EP0647342B1 - Detection de contrefacons a l'aide de codes d'identification contenant des zones de chiffres aleatoires - Google Patents
Detection de contrefacons a l'aide de codes d'identification contenant des zones de chiffres aleatoires Download PDFInfo
- Publication number
- EP0647342B1 EP0647342B1 EP92911723A EP92911723A EP0647342B1 EP 0647342 B1 EP0647342 B1 EP 0647342B1 EP 92911723 A EP92911723 A EP 92911723A EP 92911723 A EP92911723 A EP 92911723A EP 0647342 B1 EP0647342 B1 EP 0647342B1
- Authority
- EP
- European Patent Office
- Prior art keywords
- authorized
- information
- distinct
- numbers
- identifying
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Expired - Lifetime
Links
Images
Classifications
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07F—COIN-FREED OR LIKE APPARATUS
- G07F7/00—Mechanisms actuated by objects other than coins to free or to actuate vending, hiring, coin or paper currency dispensing or refunding apparatus
- G07F7/08—Mechanisms actuated by objects other than coins to free or to actuate vending, hiring, coin or paper currency dispensing or refunding apparatus by coded identity card or credit card or other personal identification means
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07D—HANDLING OF COINS OR VALUABLE PAPERS, e.g. TESTING, SORTING BY DENOMINATIONS, COUNTING, DISPENSING, CHANGING OR DEPOSITING
- G07D7/00—Testing specially adapted to determine the identity or genuineness of valuable papers or for segregating those which are unacceptable, e.g. banknotes that are alien to a currency
- G07D7/004—Testing specially adapted to determine the identity or genuineness of valuable papers or for segregating those which are unacceptable, e.g. banknotes that are alien to a currency using digital security elements, e.g. information coded on a magnetic thread or strip
- G07D7/0047—Testing specially adapted to determine the identity or genuineness of valuable papers or for segregating those which are unacceptable, e.g. banknotes that are alien to a currency using digital security elements, e.g. information coded on a magnetic thread or strip using checkcodes, e.g. coded numbers derived from serial number and denomination
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07D—HANDLING OF COINS OR VALUABLE PAPERS, e.g. TESTING, SORTING BY DENOMINATIONS, COUNTING, DISPENSING, CHANGING OR DEPOSITING
- G07D7/00—Testing specially adapted to determine the identity or genuineness of valuable papers or for segregating those which are unacceptable, e.g. banknotes that are alien to a currency
- G07D7/004—Testing specially adapted to determine the identity or genuineness of valuable papers or for segregating those which are unacceptable, e.g. banknotes that are alien to a currency using digital security elements, e.g. information coded on a magnetic thread or strip
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07D—HANDLING OF COINS OR VALUABLE PAPERS, e.g. TESTING, SORTING BY DENOMINATIONS, COUNTING, DISPENSING, CHANGING OR DEPOSITING
- G07D7/00—Testing specially adapted to determine the identity or genuineness of valuable papers or for segregating those which are unacceptable, e.g. banknotes that are alien to a currency
- G07D7/004—Testing specially adapted to determine the identity or genuineness of valuable papers or for segregating those which are unacceptable, e.g. banknotes that are alien to a currency using digital security elements, e.g. information coded on a magnetic thread or strip
- G07D7/0043—Testing specially adapted to determine the identity or genuineness of valuable papers or for segregating those which are unacceptable, e.g. banknotes that are alien to a currency using digital security elements, e.g. information coded on a magnetic thread or strip using barcodes
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07D—HANDLING OF COINS OR VALUABLE PAPERS, e.g. TESTING, SORTING BY DENOMINATIONS, COUNTING, DISPENSING, CHANGING OR DEPOSITING
- G07D7/00—Testing specially adapted to determine the identity or genuineness of valuable papers or for segregating those which are unacceptable, e.g. banknotes that are alien to a currency
- G07D7/06—Testing specially adapted to determine the identity or genuineness of valuable papers or for segregating those which are unacceptable, e.g. banknotes that are alien to a currency using wave or particle radiation
- G07D7/12—Visible light, infrared or ultraviolet radiation
Definitions
- the invention disclosed herein relates to counterfeit detection methods.
- counterfeited When an object, such as a product or document, is worth disproportionately more than the cost of its manufacture, it may be counterfeited at a profit. For example, manufacturers of proprietary products lose billions of dollars each year because their most successful products are often targeted by counterfeiters who produce spurious goods locally or overseas. When counterfeit goods are of similar or identical quality to the original, a manufacturer suffers from a continuous loss of sales as counterfeiting continues unchecked, because detection is difficult or impossible. Inferior counterfeit products may be more easily detected, but in addition to the above, they also jeopardize future sales of non-counterfeited products by marring reputation. In either case, the manufacturer's continuing level of untold lost profits due to counterfeit may be dramatic. Similar concerns arise with counterfeit documents.
- a partial listing of products susceptible to being counterfeited includes: airplane parts; art; auto parts; baby products ⁇ formula, diapers, clothing; books; computers; computer peripherals; cosmetics; designer goods ⁇ clothing, shoes, eye glasses; electronics; entertainment recordings ⁇ CDs, records, audio and video cassettes; games ⁇ board, firmware, handheld; military parts; optics ⁇ binoculars, cameras; pharmaceuticals; software; tools; toys; watches.
- Documents susceptible to fraud include: betting tickets (lottery, sports, etc); bonds (Treasury, commercial, etc); certificates (birth, gift, warranty, etc); checks (personal, commercial, travelers, etc); coupons; credit cards; currency; licenses (driver, business, import/export, etc); passports; scrip (store, amusement park, etc); stamps (postage, food, etc); stocks; tickets (concerts, sports, theater, etc); travel tickets (airline, commuter, etc), and so forth.
- Intellectual counterfeit detection and/or authentication techniques may include signatures, numbers and/or other indicia for coding each genuine object differently.
- the underlying principle here is uniqueness.
- Each genuine object is individually signed, or assigned individual identifying information.
- Traditional ways to individually authenticate objects are: sign or assign.
- Blank checks available at stationery stores, for example, may be authorized by John Smith's signature if he is known, or if that signature is verifiable, perhaps by comparison to other signed documents.
- Signatures for example, bridge mechanical and intellectual techniques, involving examination-by-eye.
- Applicants' anti-counterfeit techniques address mass produced objects, unsigned products and documents, manufactured to be essentially identical to each other ⁇ the only convenient and distinguishable difference among such essentially identical objects being the presence of associated identifying information, such as serial numbers.
- Mr. Smith's signed check may involve other variable information.
- the dollar amount, the transaction date, payee information, Mr. Smith's address and bank account number, information about his bank, and so forth examples of other articles with variable parameters are: birth certificates, credit cards, lottery tickets, passports, etc.
- serial numbers Another traditional way to uniquely identify objects is to assign serial numbers, by counting, in a most convenient and orderly fashion.
