by using the second public key and the second random number to obtain the second ciphertext.
可选的,在所述第一加密算法为sm2算法时,所述通过所述第一方提取所述第一密文中的第一部分密文和第二部分密文,包括:Optionally, when the first encryption algorithm is the sm2 algorithm, the extraction of the first part of the ciphertext and the second part of the ciphertext in the first ciphertext by the first party includes:
通过所述第一方利用第一椭圆曲线参数对所述第一密文进行密文提取,得到第一C1密文、第一C2密文和第一C3密文;performing ciphertext extraction on the first ciphertext by using the first elliptic curve parameters by the first party to obtain the first C1 ciphertext, the first C2 ciphertext and the first C3 ciphertext;
将所述第一C2密文确定为所述第一部分密文;determining the first C2 ciphertext as the first partial ciphertext;
将所述第一C1密文和所述第一C3密文进行拼接,得到所述第二部分密文。Splicing the first C1 ciphertext and the first C3 ciphertext to obtain the second part of ciphertext.
可选的,所述通过所述第二方提取所述第二密文中的第三部分密文和第四部分密文,包括:Optionally, the extracting the third part of ciphertext and the fourth part of ciphertext in the second ciphertext through the second party includes:
通过所述第二方利用第二椭圆曲线参数对所述第二密文进行密文提取,得到第二C1密文、第二C2密文和第二C3密文;performing ciphertext extraction on the second ciphertext by using the second elliptic curve parameters by the second party to obtain a second C1 ciphertext, a second C2 ciphertext, and a second C3 ciphertext;
将所述第二C2密文确定为所述第三部分密文;determining the second C2 ciphertext as the third partial ciphertext;
将所述第二C1密文和所述第二C3密文进行拼接,得到所述第二部分密文。Splicing the second C1 ciphertext and the second C3 ciphertext to obtain the second part of ciphertext.
可选的,所述通过所述第一方根据所述第三部分密文、所述目标第一部分密文和所述第二部分密文进行求交运算,得到交集结果,包括:Optionally, the first party performs an intersection operation according to the third part of the ciphertext, the first part of the target ciphertext, and the second part of the ciphertext to obtain an intersection result, including:
通过所述第一方将所述第二部分密文和所述目标第一部分密文进行拼接,得到拼接密文;Splicing the second part of the ciphertext and the target first part of the ciphertext through the first party to obtain the spliced ciphertext;
利用所述第一私钥解密所述拼接密文,得到解密结果;Decrypting the concatenated ciphertext by using the first private key to obtain a decryption result;
将所述解密结果与所述第三部分密文进行求交运算,得到交集结果。Perform an intersection operation on the decryption result and the third part of the ciphertext to obtain an intersection result.
请参阅图2,图2是本申请实施例提供的一种基于国密的隐私集合求交方法的流程示意图,应用于图1所示的两方计算系统,所述两方计算系统包括第一方和第二方,所述第一方对应第一本地数据,所述第二方对应第二本地数据;如图所示,本基于国密的隐私集合求交方法包括:Please refer to FIG. 2. FIG. 2 is a schematic flow diagram of a method for intersecting a private set based on national secrets provided by an embodiment of the present application, which is applied to the two-party computing system shown in FIG. 1, and the two-party computing system includes a first Party and the second party, the first party corresponds to the first local data, and the second party corresponds to the second local data; as shown in the figure, this method for finding intersection based on the privacy set of national secrets includes:
201、通过所述第一方生成第一国密算法的加解密处理参数,得到第一公钥、第一私钥和第一随机数。201. Generate encryption and decryption processing parameters of a first national secret algorithm by the first party to obtain a first public key, a first private key, and a first random number.
其中,第一国密算法可以包括任一国密算法,例如,SM系列国密算法,具体可以为以下至少一种:sm2国密算法、sm9国密算法等等,在此不做限定。Wherein, the first national secret algorithm may include any national secret algorithm, for example, the SM series national secret algorithm, specifically at least one of the following: sm2 national secret algorithm, sm9 national secret algorithm, etc., which are not limited here.
具体实现中,可以第一方生成第一国密算法的加解密处理参数,从而,可以得到第一公钥、第一私钥和加密需要的第一随机数。In a specific implementation, the encryption and decryption processing parameters of the first national secret algorithm can be generated by the first party, so that the first public key, the first private key and the first random number needed for encryption can be obtained.
其中,第一本地数据、第二本地数据均可以为一个数据集合,该数据集合可以包括多条数据组,每一数据组可以包括多个数据,每一数据可以对应一个标签信息,每一数据可以理解为一个信息字段,其用于表述标签信息的内容,标签信息可以包括以下至少一种:身份卡号(ID-CARD)、电话号码(Phone Number)、银行卡号(Bank Card)、社保账号、社交账号、学号、工号等等,在此不做限定。Wherein, both the first local data and the second local data can be a data set, the data set can include multiple data groups, each data group can include multiple data, each data can correspond to a tag information, each data It can be understood as an information field, which is used to express the content of the tag information. The tag information can include at least one of the following: ID-CARD, Phone Number, Bank Card, social security account number, Social account, student ID, job ID, etc. are not limited here.
本申请实施例中,本地数据中的每一行数据可以对应一个ID,该ID是每一行数据的唯一标识符,每一行都不相同,如:身份证号,手机号或自增序号。In the embodiment of this application, each row of data in the local data may correspond to an ID, which is a unique identifier of each row of data, and each row is different, such as: ID card number, mobile phone number or self-incrementing serial number.
举例说明下,具体实现中,银行C想利用运营商B的数据进行联合建模,评估用户的风险等级。则开始建模之前,双方需提供相同用户的画像标签,但双方不想暴露各自本地的非交集用户。他们可采用隐私集合求交技术获得双方的交集用户。As an example, in the specific implementation, bank C wants to use the data of operator B to conduct joint modeling to evaluate the risk level of users. Before starting modeling, both parties need to provide the portrait labels of the same users, but both parties do not want to expose their local non-intersecting users. They can use the private set intersection technique to obtain the intersection users of both parties.
202、通过所述第二方生成所述第一国密算法的加解密处理参数,得到第二公钥、第二私钥和第二随机数。202. Generate encryption and decryption processing parameters of the first national secret algorithm by the second party to obtain a second public key, a second private key, and a second random number.
其中,具体实现中,可以第二方生成第一国密算法的加解密处理参数,从而,可以得到第二公钥、第二私钥和加密需要的第二随机数。Wherein, in a specific implementation, the encryption and decryption processing parameters of the first national secret algorithm can be generated by the second party, so that the second public key, the second private key and the second random number required for encryption can be obtained.