- serial numbers offer little obstacle to a counterfeiter because he can, for example, assign matching ascending and descending numbers given one correct serial number as a start, thereby duplicating authorized numbers only once. Even if two objects with matching serial numbers were found, thereby finding at least one counterfeit, mechanical techniques may still be required to tell which is counterfeit.
- counterfeiters could avoid following a pattern that may be helpful to pursuing authorities if the pattern were discovered. For example, rather than serially numbering their fakes, counterfeiters may randomly select numbering within a wide range of known-to-be valid numbers, so that the possibility of a particular consecutive narrow range of serial numbers being discovered by authorities as having been counterfeited is avoided, making the job most difficult for the authorities (albeit more difficult, but safer, for the counterfeiters as well).
- intellectual coding techniques may also offer "self-checking" counterfeit detection schemes (self-checking is a term used with error control coding, adopted for use by applicants when referring to certain intellectual anti-counterfeit coding techniques).
- self-checking is a term used with error control coding, adopted for use by applicants when referring to certain intellectual anti-counterfeit coding techniques.
- Applicants define self-checking as follows: if a single read identifying number does not conform to a secret code, or match up in a database, it must be counterfeit.
- McNeight et al. provides objects with authorized ID numbers that conform to an algorithm or code, so that these ID numbers may be verified or tested for apparent authenticity using the same algorithm.
- the algorithm is cautiously deployed in locations where it is desirable to detect counterfeit by determining if an object's ID number conforms to the secret algorithm. Caution is required in order to prevent theft or discovery of the algorithm.
- Authorized ID numbers conform to the algorithm, but the algorithm itself is selected and/or used so that it does not readily allow easy discovery or reverse engineering of the originating algorithm.
- the algorithm must be kept secret so that it is not also used by unauthorized personnel.
- White's invention concerns security for checks and other transactions involving money.
- White uses a table of random numbers. The same table of random numbers is associated both with a portable transaction device and with a bank's central processor.
- a random number is selected from the table in the transaction device and used to encode the dollar amount of the particular check using an encryption algorithm.
- the calculated result, a security code is then put on the check.
- the authenticity of the security code on such a check may be verified, by recalculating the security code again, in the same manner, in the bank's central processor, and comparing the two security codes for a match.
- each genuine object is assigned a different authorized identifying code.
- Counterfeit is detected when incorrect, repeated or out-of-place ID numbers are found on objects.
- ID numbers which are associated with objects may be represented in normal alphanumeric characters or otherwise, such as OCR or MICR fonts of alphanumeric characters, decimal characters, or bar coded characters, etc., which are designed to be machine read, and may be visible or substantially transparent.
- an object's identifying serial number may be appended with one or more distinct random portions, positioned to the right of the serial portion, for example, with or without a decimal point (or binary point if binary were being used) or positioned preceding the serial number, or the serial portion may be understood as including one or more random portions, etc.
- a truncated security ID number comprised of a distinct serial number portion and a first random portion, may be used, for example, on the outside of a product package, and a complete security ID number, with a second random portion along with the serial number and said first random portion, used inside a product's packaging (concealing the complete ID number from casual perusal) such as on a product's enclosed return warranty registration card.
- Each distinct random portion may include one or more randomly selected digits.
- Objects of the invention disclosed herein are to protect proprietary product and document integrity, quality, reliability, safety, authenticity and the like, by creating hurdles for would-be counterfeiters, and thereby reducing or eliminating such illegal, dangerous and/or economically devastating activity.
- Other objects of the invention are to improve counterfeit detection and/or deterrence, to apprehend and/or track criminals and/or deter crime.
- the present invention provides methods and systems for identifying unauthorised objects, as defined separately in dependent claims 1 to 6, 9 and 11.
- Counterfeit products may be detected by looking for duplicate registration of normal serial numbers.
- this procedure leaves something to be desired, because counterfeit cannot be detected via the serial number until two (or more) of the same serial numbers are eventually registered, and even so, when two of the same serial numbers do turn up, an investigation must first be made to determine if one is genuine (as both may be fake) and if so, which one.
- a counterfeit product is positively detected and the vendor who sold the counterfeit product is identified by the product registrant, it may still be impossible, or cumbersome at best, to determine if other products in the vendor's stock are also counterfeit.
- physical examination procedures would likely be "intrusive" and may render examined products unfit for retail sale.
- Applicants' telling anti-counterfeit technique overcomes these shortcomings: registration involving just one ID number on a counterfeit product can immediately and unmistakably be identified as fake, and even before a "lead" from the registration process, counterfeit products can be positively identified on the retail shelf or in mail order inventory warehouses or distribution channels, etc., without opening the product's packaging.
- ID numbers include a serial portion and one or more random portions appended to, or associated with, the serial portion.
- Such ID numbers have the serial portion in predefined digit positions, so that ID numbers may be used just as orderly and conveniently as traditional serial numbers.
- the serial number portion (which may be called the serial field) of the ID number is appended with one or more random portions (each random portion may be called a random field).
- Each random portion may contain one or more randomly selected digits.
- a random number generator may be used which may, e.g., randomly select digits based on cosmic noise.
- Required randomly selected numbers may be provided on-the-fly, as needed, and then stored if required or erased if not required. Or, required randomly selected numbers may be generated and stored in a list and the list then referred to as required. It may be useful for random portions to be separated from the serial portion by a decimal point, for example.
- serial random number (SRN) shown on the Product Return Card in Fig. 1 is: 123456 23 17
- this ID number, 123456 23 17, is associated with a genuine product.
- the first six digits of the ID number, 123456 comprise a traditional sequential serial number with sufficient range to uniquely identify one million genuine products, from 000000 to 999999.
- the next four digits, in this example 23 and 17 are randomly selected, and stored in a file, such as a computer file, perhaps a file associated with a database system, along with the traditional serial number portion, to form a file listing of complete authorized ID numbers.
- authorized ID numbers are also stored separately, e.g., on a list stored in a computer file. Because of the serial portion, the list of complete authorized ID numbers is as orderly as can be, and because of the randomly selected parts, it is also unpredictable as described.
- a product's ID number e.g., 123456 23 17
- the random digits can be checked automatically ⁇ if they do not all match those which were originally stored, a counterfeit product's unauthorized ID number is positively and immediately detected.
- the product registration system computer may also be used by investigators looking for counterfeit, without need for registration and/or return cards, as described below.
- ID numbers may also be put on the outside of product packaging.
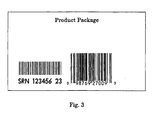
- the truncated serial random number (SRN) which corresponds in part to the ID number indicia shown in Fig. 1, is shown in Fig. 2 on the Product Package as: 123456 23 The reason for truncation is described below.
- ID numbers on the outside of product packaging makes them readily accessible, and allows a "shopping" service contracted by the product's manufacturer, or an investigator, to read and store bar coded ID numbers from products, e.g., on store shelves, and then send them, for example using a modem, to the manufacturer's system registration computer where the randomly selected portion of the ID numbers read from products can be checked against the stored list of complete authorized ID numbers, so that unauthorized ID numbers from counterfeit products may be detected.
- counterfeit products may be identified even before customer purchase, and authorities may be put on the trail of the perpetrators sooner. In enforcement proceedings, even good leads can get cold.
- applicants' counterfeit product detection system could be set up to include handheld devices that combine radio communication capability with bar code reading (e.g., the LRT 3800, which also includes portable computer terminal capabilities, in a handheld unit, a product of Symbol Technologies Inc., of Bohemia, New York) so that counterfeit could be detected at about the speed of light while an investigator points the device at a product being checked for authenticity.
- the LRT 3800 device reads and interprets the ID number bar code on a product that may be counterfeit, radio communicates this information to the product registration system computer to automatically check the ID number's random digit(s) to see if they match what was originally stored, and then receives back from the computer an indication if the ID number is unauthorized, thereby detecting counterfeit.
- Federal Express uses bar code reading and communication devices, and sometimes a communication satellite, in a package tracking system (see Automatic ID News Vol. 7, #2, 2/91, pg. 16). With such devices working with a central anti-counterfeit computer system, for example, counterfeit could be detected quickly, on a shelf in a location being checked for having counterfeit product, at a U.S. border in a routine or special Customs inspection, and so forth.
- ID numbers located on the outside of packaging are more accessible than ID numbers located inside the packaging, and may therefore more readily allow the possibility of a counterfeiter acquiring authorized ID numbers from the outside of genuine product packaging than from the inside (this may not be a significant risk in all cases).
- a counterfeiter might bribe someone in a distributor's shipping/receiving department to accumulate "outside" authorized ID numbers with a concealable bar code reader so that they could be used later on counterfeit products. If this happened, the manufacturer could be back where he started, looking for duplicates, suffering the shortcomings mentioned above, or perhaps even being worse off because of a false sense of security.
- the complete authorized ID number, 123456 23 17, is printed on the return registration card (as shown in Fig. 1) which is located inside the package and is therefore less accessible than the ID number located on the outside of packaging, thus concealing the complete authorized ID number from casual perusal. For example, if a product is in its original packaged condition, an ID number with associated random portions located inside the packaging would be concealed.
- a list (e.g., a partial listing limited to specific ranges of serial numbers, and/or selected geographical and/or chronological parameters, etc.) of authorized outside ID numbers (in the above example, 123456 23) might be supplied in a portable, non-communicating unit to investigators for use in the field as described below.
- authorized outside ID numbers in the above example, 123456 23
- portable, non-communicating unit might be supplied in a portable, non-communicating unit to investigators for use in the field as described below.
- specially trusted investigators only would be supplied with such "portable" lists, and/or such lists may only be supplied just prior to an investigation at a given location, and/or such lists may only be supplied in units that automatically erase the list after a given amount of time has elapsed and/or at a specified time, etc.
- this embodiment is less of a security exposure than supplying complete ID numbers for use in the field, especially if only a limited, partial listing is provided. For example, even if a portable list was acquired and used by counterfeiters, more complete ID numbers, such as those from a return card, would still expose the crime.
- counterfeit objects may be detected immediately, in the field, by comparing ID numbers read from a product's packaging directly against the list to determine if the correct random field for a respective serial number field is present on a product's package, without checking with the central computer where the master list of complete ID numbers is stored, on-site so to speak, no communications required, using a portable unit (much as checking a hot list, described below).
- ID numbers read from a product's packaging directly against the list to determine if the correct random field for a respective serial number field is present on a product's package, without checking with the central computer where the master list of complete ID numbers is stored, on-site so to speak, no communications required, using a portable unit (much as checking a hot list, described below).
- a return card's complete ID number, or just the random security part(s) may also be concealed, e.g., with latex covering, like the VIRN number (Void If Removed Number) on an instant lottery garre ticket, or the ID number may only be represented on the card in a customized "secret" bar code format.
- VIRN number Void If Removed Number
- Variations are possible. For example, if the possibility of a counterfeiter acquiring outside ID numbers during distribution exists, and return cards are not appropriate for a given product line, several such products may be packed for shipping in a sealed carton concealing the products' outside ID numbers during distribution.
- outside ID numbers can be put on such cartons, and latex-covered return from the retail vendor cards can be put in the carton (but not inside individual product packaging).
- 123456_ 23 17 79 10 The blank ligit position shown with an underline is described below. 123456 23 may be put on the outside of a shipping carton containing ten products. 123456 23 17 may be latex-covered and put on a return from the retail vendor card and located inside the carton, but not inside individual product packaging.
- Ten ID numbers using 123456_ 23 17 79 may be used as follows, one on the outside of each product package:
- Each product may also have a return card inside its packaging, each with one of the following ID numbers:
- ID numbers Because of the difference in the number of digits in ID numbers for respective locations, when ID numbers are read it may readily be automatically determined by apparatus where that ID number was read from, whether from the outside of the carton of ten products, from inside the carton on the carton's return card, from on the outside of an individual product or from the return card inside the individual product package.
- 123456 23 may be used on the outside of the carton of ten products, only 123456 17 may be used on the carton's return card (instead of 123456 23 17).
- 1234560 79 (the first of ten similar ID numbers corresponding to the above) may be used on the outside of an individual product, and 1234560 10 (again, the first of ten) used on the return card inside an individual product package.
- ID number (with a sixteen digit serial field and five fields of two randomly selected digits each): 1234567812345678 23 17 79 10 55 were used for documents, for example, on U.S. currency.
- a file with the serial number portions and only the associated first random field, shown with 23 in this example, may be provided by the Bureau of Engraving and Printing to commercial banks for their general use in detecting counterfeit, a file of the random fields 23 17 provided to Federal Reserve Banks for their use, a file of the random fields 23 17 79 to the Treasury, FBI, CIA, etc., a file of the random fields 23 17 79 10 may be used exclusively by those most trusted in the Secret Service, and a file of all five random fields, 23 17 79 10 55 may be stored for safe keeping and used with extreme caution only if ever needed. In this manner, if sophisticated counterfeiting were to occur, authorities would know exactly where to start looking for culprits.
- ID numbers may be useful in some counterfeit detection applications to provide ID numbers verifiable in some fashion in accord with a secret algorithm. For example, this may be accomplished according to applicants' invention as described above, i.e., to append to a serial number one or more distinct portions that conform to one or more respective secret codes. Such portions may be called secret code fields. In addition, random fields may or may not also be appended to the ID number.
- one secret code field is appended to the serial number (random fields are not used in this first example).
- the secret code field is represented by the ?? (the appended secret code field being undetermined thus far).
- the second example uses two appended random fields (each random field has two randomly selected digits in these examples) and one appended secret code field (containing two digits that result from calculating a code in these exarr ples) all three of which (fields) are used in a manner independent of each other.
- the secret code field is represented by the ?? (the appended secret code field being undetermined thus far).
- the following technique may be employed to calculate the secret code field for both the first and second example.
- the random digits used for calculating the secret algorithm need not be disseminated at all.