203、通过所述第一方利用第二国密算法、所述第一公钥、所述第一随机数对所述第一本地数据进行加密处理,得到第一密文。203. The first party encrypts the first local data by using the second national secret algorithm, the first public key, and the first random number to obtain a first ciphertext.
其中,可以通过第一方利用第二国密算法对第一本地数据进行哈希运算,再基于第一公钥、第一随机数对哈希运算结果进行加密处理,得到第一密文,例如,可以将hash后的结果进行sm2加密,得到密文M。Among them, the first party can use the second national secret algorithm to perform a hash operation on the first local data, and then encrypt the result of the hash operation based on the first public key and the first random number to obtain the first ciphertext, for example , the hashed result can be encrypted with sm2 to obtain the ciphertext M.
可选的,上述步骤203,通过所述第一方利用第二国密算法、所述第一公钥、所述第一随机数对所述第一本地数据进行加密处理,得到第一密文,可以包括如下步骤:Optionally, in the
31、通过所述第一方利用所述第二国密算法对所述第一本地数据进行哈希运算,得到第一哈希运算结果;31. The first party uses the second national secret algorithm to perform a hash operation on the first local data to obtain a first hash operation result;
32、利用所述第一公钥和所述第一随机数对所述第一哈希运算结果进行加密处理,得到所述第一密文。32. Perform encryption processing on the first hash operation result by using the first public key and the first random number to obtain the first ciphertext.
具体实现中,通过第一方利用第二国密算法对第一本地数据进行哈希运算,得到第一哈希运算结果,再可以利用第一公钥和第一随机数对第一哈希运算结果进行加密处理,得到第一密文,如此,可以实现一次加密处理,有助于提升数据安全性。In the specific implementation, the first party uses the second national secret algorithm to perform a hash operation on the first local data to obtain the first hash operation result, and then use the first public key and the first random number to perform the first hash operation The results are encrypted to obtain the first ciphertext. In this way, one encryption process can be implemented, which helps to improve data security.
204、通过所述第二方利用所述第二国密算法、所述第二公钥、所述第二随机数对所述第二本地数据进行加密处理,得到第二密文。204. The second party encrypts the second local data by using the second national secret algorithm, the second public key, and the second random number to obtain a second ciphertext.
具体实现中,其中,可以通过第二方利用第二国密算法对第二本地数据进行哈希运算,再基于第二公钥、第二随机数对哈希运算结果进行加密处理,得到第二密文。In the specific implementation, the second party can use the second national secret algorithm to perform a hash operation on the second local data, and then encrypt the result of the hash operation based on the second public key and the second random number to obtain the second ciphertext.
可选的,上述步骤204,通过所述第二方利用所述第二国密算法、所述第二公钥、所述第二随机数对所述第二本地数据进行加密处理,得到第二密文,可以包括如下步骤:Optionally, in the
41、通过所述第二方利用所述第二国密算法对所述第二本地数据进行哈希运算,得到第二哈希运算结果;41. The second party uses the second national secret algorithm to perform a hash operation on the second local data to obtain a second hash operation result;
42、利用所述第二公钥和所述第二随机数对所述第二哈希运算结果进行加密处理,得到所述第二密文。42. Perform encryption processing on the second hash operation result by using the second public key and the second random number to obtain the second ciphertext.
具体实现中,通过第二方利用第二国密算法对第二本地数据进行哈希运算,得到第二哈希运算结果,利用第二公钥和第二随机数对第二哈希运算结果进行加密处理,得到第二密文,如此,可以实现一次加密处理,有助于提升数据安全性。In the specific implementation, the second party uses the second national secret algorithm to perform a hash operation on the second local data to obtain the second hash operation result, and uses the second public key and the second random number to perform hash operation on the second hash operation result Encryption processing to obtain the second ciphertext, so that one encryption processing can be realized, which helps to improve data security.
205、通过所述第一方提取所述第一密文中的第一部分密文和第二部分密文,将所述第一部分密文发送给所述第二方。205. Extract the first part of ciphertext and the second part of ciphertext from the first ciphertext by the first party, and send the first part of ciphertext to the second party.
具体实现中,通过第一方提取第一密文中的第一部分密文和第二部分密文,将第一部分密文发送给第二方。例如,可以通过sm2算法提取第一密文中的C1、C2、C3密文,可以将C2作为第一部分密文,C1和C3进行拼接作为第二部分密文。In a specific implementation, the first part of the ciphertext and the second part of the ciphertext are extracted by the first party, and the first part of the ciphertext is sent to the second party. For example, the ciphertexts C1, C2, and C3 in the first ciphertext can be extracted through the sm2 algorithm, C2 can be used as the first part of the ciphertext, and C1 and C3 can be concatenated as the second part of the ciphertext.
可选的,在所述第一加密算法为sm2算法时,上述步骤205,通过所述第一方提取所述第一密文中的第一部分密文和第二部分密文,可以包括如下步骤:Optionally, when the first encryption algorithm is the sm2 algorithm, the
51、通过所述第一方利用第一椭圆曲线参数对所述第一密文进行密文提取,得到第一C1密文、第一C2密文和第一C3密文;51. Using the first elliptic curve parameters to perform ciphertext extraction on the first ciphertext by the first party to obtain the first C1 ciphertext, the first C2 ciphertext, and the first C3 ciphertext;
52、将所述第一C2密文确定为所述第一部分密文;52. Determine the first C2 ciphertext as the first partial ciphertext;
53、将所述第一C1密文和所述第一C3密文进行拼接,得到所述第二部分密文。53. Concatenate the first C1 ciphertext and the first C3 ciphertext to obtain the second part of ciphertext.
本申请实施例中,第一椭圆曲线参数可以为sm2算法的椭圆曲线参数。In this embodiment of the present application, the first elliptic curve parameter may be an elliptic curve parameter of the sm2 algorithm.
具体的,可以通过第一方利用第一椭圆曲线参数对第一密文进行密文提取,得到第一C1密文、第一C2密文和第一C3密文,再将第一C2密文确定为第一部分密文,将第一C1密文和第一C3密文进行拼接,得到第二部分密文。Specifically, the first party may use the first elliptic curve parameters to perform ciphertext extraction on the first ciphertext to obtain the first C1 ciphertext, the first C2 ciphertext, and the first C3 ciphertext, and then extract the first C2 ciphertext It is determined as the first part of the ciphertext, and the first C1 ciphertext and the first C3 ciphertext are spliced to obtain the second part of the ciphertext.
举例说明下,可以利用sm2算法的椭圆曲线参数(椭圆曲线基点的阶n),得到密文中椭圆曲线上点的长度(记为len=n的比特长度,通常为64),并依此定位第一C1密文、第一C2密文和第一C3密文,第一C2密文的起始位置由公式2*len+64计算得到,即C2=M[2*len+64:],M中前半部分的密文则为第一C1密文和第一C3密文的拼接,记为C1||C3=M[:2*len+64]。For example, the elliptic curve parameter of the sm2 algorithm (the order n of the elliptic curve base point) can be used to obtain the length of the point on the elliptic curve in the ciphertext (recorded as the bit length of len=n, usually 64), and accordingly locate the first One C1 ciphertext, the first C2 ciphertext and the first C3 ciphertext, the starting position of the first C2 ciphertext is calculated by the formula 2*len+64, that is, C2=M[2*len+64:], M The ciphertext in the first half is the concatenation of the first C1 ciphertext and the first C3 ciphertext, which is denoted as C1||C3=M[:2*len+64].
本申请实施例中,可以基于sm2算法的椭圆曲线上点的运算,因为sm2算法的加密结果不仅包含椭圆曲线上的点(C1),还包括了点和原文拼接的一个hash值(C3),以及原文的加密结果(C2),即SM2密文是由C1,C3,C2拼接而成,记为(C1||C3||C2),因此,需要将对应组成部分提取出来进行加解密操作。In the embodiment of this application, the calculation of points on the elliptic curve based on the sm2 algorithm can be used, because the encrypted result of the sm2 algorithm not only includes the point (C1) on the elliptic curve, but also includes a hash value (C3) spliced between the point and the original text, And the encryption result (C2) of the original text, that is, the SM2 ciphertext is composed of C1, C3, and C2, which is recorded as (C1||C3||C2). Therefore, the corresponding components need to be extracted for encryption and decryption operations.
206、通过所述第二方提取所述第二密文中的第三部分密文和第四部分密文,通过所述第二公钥和所述第二随机数对所述第一部分密文进行加密,得到参考第一部分密文,提取所述参考第一部分密文的部分密文,得到目标第一部分密文;将所述第三部分密文和所述目标第一部分密文发送给所述第一方。206. Using the second party to extract the third part of the ciphertext and the fourth part of the ciphertext in the second ciphertext, and using the second public key and the second random number to process the first part of the ciphertext Encrypt to obtain the first partial ciphertext of the reference, extract the partial ciphertext of the reference first partial ciphertext, and obtain the target first partial ciphertext; send the third partial ciphertext and the target first partial ciphertext to the first party.
具体实现中,也可以采用上述步骤205类似方法,提取第二密文中的第三部分密文和第四部分密文,第三部分密文与第一部分密文对应,第四部分密文与第二部分密文对应,再通过第二公钥和第二随机数对第一部分密文进行加密,得到参考第一部分密文,即二次密文,再可以提取参考第一部分密文的部分密文,得到目标第一部分密文,将第三部分密文和目标第一部分密文发送给第一方。例如,可以利用第三椭圆曲线参数对参考第一部分密文进行密文提取,得到C1密文、C2密文和C3密文,再将C2密文作为目标第一部分密文。In a specific implementation, a method similar to the
本申请实施例中,第三椭圆曲线参数可以为sm2算法的椭圆曲线参数。第一椭圆曲线参数、第二椭圆曲线参数、第三椭圆曲线参数可以相同或者不同。In this embodiment of the present application, the third elliptic curve parameter may be an elliptic curve parameter of the sm2 algorithm. The first elliptic curve parameter, the second elliptic curve parameter, and the third elliptic curve parameter may be the same or different.
可选的,上述步骤206、通过所述第二方提取所述第二密文中的第三部分密文和第四部分密文,可以包括如下步骤:Optionally, the
61、通过所述第二方利用第二椭圆曲线参数对所述第二密文进行密文提取,得到第二C1密文、第二C2密文和第二C3密文;61. Using the second elliptic curve parameters to perform ciphertext extraction on the second ciphertext by the second party to obtain a second C1 ciphertext, a second C2 ciphertext, and a second C3 ciphertext;
62、将所述第二C2密文确定为所述第三部分密文;62. Determine the second C2 ciphertext as the third partial ciphertext;
63、将所述第二C1密文和所述第二C3密文进行拼接,得到所述第二部分密文。63. Concatenate the second C1 ciphertext and the second C3 ciphertext to obtain the second part of ciphertext.
本申请实施例中,第二椭圆曲线参数可以为sm2算法的椭圆曲线参数。第一椭圆曲线参数、第二椭圆曲线参数可以相同或者不同。In this embodiment of the present application, the second elliptic curve parameter may be an elliptic curve parameter of the sm2 algorithm. The first elliptic curve parameter and the second elliptic curve parameter may be the same or different.
具体的,可以通过第二方利用第二椭圆曲线参数对第二密文进行密文提取,得到第二C1密文、第二C2密文和第二C3密文,再将第二C2密文确定为第三部分密文,将第二C1密文和第二C3密文进行拼接,得到第四部分密文。Specifically, the second party may use the second elliptic curve parameters to perform ciphertext extraction on the second ciphertext to obtain the second C1 ciphertext, the second C2 ciphertext, and the second C3 ciphertext, and then extract the second C2 ciphertext It is determined as the third part of the ciphertext, and the second C1 ciphertext and the second C3 ciphertext are spliced to obtain the fourth part of the ciphertext.
举例说明下,可以利用sm2算法椭圆曲线参数(椭圆曲线基点的阶n),得到密文中椭圆曲线上点的长度(记为len=n的比特长度,通常为64),并依此定位第二C1密文、第二C2密文和第二C3密文,第二C2密文的起始位置由公式2*len+64计算得到,即C2=M[2*len+64:],M中前半部分的密文则为第二C1密文和第二C3密文的拼接,记为C1||C3=M[:2*len+64]。For example, the elliptic curve parameter of the sm2 algorithm (the order n of the base point of the elliptic curve) can be used to obtain the length of the point on the elliptic curve in the ciphertext (recorded as the bit length of len=n, usually 64), and accordingly locate the second C1 ciphertext, the second C2 ciphertext and the second C3 ciphertext, the starting position of the second C2 ciphertext is calculated by the formula 2*len+64, that is, C2=M[2*len+64:], in M The ciphertext in the first half is the concatenation of the second C1 ciphertext and the second C3 ciphertext, which is recorded as C1||C3=M[:2*len+64].
207、通过所述第一方根据所述第三部分密文、所述目标第一部分密文和所述第二部分密文进行求交运算,得到交集结果。207. The first party performs an intersection operation according to the third part of ciphertext, the target first part of ciphertext, and the second part of ciphertext to obtain an intersection result.