- the random digits used for calculating need not be put on the authorized objects themselves. Only some result of the secret algorithm calculation may be put on the authorized object and, according to the invention, the random digits required for the algorithm calculation stored only in the central computer, i.e., the random digits are stored in one location only. The advantage of this is reduced exposure of the random numbers, and increasing security for the secret code.
- the fourth example following uses the same secret code algorithm as the third example, but the random field represented by 17 in the third example is not used at all, and the random field represented by the 23 in the third example is used in calculating the algorithm in the central computer but it (23) is not put on the authorized object.
- serial numbers have only one respective random field which is only stored in the central computer and is not put on the object.
- the algorithm may be calculated for authorization and the result put on the object being authorized, and calculated again for verification.
- the random numbers need to be kept in storage to be used again in the calculation.
- the secret code field result of the calculation is put on the authorized object but need not be stored aside from the object. Therefore, in order to lessen exposure of sensitive information, means may be provided for automatically erasing the calculated secret code field results after being put on the authorized objects.
- the result when the algorithm is calculated for authorization and the result put on the object being authorized, the result could also be stored in the central computer, in association with the serial number, until needed again for verification of the authenticity of the object.
- verification then would work as follows: the serial number including the secret code field would be read from an object having its authenticity checked, and the reading compared in the central computer against the result that was previously calculated and stored for this serial number. A match indicates genuine.
- the random numbers are not needed again for calculating in this second embodiment of the fourth example, the random numbers need not be kept in storage after the authorization process. If the secret code field result of the calculation is stored, random numbers need not be. The random numbers may be erased after the calculation. Advantage: risk of exposure of the random numbers is then eliminated and this would tend to increase the difficulty in breaking the code, as mentioned above. Also, if the random numbers required for this second embodiment of the fourth example were only provided on-the-fly, as needed for the calculation, and erased immediately after the required calculation is completed, security would be increased. For example, means may be provided to automatically erase the random numbers after the calculation.
- security is increased because authorization and verification is performed in only one location, and the random numbers and/or the secret code and/or the secret code fields need not be disseminated beyond this central system nor stored longer than needed (except that ID numbers, however they are constructed, are associated with the authentic objects they protect) and therefore the risk of exposure of the random information and/or the secret algorithm and/or the secret code fields is lessened.
- the secret field is calculated, and verification may be accomplished, just as described for the fourth example, storing the required random digits safely in one location (according to the first embodiment) or storing the secret code field in one location (according to the second embodiment).
- the random digits, 17, are put on the object and stored in the central computer as described previously.
- the fifth example's ID number is completed as follows:
- the secret code is independent and random is not used at all.
- the secret code is used independently, and two random fields are used.
- the secret code is dependent on one random field (which is also put on the object) and one random field is independent of the secret code.
- the secret code is dependent on one random field but this random field is not put on the object; this random, or the secret code field, is stored in only one computer.
- the secret code is dependent on one random field but this random is not put on the object; the random, or the secret code field, is stored in only one computer, and one random field is independent of the secret code.
- a secret code may add significant difficulty for counterfeiters, i.e., in addition to other requirements, a counterfeiter would require knowledge of the secret code and he would be required to operate this code in order to provide correct ID numbers for his fakes. Some counterfeiting may therefore be deterred.
- One digit that cannot be anticipated is calculated using part of an object's six digit serial number and a random number.
- the random number is used in the calculation but it is not associated with the object in this example: 123456 ?
- the serial number portion is 123456.
- the digit that cannot be anticipated is represented by the ? as this digit is so far unknown but it will be calculated below.
- the serial number 123456 and the respective digit 6 may be used to designate one object among as many as 999,999 other essentially identical and identifiable objects in this example as authorized.
- each such object may be identified by a respective ID number which includes a six digit serial number portion.
- the resulting digit (6 in this example) cannot be anticipated.
- the randomly selected digit for serial number 123456, 9, which is used in the calculation may be stored and retrieved and used to recalculate the digit that cannot be anticipated (6) for verification.
- the digit that cannot be anticipated, 6, can be stored (aside from being associated with the object) and retrieved for verification purposes without recalculating the algorithm.
- a secret algorithm may also be used to provide a corresponding inside ID number, shown as, 123456 ??, which may be used, e.g., on a return card.
- 97 would be the final result for the secret code field for the corresponding inside ID number shown for this example: 123456 97.
- multiple secret code fields may also be used to provide different levels of counterfeit resistant ID numbers.
- Applicants' preferred anti-counterfeit system also checks for repeated ID numbers (inside, outside, etc). This prevents the possibility of one or a few authorized ID numbers used over and over going undetected. Repeated authorized ID numbers may be found, as well as repeated incorrect ID numbers. For example, two or more similar objects may be located with the same correct (or the same incorrect) ID numbers.
- Repeated ID numbers could be flagged in the system computer and put out on "hot” lists and automatically circulated to authorized investigators to allow “immediate” detection of each subsequent use, as described below. Or, for possible security reasons, it may be preferred to maintain hot lists only in the system computer. For example, a hot list of repeated valid ID numbers in New York may be useful to a counterfeiter in California, if, for example, California investigators did not have the hot list of repeated valid numbers that had been circulated to investigators in New York.
- Complete product distribution and shipment history may also be associated with applicants' anti-counterfeit system computer, and augmented with the registration process, so that, for example, any products reported stolen (prior to being sold to the public) may be flagged and backtracked to apprehend the culprits when the stolen products are ultimately registered.
- Product distribution information, along with registration information, may also be useful for marketing, accounting, inventory, automation control, quality control, and other purposes.
- Applicants' anti-counterfeit systems may be augmented and/or adapted for use to also detect product diversion, or gray marketing, as well as control problems with returns and seasonally packaged goods, product recalls for defects or tampered-with goods, etc.
- the U.S. Customs Service plays a large part in detecting counterfeit products at our nation's borders.
- applicants suggest that all companies should adopt uniform self-identifying bar code standards, of the type described in Table 1 (note Format F, 101, on Table 1, "Product or document 'Seal of Authenticity' service"), 1989, and should use common communication facilities and common counterfeit product computer system facilities. This would allow convenient means, for example, for U.S. Custom agents, as well as other investigators, to use the same bar code reading devices to check a variety of products for authenticity.
- a "Seal of Authenticity" and/or the addition of a product return card to confirm authenticity might become part of a product's enhanced, and thus more desirable, image, as well as an integral part of a product's marketing strategy.
- visible or invisible security ID number indicia may have, in possible association with a "Seal of Authenticity," on a would-be counterfeiter.
- the UPC symbol shown to the right of the security ID number in Fig. 3 is a photo reproduction of an actual UPC symbol from a product called Vistatector, which is a pen-like device that can detect counterfeit currency or other counterfeit documents, a product of a New York City company, Vistatech Enterprises, Limited.
- locating two distinct bar code symbols near each other such as a product's ID number and its UPC symbol, allows the possibility of an investigator reading the ID number in association with the UPC symbol, in the same reading or scanning operation, so that the product under scrutiny can be identified in accord with standard UPC product assignment coding, and individually identified for authenticity purposes with the ID number as described above.