具体实现中,第二部分密文与目标第一部分密文可以进行拼接,得到拼接密文,再利用第一私钥对其进行解密,得到解密结果,再将其与第三部分密文进行求交运算,便可以得到交集结果。当然,还可以将交集结果发送给第二方。In the specific implementation, the second part of the ciphertext and the first part of the target ciphertext can be concatenated to obtain the concatenated ciphertext, and then use the first private key to decrypt it to obtain the decryption result, and then calculate it with the third part of the ciphertext Intersection operation, you can get the intersection result. Of course, it is also possible to send the intersection result to a second party.
本申请实施例中,能够扩充了国密算法的应用场景,还可以保证了隐私集合求交过程的安全、可靠、可控,以及降低了隐私集合求交过程的通信量。In the embodiment of the present application, the application scenarios of the national secret algorithm can be expanded, and the security, reliability, and controllability of the private set intersection process can be guaranteed, and the communication traffic of the private set intersection process can be reduced.
具体的,一方面国密算法是由国家密码局认定的国产商用密码算法,国家自主可控。密码安全是一个国家综合国力和竞争力的重要标志,密码技术作为国家自主可控的核心技术,在维护国家安全、促进经济发展方面发挥着越来越重要的作用,另一方面国密算法在加密强度或运算性能上都优于同类国际通用算法,因为采用的椭圆曲线加密国密算法,相较普通的公钥加密算法,相同安全等级要求下,密钥长度更短,所以密文更小,可以显著降低通讯量。Specifically, on the one hand, the national encryption algorithm is a domestic commercial encryption algorithm recognized by the State Cryptography Administration, which is independently controllable by the state. Encryption security is an important symbol of a country's comprehensive national strength and competitiveness. As a core technology independently and controllable by the country, encryption technology is playing an increasingly important role in maintaining national security and promoting economic development. Encryption strength and computing performance are superior to similar international general algorithms, because the elliptic curve encryption national secret algorithm adopted, compared with ordinary public key encryption algorithms, under the same security level requirements, the key length is shorter, so the ciphertext is smaller , can significantly reduce the amount of communication.
可选的,上述步骤207,通过所述第一方根据所述第三部分密文、所述目标第一部分密文和所述第二部分密文进行求交运算,得到交集结果,可以包括如下步骤:Optionally, in the
71、通过所述第一方将所述第二部分密文和所述目标第一部分密文进行拼接,得到拼接密文;71. Splicing the second part of the ciphertext and the target first part of the ciphertext through the first party to obtain the spliced ciphertext;
72、利用所述第一私钥解密所述拼接密文,得到解密结果;72. Decrypt the concatenated ciphertext by using the first private key to obtain a decryption result;
73、将所述解密结果与所述第三部分密文进行求交运算,得到交集结果。73. Perform an intersection operation on the decryption result and the third part of the ciphertext to obtain an intersection result.
具体实现中,可以通过第一方将第二部分密文和目标第一部分密文进行拼接,得到拼接密文,再利用第一私钥解密拼接密文,得到解密结果,最后,可以将解密结果与第三部分密文进行求交运算,得到交集结果。In the specific implementation, the first party can concatenate the second part of the ciphertext and the first part of the target ciphertext to obtain the concatenated ciphertext, and then use the first private key to decrypt the concatenated ciphertext to obtain the decryption result. Finally, the decryption result can be Perform an intersection operation with the third part of the ciphertext to obtain the intersection result.
本申请实施例中,可以利用sm3和sm2算法,通过改造现有的基于Diffie-Hellmann密钥协商的PSI方案,提出了一种基于国密的PSI方案,扩充了国密算法的应用场景,保证了隐私集合求交过程的安全、可靠、可控。此外因为采用的是椭圆曲线加密方案,降低了PSI过程的通信量。In the embodiment of this application, the sm3 and sm2 algorithms can be used to improve the existing PSI scheme based on Diffie-Hellmann key agreement, and a PSI scheme based on the national secret is proposed, which expands the application scenarios of the national secret algorithm and ensures It ensures the safety, reliability and controllability of the privacy set intersection process. In addition, because the elliptic curve encryption scheme is adopted, the communication volume of the PSI process is reduced.
本申请实施例中,在第一国密算法为sm2国密算法、第二国密算法为sm3国密算法时,则提出了一种基于国密(sm2和sm3)的隐私集合求交方案,进而,扩充了国密算法的应用场景,保证了隐私集合求交过程的安全、可靠、可控。In the embodiment of the present application, when the first national secret algorithm is the sm2 national secret algorithm and the second national secret algorithm is the sm3 national secret algorithm, a privacy set intersection scheme based on the national secrets (sm2 and sm3) is proposed, Furthermore, the application scenarios of the national secret algorithm are expanded to ensure the safety, reliability and controllability of the private set intersection process.
具体实现过程,在第一方为C方,第二方为B方的情况下,如图3所示,B方、C两方基于国密的隐私集合求交过程可以包括如下步骤:The specific implementation process, in the case where the first party is party C and the second party is party B, as shown in Figure 3, the process of seeking the intersection of party B and party C based on the privacy set of national secrets may include the following steps:
S1、B、C双方各自生成sm2算法中公私钥及sm2加密时需要的随机数k,并缓存;S1, B, and C each generate the public and private keys in the sm2 algorithm and the random number k required for sm2 encryption, and cache them;
S2、B、C双方用sm3算法对用于隐私集合求交的数据ID进行hash,例如,可以利用sm3算法对本地数据ID进行hash。S2, B, and C use the sm3 algorithm to hash the data ID used for the intersection of privacy sets. For example, the sm3 algorithm can be used to hash the local data ID.
S3、B、C双方将各自hash后的结果进行sm2加密,得到密文M,即:各自利用公钥和随机数,加密hash后的ID,即可以得到密文M。S3, B, and C perform sm2 encryption on their respective hash results to obtain the ciphertext M, that is, each uses the public key and random number to encrypt the hashed ID to obtain the ciphertext M.
S4、B、C双方各自根据椭圆曲线参数提取sm2密文中C1,C3,C2,具体的:利用sm2椭圆曲线参数,得到密文中椭圆曲线上点的长度(记为len),并依此定位hash值加密的密文,密文起始位置由公式2*len+64计算得到,即C2=M[2*len+64:],M中前半部分的密文则为C1和C3的拼接,记为C1||C3=M[:2*len+64]。S4, B, and C each extract C1, C3, and C2 in the sm2 ciphertext according to the elliptic curve parameters. Specifically: use the sm2 elliptic curve parameters to obtain the length of the point on the elliptic curve in the ciphertext (denoted as len), and locate the hash accordingly Value encrypted ciphertext, the starting position of the ciphertext is calculated by the formula 2*len+64, that is, C2=M[2*len+64:], the ciphertext in the first half of M is the concatenation of C1 and C3, record is C1||C3=M[:2*len+64].
S5、C方将本方C2发送给B方。S5. Party C sends party C2 to party B.
S6、B方接收C方信息C2,并利用本方缓存的公钥和随机数加密该C2,具体的,利用本方缓存的公钥和随机数对C2进行sm2加密,得到C方C2二次加密的密文。S6. Party B receives party C's information C2, and encrypts the C2 with its cached public key and random number. Specifically, uses its cached public key and random number to encrypt C2 with sm2, and obtains party C's C2 twice Encrypted ciphertext.
S7、利用步骤S4中相同的方法提取二次加密密文的C2,即根据椭圆曲线参数提取新密文中的C2;将其与B方C2一同发给C方,即B方将本地的C2和C方加密后再提取的C2一同发给C方。S7. Use the same method in step S4 to extract the C2 of the secondary encrypted ciphertext, that is, extract the C2 in the new ciphertext according to the elliptic curve parameters; send it to the C party together with the C2 of the B party, that is, the B party will send the local C2 and C2 C party encrypts and then extracts C2 and sends it to C party together.
S8、C方接收B方信息,将C1、C3和二次加密后的本方数据ID的C2拼接,利用缓存的私钥解密拼接后的密文,得到的结果即为本方数据ID利用B方公钥加密的结果。S8. Party C receives party B's information, splices C1, C3 and C2 of the party's data ID after the second encryption, and uses the cached private key to decrypt the spliced ciphertext, and the result obtained is the party's data ID using B The result of party public key encryption.
S9、将解密后的结果与C方接收到的B方C2本地求交集。S9. Compute the intersection of the decrypted result and the B party C2 received by the C party locally.
S10、C方发送交集结果给B方,B方则可以接收交集结果。S10, Party C sends the intersection result to Party B, and Party B can receive the intersection result.
可以看出,本申请实施例中所描述的基于国密的隐私集合求交方法,应用于两方计算系统,该两方计算系统包括第一方和第二方,第一方对应第一本地数据,第二方对应第二本地数据;通过第一方生成第一国密算法的加解密处理参数,得到第一公钥、第一私钥和第一随机数;通过第二方生成第一国密算法的加解密处理参数,得到第二公钥、第二私钥和第二随机数;通过第一方利用第二国密算法、第一公钥、第一随机数对第一本地数据进行加密处理,得到第一密文;通过第二方利用第二国密算法、第二公钥、第二随机数对第二本地数据进行加密处理,得到第二密文;通过第一方提取第一密文中的第一部分密文和第二部分密文,将第一部分密文发送给第二方;通过第二方提取第二密文中的第三部分密文和第四部分密文,通过第二公钥和第二随机数对第一部分密文进行加密,得到参考第一部分密文,提取参考第一部分密文的部分密文,得到目标第一部分密文;将第三部分密文和目标第一部分密文发送给第一方;通过第一方根据第三部分密文、目标第一部分密文和第二部分密文进行求交运算,得到交集结果,采用了国密算法,可以更自主可控,另外也扩充国密算法的应用场景。It can be seen that the national secret-based privacy set intersection method described in the embodiment of this application is applied to a two-party computing system. The two-party computing system includes a first party and a second party, and the first party corresponds to the first local Data, the second party corresponds to the second local data; the first party generates the encryption and decryption processing parameters of the first national secret algorithm to obtain the first public key, the first private key and the first random number; the second party generates the first Encryption and decryption processing parameters of the national secret algorithm to obtain the second public key, the second private key and the second random number; through the first party using the second national secret algorithm, the first public key and the first random number to pair the first local data Perform encryption processing to obtain the first ciphertext; use the second national secret algorithm, the second public key, and the second random number to encrypt the second local data through the second party to obtain the second ciphertext; extract the second ciphertext through the first party The first part of the ciphertext and the second part of the ciphertext in the first ciphertext, the first part of the ciphertext is sent to the second party; the third part of the ciphertext and the fourth part of the ciphertext in the second ciphertext are extracted by the second party, and the The second public key and the second random number encrypt the first part of the ciphertext to obtain the reference to the first part of the ciphertext, extract the part of the ciphertext that refers to the first part of the ciphertext, and obtain the first part of the target ciphertext; combine the third part of the ciphertext with the target The first part of the ciphertext is sent to the first party; the first party performs the intersection operation according to the third part of the ciphertext, the first part of the target ciphertext and the second part of the ciphertext, and obtains the intersection result, using the national secret algorithm, which can be more autonomous It is controllable, and it also expands the application scenarios of the national secret algorithm.
与上述实施例一致地,请参阅图4,图4是本申请实施例提供的一种电子设备的结构示意图,如图所示,该电子设备包括处理器、存储器、通信接口以及一个或多个程序,上述一个或多个程序被存储在上述存储器中,并且被配置由上述处理器执行,应用于两方计算系统,所述两方计算系统包括第一方和第二方,所述第一方对应第一本地数据,所述第二方对应第二本地数据;本申请实施例中,上述程序包括用于执行以下步骤的指令:Consistent with the above embodiment, please refer to FIG. 4, which is a schematic structural diagram of an electronic device provided by an embodiment of the present application. As shown in the figure, the electronic device includes a processor, a memory, a communication interface, and one or more program, the above-mentioned one or more programs are stored in the above-mentioned memory, and configured to be executed by the above-mentioned processor, applied to a two-party computing system, the two-party computing system includes a first party and a second party, and the first The party corresponds to the first local data, and the second party corresponds to the second local data; in the embodiment of the present application, the above program includes instructions for performing the following steps:
通过所述第一方生成第一国密算法的加解密处理参数,得到第一公钥、第一私钥和第一随机数;Generate the encryption and decryption processing parameters of the first national secret algorithm by the first party to obtain the first public key, the first private key and the first random number;
通过所述第二方生成所述第一国密算法的加解密处理参数,得到第二公钥、第二私钥和第二随机数;generating encryption and decryption processing parameters of the first national secret algorithm by the second party to obtain a second public key, a second private key and a second random number;
通过所述第一方利用第二国密算法、所述第一公钥、所述第一随机数对所述第一本地数据进行加密处理,得到第一密文;Encrypting the first local data by the first party using the second national secret algorithm, the first public key, and the first random number to obtain a first ciphertext;
通过所述第二方利用所述第二国密算法、所述第二公钥、所述第二随机数对所述第二本地数据进行加密处理,得到第二密文;Encrypting the second local data by the second party using the second national secret algorithm, the second public key, and the second random number to obtain a second ciphertext;
通过所述第一方提取所述第一密文中的第一部分密文和第二部分密文,将所述第一部分密文发送给所述第二方;extracting the first part of the ciphertext and the second part of the ciphertext from the first ciphertext by the first party, and sending the first part of the ciphertext to the second party;
通过所述第二方提取所述第二密文中的第三部分密文和第四部分密文,通过所述第二公钥和所述第二随机数对所述第一部分密文进行加密,得到参考第一部分密文,提取所述参考第一部分密文的部分密文,得到目标第一部分密文;将所述第三部分密文和所述目标第一部分密文发送给所述第一方;Extracting the third part of the ciphertext and the fourth part of the ciphertext in the second ciphertext by the second party, encrypting the first part of the ciphertext by using the second public key and the second random number, Obtaining the first partial ciphertext of the reference, extracting the partial ciphertext of the reference first partial ciphertext, and obtaining the target first partial ciphertext; sending the third partial ciphertext and the target first partial ciphertext to the first party ;
通过所述第一方根据所述第三部分密文、所述目标第一部分密文和所述第二部分密文进行求交运算,得到交集结果。An intersection result is obtained by the first party performing an intersection operation according to the third part of the ciphertext, the target first part of the ciphertext, and the second part of the ciphertext.