- this may allow smaller ID number indicia on packaging to be sufficient, since general product identification may be made via the UPC symbol, and/or this may be helpful by automatically informing authenticity apparatus what kind of product is being scrutinized.
- ID number indicia such as shown in Fig. 2, or perhaps only the bar coded indicium of Fig. 2, substantially transparent, effectively invisible.
- Dolash et al.'s U.S. Pat. No. 4,983,817 describes how substantially transparent bar codes may be accurately read even though placed on top of visible printed text or even placed on top of a visible bar code symbol.
- a bar coded ID number may be printed in invisible ink directly over a standard UPC symbol on a product's packaging, or in convenient proximity therewith.
- one mode of operation (referred to as a "dual mode setting") of bar code scanning apparatus may require that two different bar code symbols (i.e., each individual symbol is complete unto itself and each can be read separately) such as a visible UPC symbol and an invisible ID number (either superimposed over the visible UPC symbol or just placed near the visible UPC symbol) or a visible UPC symbol and a visible ID number (as shown in Fig. 3) be successfully read before indicating a reading operation has been completed.
- two different bar code symbols i.e., each individual symbol is complete unto itself and each can be read separately
- two different bar code symbols i.e., each individual symbol is complete unto itself and each can be read separately
- a visible UPC symbol and an invisible ID number either superimposed over the visible UPC symbol or just placed near the visible UPC symbol
- a visible UPC symbol and a visible ID number (as shown in Fig. 3) be successfully read before indicating a reading operation has been completed.
- an audible beep and/or the lighting of an indicator light are often generated at the end of each bar code reading operation in order to indicate completion thereof.
- a signal indicating completion of the bar code reading operation would not be provided until both a visible UPC symbol and an invisible ID number (in one example) have been successfully read, i.e., a reading from one bar code symbol located near a second symbol is automatically delayed until the second is also read in the same reading operation or cycle (e.g., as ended with an associated beep).
- the dual mode setting for reading bar codes may operate as follows: when a mode selector switch is set to the dual mode position, the switch could clamp the signal that would normally indicate the completion of one bar code reading until a second signal indicates the completion of a second reading of another bar code symbol. Then, with both signals present, each indicating a completed reading of a respective bar code symbol, the clamp may be lifted (unclamped) allowing the beep to sound and/or the indicator light to be lighted, thus indicating that both bar code symbols had been read in this dual mode setting.
- Other operations could also be accomplished before an indication of the end of a reading operation, e.g., price look-up, inventory list augmentation, authenticity check, date check, comparison to lists of ID numbers being sought by enforcement authorities, etc.
- the dual mode setting operation may be used with bar code reading apparatus even if human operators are not involved in the bar code reading operation. For example, a signal indicating completion would not be provided to associated circuits (as would normally be done after one bar code symbol was read) until two symbols were read.
- the mode setting switch on bar code reading apparatus may select applicants' dual mode setting, and perhaps other settings as well, such as a single mode setting that anticipates a reading where only one bar code symbol per reading operation is present. For example, a setting where only the one UPC symbol will be read even if an invisible bar code is on top of it.
- an invisible ID number symbol placed over a product's UPC symbol can be used for detecting expired product.
- the date of the last-day-of-sale for limited shelf-life products may be stored in a supermarket's computer in association with ID numbers.
- the expiration date for ID number bearing Baby Safe Formula product, 3/21/91 may be stored in the computer along with the information that the 3/21/91 expiration date applies to Baby Safe Formula with ID numbers (serial portion only) 1,000,000 to 1,001,000.
- ID numbers from Baby Safe Formula are read at a check out counter and sent to the supermarket's computer, their expiration dates may be looked up, and/or authenticity may be checked (in real time or in a nocturnal batch processing operation, using the common communication and counterfeit product computer system facilities mentioned above) and/or various lists may be checked (price, inventory, stolen goods, counterfeit with repeated ID numbers, contaminated goods, etc.) etc.
- the light may be desirable to indicate whether one symbol or two different symbols have in fact been read. For example, when two bar code symbols are read, sound two beeps ("beep,beep" as opposed to “beep") and/or double blink the light repeatedly (blink,blink, pause, blink,blink, pause, blink,blink, ...) or light two lights or use colored lights, etc.
- An automatic dual mode setting on bar code scanning apparatus is first described for one visible and one invisible bar code symbol, using a visible UPC symbol and an invisible ID number.
- a bar code reading device could also sense for other bar code structure, as it senses for the UPC symbol. Sensing for this other bar code structure, of say, just a few bars and spaces, could be performed in a second invisible luminescent frequency band ⁇ that reflected by an invisible bar code.
- Dolash et al.'s U.S. Pat. No. 4,983,817 describes dual bar code detection means for reading two differing frequency bands, comprising optical filters, collection optics, light detectors, etc.
- the invisible superimposed bar code may be made at least as tall as the the UPC symbol underneath. and placed so that it spans at least part of this UPC symbol completely from top to bottom. Thus, at least part of the first invisible bar code symbol cannot be missed while reading the complete second visible symbol.
- Fig. 3 where one visible bar code symbol is located next to another as shown: if during a reading operation with scanning apparatus set in automatic dual mode setting, scan lines came from the right and encountered the complete UPC symbol of Fig. 3 without going sufficiently past to also encounter part of the ID number symbol to the left (the normal required quiet zone for the bar code symbols described in these examples is understood to be 1/4 inch or less) a reading of only the UPC symbol may be provided along with a beep indicating completion of the reading operation even though two symbols are present next to each other and should be read together.
- Scanning apparatus with automatic dual mode setting may be adjusted to work as follows: in automatic dual mode position the scan lines always go past the first bar code symbol encountered at least a fixed amount of, say effectively, 1/2 inch distance (this 1/2 inch being greater than what would otherwise be required for the quiet zone, as described). For example, referring back to Fig. 3, if during an automatic dual mode setting reading operation, scan lines came from the right and encountered the complete UPC symbol, the scan lines would continue at least 1/2 inch past the left end of the UPC symbol, traversing past the complete 3/8 inch space shown in Fig. 3, so that at least 1/8 inch part of the ID number symbol to the left of the UPC symbol is also encountered.
- apparatus proceeds on the basis that only the one UPC bar code symbol is present. For example, if scanning apparatus finds 1/2 inch of white space blank, the UPC code reading is provided and a beep would sound (once) and/or the indicator light would light (without blinking) after only one UPC symbol has been read, without undue pause.
- care may also be taken when printing single bar code symbols (that may be read singly in an automatic dual mode setting) to either use a quiet zone of 1/2 inch minimum or not to use printing text or other material within 1/2 inch that might be interpreted as a few bars and spaces. If, for example, text were printed 1/4 inch from one UPC symbol, and this text were interpreted to be a few bars and spaces in automatic dual mode setting, delay may result from looking for another symbol (which is not present).
- a scan line skewing effect is possible, similar to what may cause a short read [short reads may occur when a skewed scan line leaves or enters a symbol other than at the end(s) of the symbol] so that, still referring to Fig. 3, the ID number symbol may be missed by skewed scan lines reading the UPC symbol, or, in the example shown in Fig. 3, missed by high or low sufficiently horizontal scan lines because the ID number symbol is shown shorter (smaller) than the UPC symbol on both top and bottom.
- the ID number symbol may be made taller than shown in Fig. 3, tall enough to extend above and below the UPC symbol, tall enough so that at least part of the top or bottom of the tall ID number symbol "catches" these skewed scan lines, to avoid the ID number symbol being missed altogether (only the part of the ID number symbol closest to the UPC symbol actually need be so tall).
- the two symbols of Fig. 3 could be made the same height and placed in vertical alignment next to each other (i.e., both sitting on the same horizontal line and both rising to the same height therefrom) and bearer bars used across their tops and bottoms spanning the 1/4 inch to the 3/8 inch space in-between. As may be understood, the space between the two symbols cannot be too wide, i.e., greater than 3/8 inch in the above example.
- the 1/2 inch distance that the scan lines go past the first bar code symbol encountered may need to be increased, perhaps to 3/4 or 1 inch, depending on other specifications, angles, etc. And, if the in-between space were 1/4 inch, not 3/8, the 1/2 inch distance may suffice.
- another method may be used to automatically determine whether only one bar code symbol was present in a relevant area being scanned, or whether two bar code symbols located near each other were present.
- bar code scanning apparatus could always sense for the presence of a UPC symbol, and when a UPC symbol is read.
- the computer stores the information for each UPC code that may be read, as to whether or not another bar code symbol should be present and should also be read. Also, more than one flag could be used, in order to inform, e.g., which other particular bar code symbol(s) should be present and should be read, or, if more than one, which one(s) should be read, etc.
- UPC Number System Characters e.g., 1, 6, 7, 8 or 9, which were "Reserved for uses unidentified at this time," i.e., reserved when UPC conventions were adopted, to inform whether one UPC symbol or one UPC symbol and at least another bar code symbol should also be read in a given reading operation.
Landscapes
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Engineering & Computer Science (AREA)
- Computer Security & Cryptography (AREA)
- Health & Medical Sciences (AREA)
- General Health & Medical Sciences (AREA)
- Toxicology (AREA)
- Credit Cards Or The Like (AREA)
Claims (11)
- Un procédé pour identifier des objets non autorisés, comprenant les étapes suivantes :sur au moins un emplacement moins accessible de chaque objet autorisé, on associe à celui-ci une information d'identification qui comprend au moins deux parties distinctes sélectionnées de manière aléatoire;sur au moins un autre emplacement plus accessible de chaque objet autorisé, on associe à celui-ci l'information d'identification, mais en omettant au moins l'une des parties distinctes;on stocke l'information d'identification avec les aux moins deux parties distinctes, séparément desdites associations avec les objets autorisés;on lit l'information d'identification à partir de l'un au moins des emplacements associés à un objet dont on contrôle l'authenticité;on compare l'information lue avec l'information stockée correspondante, pour détecter une ou plusieurs discordances entre elles, grâce à quoi un objet non autorisé est identifié.
- Un procédé pour identifier des objets non autorisés, comprenant les étapes suivantes :sur au moins un emplacement moins accessible de chaque objet autorisé, on associe à celui-ci une information d'identification qui comprend au moins deux parties distinctes sélectionnées de façon aléatoire;dans au moins un autre emplacement plus accessible de chaque objet autorisé, on associe à celui-ci l'information d'identification, mais en omettant l'une au moins des parties distinctes;on stocke ladite information avec les aux moins deux parties distinctes, séparément desdites associations avec les objets autorisés;on lit l'information d'identification à partir de l'autre emplacement plus accessible associé à un objet dont on contrôle l'authenticité;on compare l'information lue provenant de l'autre emplacement plus accessible avec l'information stockée correspondante, pour détecter des discordances entre elles, grâce à quoi un objet non autorisé est identifié;on lit l'information d'identification incluant les aux moins deux parties distinctes, à partir de l'au moins un emplacement moins accessible associé à un objet dont on contrôle l'authenticité;on compare l'information lue provenant de l'au moins un emplacement moins accessible avec des parties correspondantes de l'information stockée, pour détecter une ou plusieurs discordances entre elles, grâce à quoi un objet non autorisé est identifié.
- Un procédé pour identifier des objets non autorisés avec une enveloppe extérieure, tels que des produits avec emballage, comprenant les étapes suivantes :sur au moins un emplacement à l'intérieur de l'enveloppe de chaque objet autorisé, on associe à celui-ci une information d'identification qui comprend au moins deux parties distinctes sélectionnées de façon aléatoire;sur au moins un emplacement sur l'extérieur de l'enveloppe de chaque objet autorisé, on associe à celui-ci l'information d'identification, mais en omettant l'une au moins des parties distinctes;on stocke ladite information avec les aux moins deux parties distinctes, séparément desdites associations avec les objets autorisés;on lit l'information d'identification à partir de l'un au moins des emplacements associés à un objet dont on contrôle l'authenticité;on compare l'information lue avec l'information stockée correspondante pour détecter une ou plusieurs discordances entre elles, grâce à quoi un objet non autorisé est identifié.
- Un procédé pour identifier des objets non autorisés avec une enveloppe extérieure, tels que des produits avec emballage, comprenant les étapes suivantes :sur au moins un emplacement à l'intérieur de l'enveloppe de chaque objet autorisé, on associe à celui-ci une information d'identification qui comprend au moins deux parties distinctes sélectionnées de façon aléatoire;sur au moins un emplacement sur l'extérieur de l'enveloppe de chaque objet autorisé, on associe à celui-ci l'information d'identification, mais en omettant l'une au moins des parties distinctes;on stocke ladite information avec les aux moins deux parties distinctes, séparément desdites associations avec les objets autorisés;on lit l'information d'identification à partir d'au moins un emplacement sur l'extérieur d'un objet dont on contrôle l'authenticité;on compare l'information lue à partir de l'emplacement extérieur avec l'information stockée correspondante, pour détecter une discordance entre elles, grâce à quoi un objet non autorisé est identifié;on lit l'information d'identification comprenant les aux moins deux parties distinctes, à partir d'au moins un emplacement intérieur d'un objet dont on contrôle l'authenticité;on compare l'information lue à partir de l'emplacement intérieur avec l'information stockée correspondante, pour détecter une ou plusieurs discordances entre elles, grâce à quoi un objet non autorisé est identifié.
- Un procédé de désignation d'un objet comme étant autorisé, comprenant les étapes suivantes :on sélectionne de façon aléatoire au moins deux chiffres distincts;on stocke ces deux chiffres distincts avec le numéro de série de l'objet autorisé; eton associe à l'objet, sur la surface extérieure de celui-ci, le numéro de série et un chiffre distinct parmi les deux chiffres distincts; et,on associe à l'objet, à l'intérieur de sa surface extérieure, le numéro de série et les deux chiffres distincts.