可选的,在所述通过所述第一方利用第二国密算法、所述第一公钥、所述第一随机数对所述第一本地数据进行加密处理,得到第一密文方面,上述程序包括用于执行以下步骤的指令:Optionally, in the aspect of obtaining the first ciphertext by encrypting the first local data by the first party using the second national secret algorithm, the first public key, and the first random number , the above program includes instructions to perform the following steps:
通过所述第一方利用所述第二国密算法对所述第一本地数据进行哈希运算,得到第一哈希运算结果;performing a hash operation on the first local data by the first party using the second national secret algorithm to obtain a first hash operation result;
利用所述第一公钥和所述第一随机数对所述第一哈希运算结果进行加密处理,得到所述第一密文。Encrypting the first hash operation result by using the first public key and the first random number to obtain the first ciphertext.
可选的,在所述通过所述第二方利用所述第二国密算法、所述第二公钥、所述第二随机数对所述第二本地数据进行加密处理,得到第二密文方面,上述程序包括用于执行以下步骤的指令:Optionally, the second party uses the second national secret algorithm, the second public key, and the second random number to encrypt the second local data to obtain a second secret key. In this regard, the above program includes instructions for performing the following steps:
通过所述第二方利用所述第二国密算法对所述第二本地数据进行哈希运算,得到第二哈希运算结果;performing a hash operation on the second local data by the second party using the second national secret algorithm to obtain a second hash operation result;
利用所述第二公钥和所述第二随机数对所述第二哈希运算结果进行加密处理,得到所述第二密文。Encrypting the second hash operation result by using the second public key and the second random number to obtain the second ciphertext.
可选的,在所述第一加密算法为sm2算法时,在所述通过所述第一方提取所述第一密文中的第一部分密文和第二部分密文方面,上述程序包括用于执行以下步骤的指令:Optionally, when the first encryption algorithm is the sm2 algorithm, in terms of extracting the first part of the ciphertext and the second part of the ciphertext in the first ciphertext through the first party, the above program includes Instructions to perform the following steps:
通过所述第一方利用第一椭圆曲线参数对所述第一密文进行密文提取,得到第一C1密文、第一C2密文和第一C3密文;performing ciphertext extraction on the first ciphertext by using the first elliptic curve parameters by the first party to obtain the first C1 ciphertext, the first C2 ciphertext and the first C3 ciphertext;
将所述第一C2密文确定为所述第一部分密文;determining the first C2 ciphertext as the first partial ciphertext;
将所述第一C1密文和所述第一C3密文进行拼接,得到所述第二部分密文。Splicing the first C1 ciphertext and the first C3 ciphertext to obtain the second part of ciphertext.
可选的,在所述通过所述第二方提取所述第二密文中的第三部分密文和第四部分密文方面,上述程序包括用于执行以下步骤的指令:Optionally, in terms of extracting the third part of ciphertext and the fourth part of ciphertext in the second ciphertext through the second party, the above program includes instructions for performing the following steps:
通过所述第二方利用第二椭圆曲线参数对所述第二密文进行密文提取,得到第二C1密文、第二C2密文和第二C3密文;performing ciphertext extraction on the second ciphertext by using the second elliptic curve parameters by the second party to obtain a second C1 ciphertext, a second C2 ciphertext, and a second C3 ciphertext;
将所述第二C2密文确定为所述第三部分密文;determining the second C2 ciphertext as the third partial ciphertext;
将所述第二C1密文和所述第二C3密文进行拼接,得到所述第二部分密文。Splicing the second C1 ciphertext and the second C3 ciphertext to obtain the second part of ciphertext.
可选的,在所述通过所述第一方根据所述第三部分密文、所述目标第一部分密文和所述第二部分密文进行求交运算,得到交集结果方面,上述程序包括用于执行以下步骤的指令:Optionally, in terms of obtaining an intersection result by performing an intersection operation by the first party according to the third part of the ciphertext, the first part of the target ciphertext, and the second part of the ciphertext, the above procedure includes Instructions to perform the following steps:
通过所述第一方将所述第二部分密文和所述目标第一部分密文进行拼接,得到拼接密文;Splicing the second part of the ciphertext and the target first part of the ciphertext through the first party to obtain the spliced ciphertext;
利用所述第一私钥解密所述拼接密文,得到解密结果;Decrypting the concatenated ciphertext by using the first private key to obtain a decryption result;
将所述解密结果与所述第三部分密文进行求交运算,得到交集结果。Perform an intersection operation on the decryption result and the third part of the ciphertext to obtain an intersection result.
本申请实施例还提供一种计算机存储介质,其中,该计算机存储介质存储用于电子数据交换的计算机程序,该计算机程序使得计算机执行如上述方法实施例中记载的任一方法的部分或全部步骤,上述计算机包括电子设备。An embodiment of the present application also provides a computer storage medium, wherein the computer storage medium stores a computer program for electronic data exchange, and the computer program enables the computer to execute some or all of the steps of any method described in the above method embodiments , the above-mentioned computer includes electronic equipment.
本申请实施例还提供一种计算机程序产品,上述计算机程序产品包括存储了计算机程序的非瞬时性计算机可读存储介质,上述计算机程序可操作来使计算机执行如上述方法实施例中记载的任一方法的部分或全部步骤。该计算机程序产品可以为一个软件安装包,上述计算机包括电子设备。An embodiment of the present application also provides a computer program product, the computer program product includes a non-transitory computer-readable storage medium storing a computer program, and the computer program is operable to enable the computer to execute any one of the methods described in the above method embodiments. Some or all steps of the method. The computer program product may be a software installation package, and the computer includes electronic equipment.
需要说明的是,对于前述的各方法实施例,为了简单描述,故将其都表述为一系列的动作组合,但是本领域技术人员应该知悉,本申请并不受所描述的动作顺序的限制,因为依据本申请,某些步骤可以采用其他顺序或者同时进行。其次,本领域技术人员也应该知悉,说明书中所描述的实施例均属于优选实施例,所涉及的动作和模块并不一定是本申请所必须的。It should be noted that for the foregoing method embodiments, for the sake of simple description, they are expressed as a series of action combinations, but those skilled in the art should know that the present application is not limited by the described action sequence. Depending on the application, certain steps may be performed in other orders or simultaneously. Secondly, those skilled in the art should also know that the embodiments described in the specification belong to preferred embodiments, and the actions and modules involved are not necessarily required by this application.
在上述实施例中,对各个实施例的描述都各有侧重,某个实施例中没有详述的部分,可以参见其他实施例的相关描述。In the foregoing embodiments, the descriptions of each embodiment have their own emphases, and for parts not described in detail in a certain embodiment, reference may be made to relevant descriptions of other embodiments.
在本申请所提供的几个实施例中,应该理解到,所揭露的装置,可通过其它的方式实现。例如,以上所描述的装置实施例仅仅是示意性的,例如上述单元的划分,仅仅为一种逻辑功能划分,实际实现时可以有另外的划分方式,例如多个单元或组件可以结合或者可以集成到另一个系统,或一些特征可以忽略,或不执行。另一点,所显示或讨论的相互之间的耦合或直接耦合或通信连接可以是通过一些接口,装置或单元的间接耦合或通信连接,可以是电性或其它的形式。In the several embodiments provided in this application, it should be understood that the disclosed device can be implemented in other ways. For example, the device embodiments described above are only illustrative. For example, the division of the above units is only a logical function division. In actual implementation, there may be other division methods, for example, multiple units or components can be combined or integrated. to another system, or some features may be ignored, or not implemented. In another point, the mutual coupling or direct coupling or communication connection shown or discussed may be through some interfaces, and the indirect coupling or communication connection of devices or units may be in electrical or other forms.
上述作为分离部件说明的单元可以是或者也可以不是物理上分开的,作为单元显示的部件可以是或者也可以不是物理单元,即可以位于一个地方,或者也可以分布到多个网络单元上。可以根据实际的需要选择其中的部分或者全部单元来实现本实施例方案的目的。The units described above as separate components may or may not be physically separated, and the components displayed as units may or may not be physical units, that is, they may be located in one place, or may be distributed to multiple network units. Part or all of the units can be selected according to actual needs to achieve the purpose of the solution of this embodiment.
另外,在本申请各个实施例中的各功能单元可以集成在一个处理单元中,也可以是各个单元单独物理存在,也可以两个或两个以上单元集成在一个单元中。上述集成的单元既可以采用硬件的形式实现,也可以采用软件功能单元的形式实现。In addition, each functional unit in each embodiment of the present application may be integrated into one processing unit, each unit may exist separately physically, or two or more units may be integrated into one unit. The above-mentioned integrated units can be implemented in the form of hardware or in the form of software functional units.
上述集成的单元如果以软件功能单元的形式实现并作为独立的产品销售或使用时,可以存储在一个计算机可读取存储器中。基于这样的理解,本申请的技术方案本质上或者说对现有技术做出贡献的部分或者该技术方案的全部或部分可以以软件产品的形式体现出来,该计算机软件产品存储在一个存储器中,包括若干指令用以使得一台计算机设备(可为个人计算机、服务器或者网络设备等)执行本申请各个实施例上述方法的全部或部分步骤。而前述的存储器包括:U盘、只读存储器(ROM,Read-Only Memory)、随机存取存储器(RAM,Random Access Memory)、移动硬盘、磁碟或者光盘等各种可以存储程序代码的介质。If the above-mentioned integrated units are realized in the form of software function units and sold or used as independent products, they can be stored in a computer-readable memory. Based on this understanding, the technical solution of the present application is essentially or part of the contribution to the prior art, or all or part of the technical solution can be embodied in the form of a software product, and the computer software product is stored in a memory. Several instructions are included to make a computer device (which may be a personal computer, server or network device, etc.) execute all or part of the steps of the above-mentioned methods in various embodiments of the present application. The aforementioned memory includes: U disk, read-only memory (ROM, Read-Only Memory), random access memory (RAM, Random Access Memory), mobile hard disk, magnetic disk or optical disk and other media that can store program codes.
本领域普通技术人员可以理解上述实施例的各种方法中的全部或部分步骤是可以通过程序来指令相关的硬件来完成,该程序可以存储于一计算机可读存储器中,存储器可以包括:闪存盘、只读存储器(英文:Read-Only Memory,简称:ROM)、随机存取器(英文:RandomAccess Memory,简称:RAM)、磁盘或光盘等。Those of ordinary skill in the art can understand that all or part of the steps in the various methods of the above-mentioned embodiments can be completed by instructing related hardware through a program, and the program can be stored in a computer-readable memory, and the memory can include: a flash disk , Read-only memory (English: Read-Only Memory, abbreviated: ROM), random access device (English: Random Access Memory, abbreviated: RAM), magnetic disk or optical disk, etc.
以上对本申请实施例进行了详细介绍,本文中应用了具体个例对本申请的原理及实施方式进行了阐述,以上实施例的说明只是用于帮助理解本申请的方法及其核心思想;同时,对于本领域的一般技术人员,依据本申请的思想,在具体实施方式及应用范围上均会有改变之处,综上所述,本说明书内容不应理解为对本申请的限制。The embodiments of the present application have been introduced in detail above, and specific examples have been used in this paper to illustrate the principles and implementation methods of the present application. The descriptions of the above embodiments are only used to help understand the methods and core ideas of the present application; meanwhile, for Those skilled in the art will have changes in specific implementation methods and application scopes based on the ideas of the present application. In summary, the contents of this specification should not be construed as limiting the present application.