- Un procédé de désignation d'un objet comme étant autorisé, comprenant les étapes suivantes :on sélectionne de façon aléatoire au moins deux chiffres distincts;on stocke ces au moins deux chiffres distincts conjointement à un numéro de série d'un objet autorisé, sous la forme d'un numéro d'identification autorisé complet; eton associe à l'objet, sur la surface extérieure de celui-ci, le numéro de série et un chiffre distinct parmi les au moins deux chiffres distincts.
- Le procédé selon la revendication 6, dans lequel le numéro de série et les deux chiffres distincts sont placés à l'intérieur de la surface extérieure de l'objet.
- Le procédé selon la revendication 7, dans lequel le numéro de série et les deux chiffres distincts placés à l'intérieur de la surface extérieure de l'objet sont associés à une carte de retour pour l'objet.
- Un système pour identifier un objet non autorisé parmi un ensemble d'objets autorisés, chaque objet autorisé de l'ensemble étant associé à une information d'identification dont une partie a été calculée en utilisant un algorithme qui dépend d'un nombre sélectionné de façon aléatoire, le système comprenant :des moyens pour stocker de façon sûre les nombres sélectionnés de façon aléatoire uniquement à un seul emplacement;des moyens pour lire une information d'identification à partir d'un objet;des moyens couplés pour recevoir l'information lue à partir de l'objet, pour stocker au moins temporairement cette information; etdes moyens pour détecter automatiquement le moment auquel l'information lue sur un objet quelconque comprend une partie précitée différente de celle calculée en utilisant l'algorithme, grâce à quoi un objet non autorisé est identifié.
- Le système selon la revendication 9, comprenant également des moyens pour effacer automatiquement la partie calculée en utilisant l'algorithme, après l'association avec l'objet autorisé.
- Un procédé pour identifier des objets non autorisés, comprenant les étapes suivantes :on associe à chaque objet autorisé une information d'identification qui comprend une multiplicité de parties sélectionnées de façon aléatoire, l'une au moins des parties sélectionnées de façon aléatoire étant cachée dans une condition donnée des objets, et l'une au moins des parties sélectionnées de façon aléatoire étant visible dans cette condition donnée de l'objet;on stocke cette information séparément de ladite association avec les objets autorisés;on lit cette information sur un objet dont on contrôle l'authenticité; eton compare l'information lue avec l'information stockée pour détecter une discordance entre elles, grâce à quoi un objet non autorisé est identifié.
Applications Claiming Priority (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| PCT/US1992/003911 WO1993022745A1 (fr) | 1992-05-06 | 1992-05-06 | Detection de contrefaçons a l'aide de codes d'identification contenant des zones de chiffres aleatoires |
Publications (3)
| Publication Number | Publication Date |
|---|---|
| EP0647342A1 EP0647342A1 (fr) | 1995-04-12 |
| EP0647342A4 EP0647342A4 (fr) | 1995-09-06 |
| EP0647342B1 true EP0647342B1 (fr) | 2002-03-27 |
Family
ID=22231062
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| EP92911723A Expired - Lifetime EP0647342B1 (fr) | 1992-05-06 | 1992-05-06 | Detection de contrefacons a l'aide de codes d'identification contenant des zones de chiffres aleatoires |
Country Status (4)
| Country | Link |
|---|---|
| EP (1) | EP0647342B1 (fr) |
| AU (1) | AU1895992A (fr) |
| DE (1) | DE69232519D1 (fr) |
| WO (1) | WO1993022745A1 (fr) |
Cited By (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| WO2013165028A2 (fr) | 2012-05-04 | 2013-11-07 | Atambo Patrick Nyachio | Systèmes et procédés de localisation et d'authentification d'articles portant des numéros consécutifs |
Families Citing this family (36)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US6442276B1 (en) * | 1997-07-21 | 2002-08-27 | Assure Systems, Inc. | Verification of authenticity of goods by use of random numbers |
| EP0946019A1 (fr) * | 1998-03-25 | 1999-09-29 | CANAL+ Société Anonyme | Authentification des données dans un système de transmission numérique |
| EP0957459A1 (fr) * | 1998-05-12 | 1999-11-17 | Orell Füssli Graphische Betriebe AG | Méthode et dispositif pour vérifier le droit de propriété d'objets |
| NL1010552C2 (nl) * | 1998-11-13 | 2000-05-16 | Koninkl Kpn Nv | Werkwijze voor het verschaffen van een betalingsbewijs voor een te leveren dienst, alsmede stelsel voor het controleren van betalingsbewijzen. |
| NL1010722C2 (nl) * | 1998-12-04 | 2000-06-06 | Ruiten Theodorus H M | Werkwijze en beveiligingssysteem voor het vaststellen van de identiteit van waarde-voorwerpen. |
| US6681214B1 (en) | 1999-06-29 | 2004-01-20 | Assure Systems, Inc. | Secure system for printing authenticating digital signatures |
| EP1218857A1 (fr) * | 1999-08-25 | 2002-07-03 | Giesecke & Devrient GmbH | Procede de garantie produit |
| US6843418B2 (en) * | 2002-07-23 | 2005-01-18 | Cummin-Allison Corp. | System and method for processing currency bills and documents bearing barcodes in a document processing device |
| US6965880B2 (en) * | 2000-03-30 | 2005-11-15 | Fujitsu Limited | Transaction number management method in network commodity sales |
| RU2165643C1 (ru) * | 2000-04-19 | 2001-04-20 | Государственное унитарное предприятие Научно-технический центр "Атлас" | Способ подтверждения подлинности информации |
| GB0015147D0 (en) | 2000-06-21 | 2000-08-09 | Jacobs Michael | Tracking system |
| US20040162828A1 (en) * | 2000-08-04 | 2004-08-19 | Moyes Jeremy Paul | System and methods for monitoring items |
| DE60006969T2 (de) * | 2000-11-02 | 2004-10-28 | Orell Füssli Security Documents AG | Verfahren zum Prüfen der Echtheit von Artikeln |
| NO314372B1 (no) * | 2001-06-20 | 2003-03-10 | Kezzler As | Fremgangsmåte for frembringelse og senere benyttelse av autentiseringsinformasjon |
| CN1606763A (zh) * | 2001-10-25 | 2005-04-13 | 皇家飞利浦电子股份有限公司 | 用于证实已包装商品的方法和系统 |
| FR2831695B1 (fr) * | 2001-10-31 | 2004-10-01 | Catherine Bouthiaux | Procede de tracabilite et d'authentification de produits a haute valeur ajoutee et/ou sensibles |
| EP1454291B1 (fr) * | 2001-12-11 | 2007-08-08 | Tagsys SA | Systemes d'etiquetage de donnees securises |