Claims (4)
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202210876365.5A CN115242514B (en) | 2022-07-25 | 2022-07-25 | Method, system, electronic device, and storage medium for seeking intersection of private sets based on national secrets |
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| CN202210876365.5A CN115242514B (en) | 2022-07-25 | 2022-07-25 | Method, system, electronic device, and storage medium for seeking intersection of private sets based on national secrets |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| CN115242514A CN115242514A (en) | 2022-10-25 |
| CN115242514B true CN115242514B (en) | 2023-03-07 |
Family
ID=83675055
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| CN202210876365.5A Active CN115242514B (en) | 2022-07-25 | 2022-07-25 | Method, system, electronic device, and storage medium for seeking intersection of private sets based on national secrets |
Country Status (1)
| Country | Link |
|---|---|
| CN (1) | CN115242514B (en) |
Families Citing this family (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN115913537B (en) * | 2022-11-10 | 2025-08-08 | 深圳市洞见智慧科技有限公司 | Data intersection method, system and related equipment based on privacy protection |
| CN115834189B (en) * | 2022-11-17 | 2025-09-23 | 深圳市洞见智慧科技有限公司 | Privacy intersection method, device and related products in low-bandwidth environment |
| CN115801261B (en) * | 2023-01-15 | 2023-04-25 | 三未信安科技股份有限公司 | Ciphertext intersection method based on cryptographic algorithm |
| CN117155539B (en) * | 2023-10-31 | 2024-01-30 | 浙江大学 | Obfuscation of analog radio frequency circuit netlists and recovery methods, devices, terminals and media |
Citations (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN109040076A (en) * | 2018-08-09 | 2018-12-18 | 腾讯科技(深圳)有限公司 | A kind of data processing method, system, device, equipment and medium |
| CN112003695A (en) * | 2020-08-11 | 2020-11-27 | 天翼电子商务有限公司 | Privacy set intersection method, system, medium, and apparatus |
| CN113225186A (en) * | 2021-05-31 | 2021-08-06 | 平安科技(深圳)有限公司 | Private data intersection solving method and device, computer equipment and storage medium |
| CN114640444A (en) * | 2022-03-18 | 2022-06-17 | 哈尔滨理工大学 | Privacy protection set intersection acquisition method and device based on domestic cryptographic algorithm |
Family Cites Families (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| KR102763450B1 (en) * | 2019-12-24 | 2025-02-07 | 삼성에스디에스 주식회사 | Apparatus and method for set intersection operation |
-
2022
- 2022-07-25 CN CN202210876365.5A patent/CN115242514B/en active Active
Patent Citations (4)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| CN109040076A (en) * | 2018-08-09 | 2018-12-18 | 腾讯科技(深圳)有限公司 | A kind of data processing method, system, device, equipment and medium |
| CN112003695A (en) * | 2020-08-11 | 2020-11-27 | 天翼电子商务有限公司 | Privacy set intersection method, system, medium, and apparatus |
| CN113225186A (en) * | 2021-05-31 | 2021-08-06 | 平安科技(深圳)有限公司 | Private data intersection solving method and device, computer equipment and storage medium |
| CN114640444A (en) * | 2022-03-18 | 2022-06-17 | 哈尔滨理工大学 | Privacy protection set intersection acquisition method and device based on domestic cryptographic algorithm |
Non-Patent Citations (1)
| Title |
|---|
| 面向隐私保护的集合交集计算综述;魏立斐,刘纪海,张蕾,王勤,贺崇德;《计算机研究与发展》;20211118;1782-1799 * |
Also Published As
| Publication number | Publication date |
|---|---|
| CN115242514A (en) | 2022-10-25 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| CN115242514B (en) | Method, system, electronic device, and storage medium for seeking intersection of private sets based on national secrets | |
| WO2022252632A1 (en) | Data encryption processing method and apparatus, computer device, and storage medium | |
| CN107196926B (en) | A kind of cloud outsourcing privacy set comparison method and device | |
| CN107395368B (en) | Digital signature method, decapsulation method and decryption method in media-free environment | |
| CN115269938B (en) | Homomorphic encryption-based keyword track hiding query method, system and related device | |
| CN107248984A (en) | Data exchange system, method and apparatus | |
| CN114726597A (en) | Data transmission method, device, system and storage medium | |
| WO2020224138A1 (en) | Blockchain technology-based multi-party authorization method and device | |
| CN116032667B (en) | Online stealth inquiry method, system and related equipment supporting efficient updating | |
| CN115580489B (en) | Data transmission method, device, equipment and storage medium | |
| US12132838B2 (en) | Secret code verification protocol | |
| CN115225266A (en) | Multi-party threshold privacy set intersection method and system based on cloud server assistance | |
| CN110912683B (en) | Password storage method and device and password verification method and device | |
| CN113965314B (en) | Homomorphic encryption processing method and related equipment | |
| CN121173563A (en) | Copyright file chaining method and device, electronic equipment, storage medium and product | |
| CN112019335B (en) | A multi-party collaborative encryption and decryption method and device, system and medium based on SM2 algorithm | |
| CN108881300A (en) | A kind of file encryption that supporting mobile phone terminal security cooperation and sharing method and system | |
| CN117077156B (en) | Data processing method and electronic device | |
| CN116595562B (en) | Data processing method and electronic equipment | |
| CN116894268A (en) | High-performance privacy intersection methods, systems and related equipment for massive data | |
| JP2022053676A (en) | Information processing system and information processing method | |
| CN107707611B (en) | Power data cloud processing method, device and system | |
| CN116308350A (en) | Homomorphic encryption-based private transaction method, device and related products | |
| CN115225250A (en) | Outsourced decryption system and method for ciphertext data based on homomorphic encryption | |
| CN112348674A (en) | Block chain transaction data storage and acquisition method and device |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PB01 | Publication | ||
| PB01 | Publication | ||
| SE01 | Entry into force of request for substantive examination | ||
| SE01 | Entry into force of request for substantive examination | ||
| GR01 | Patent grant | ||
| GR01 | Patent grant | ||
| CP03 | Change of name, title or address |
Address after: 071708 Hebei Province, Baoding City, China (Hebei) Free Trade Pilot Zone, Xiongan Area, Start-up Zone, Yining Street No. 164, North District of Innovation Park (Artificial Intelligence Industrial Park), Unit 4, 4th Floor, Room 418 Patentee after: Dongjin Technology (Xiongan) Co., Ltd. Country or region after: China Address before: 518000 Guangdong Province Shenzhen City Futian District Futian Street Gangxia Community Cai Tian Road 3069 Star River Century Building A 3603B8 Patentee before: Shenzhen Dongjian Intelligent Technology Co.,Ltd. Country or region before: China |
|
| CP03 | Change of name, title or address |