| RU2216776C2 (ru) * | 2001-12-24 | 2003-11-20 | Общество с ограниченной ответственностью "АЙ-ФЕРСТ" | Способ идентификации и учета маркированных объектов и система для его осуществления |
| RU2207624C1 (ru) * | 2001-12-27 | 2003-06-27 | Субботин Андрей Александрович | Способ определения подлинности объекта по информации об этом объекте |
| US8171567B1 (en) | 2002-09-04 | 2012-05-01 | Tracer Detection Technology Corp. | Authentication method and system |
| RU2225032C1 (ru) * | 2002-10-18 | 2004-02-27 | Власюк Владимир Владимирович | Способ контроля подлинности продукции |
| WO2005083644A1 (fr) * | 2004-03-02 | 2005-09-09 | Stikker.Com Bv | Procede et systeme permettant de verifier l'authenticite de produits |
| DE602005014755D1 (de) | 2004-03-12 | 2009-07-16 | Ingenia Technology Ltd | Verfahren und vorrichtungen zur erzeugung authentifizierbarer gegenstände und ihrer nachfolgenden überprüfung |
| ITTO20050160A1 (it) * | 2005-03-14 | 2006-09-15 | Gaetano Rizzi | Sistema di gestione e controllo dati, particolamente per la verifica di articoli dotati di un codice identificativo |
| KR100831601B1 (ko) * | 2005-10-26 | 2008-05-23 | 이항경 | 일련 번호 및 비밀 번호를 이용한 통신 네트워크상에서의상품 진위 여부 확인 방법 및 시스템 |
| EP2008221A4 (fr) * | 2006-03-29 | 2010-07-07 | Trackway Oy | Etude polyvalente d'authenticite |
| FR2900481B1 (fr) * | 2006-04-27 | 2009-04-24 | Arjowiggins Soc Par Actions Si | Systeme de lecture d'au moins un code a barres |
| DE102006020958A1 (de) * | 2006-05-05 | 2007-11-08 | Nahro Oktay | Verfahren zur Authentifizierung eines Produkts |
| EP1947592A1 (fr) * | 2007-01-19 | 2008-07-23 | Multitel ASBL | Procédé et dispositif d'authentification pour protéger les marchandises fabriquées |
| GB2460625B (en) * | 2008-05-14 | 2010-05-26 | Ingenia Holdings | Two tier authentication |
| GB2462029B (en) * | 2008-05-14 | 2010-08-25 | Ingenia Holdings | Tracking of an Article |
| RU2413973C2 (ru) * | 2009-05-26 | 2011-03-10 | Владимир Анатольевич Перелыгин | Идентификационный сертификат |
| GB2476226B (en) | 2009-11-10 | 2012-03-28 | Ingenia Holdings Ltd | Optimisation |
| EP2383705B1 (fr) | 2010-04-30 | 2012-10-31 | MediSeal GmbH | Emballage sous blister protégé contre la falsification |
| WO2012082006A1 (fr) * | 2010-12-15 | 2012-06-21 | Perelygin Vladimir Anatolevich | Certificat d'identification |
| DE202014008915U1 (de) * | 2014-11-11 | 2014-12-08 | Siemens Vai Metals Technologies Gmbh | Halterung zur Aufnahme mindestens einer Identfikationsmarke und metallurgisches Gefäß mit einer solchen Halterung sowie Identifikationsmarke |
Citations (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US3833795A (en) * | 1971-08-05 | 1974-09-03 | Elscint Ltd | Method and means for ascertaining the authenticity of serially numbered objects |
Family Cites Families (16)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US3890599A (en) * | 1973-09-13 | 1975-06-17 | Command Automation Inc | Arrangement for protecting and authenticating a document |
| US4193061A (en) * | 1978-07-11 | 1980-03-11 | Zoltai John T | Electronic authentication system |
| FR2439436A1 (fr) * | 1978-10-18 | 1980-05-16 | Chateau Michel | Procede de dialogue entre un ordinateur et un de ses utilisateurs et application de ce procede aux paiements bancaires ou analogues |
| US4558318A (en) * | 1980-06-23 | 1985-12-10 | Light Signatures, Inc. | Merchandise verification and information system |
| US4463250A (en) * | 1981-07-11 | 1984-07-31 | Mcneight David L | Method and apparatus for use against counterfeiting |
| FR2556867B1 (fr) * | 1983-12-14 | 1986-06-06 | Jalon Michel | Procede de marquage de securite, matieres pourvues de marques de securite, et leurs applications. |
| US4630201A (en) * | 1984-02-14 | 1986-12-16 | International Security Note & Computer Corporation | On-line and off-line transaction security system using a code generated from a transaction parameter and a random number |
| JPS6191790A (ja) * | 1984-10-12 | 1986-05-09 | カシオ計算機株式会社 | カ−ド照合装置 |
| FR2575566B1 (fr) * | 1984-12-28 | 1990-06-22 | Bull Sa | Procede pour personnaliser des supports portatifs tels que des cartes |
| FR2596901B3 (fr) * | 1986-04-03 | 1988-08-26 | Bucari Claude | Chequier inviolable et procede de controle des cheques |
| US4839507A (en) * | 1987-11-06 | 1989-06-13 | Lance May | Method and arrangement for validating coupons |
| US4949256A (en) * | 1988-05-06 | 1990-08-14 | Humble David Raymond | Coupon validation network with storage of customer coupon data for credit on future purchases |
| EP0354260A1 (fr) * | 1988-08-10 | 1990-02-14 | C.P.C. Investment Trust | Système de codage et de décodage |
| DE68920300T2 (de) * | 1988-12-05 | 1995-05-18 | James Salvatore Bianco | Identifikationsmittel mit verschlüsseltem Sicherheitskode. |
| FR2654236B1 (fr) * | 1989-11-03 | 1992-01-17 | Europ Rech Electr Lab | Procede de protection contre l'utilisation frauduleuse de cartes a microprocesseur, et dispositif de mise en óoeuvre. |
| NL9002071A (nl) * | 1990-09-21 | 1991-02-01 | Nl Bank Nv | Een bankbiljet met streepcode. |
-
1992
- 1992-05-06 AU AU18959/92A patent/AU1895992A/en not_active Abandoned
- 1992-05-06 DE DE69232519T patent/DE69232519D1/de not_active Expired - Lifetime
- 1992-05-06 WO PCT/US1992/003911 patent/WO1993022745A1/fr not_active Ceased
- 1992-05-06 EP EP92911723A patent/EP0647342B1/fr not_active Expired - Lifetime
Patent Citations (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| US3833795A (en) * | 1971-08-05 | 1974-09-03 | Elscint Ltd | Method and means for ascertaining the authenticity of serially numbered objects |
Cited By (1)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| WO2013165028A2 (fr) | 2012-05-04 | 2013-11-07 | Atambo Patrick Nyachio | Systèmes et procédés de localisation et d'authentification d'articles portant des numéros consécutifs |
Also Published As
| Publication number | Publication date |
|---|---|
| EP0647342A1 (fr) | 1995-04-12 |
| EP0647342A4 (fr) | 1995-09-06 |
| DE69232519D1 (de) | 2002-05-02 |
| AU1895992A (en) | 1993-11-29 |
| WO1993022745A1 (fr) | 1993-11-11 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| EP0647342B1 (fr) | Detection de contrefacons a l'aide de codes d'identification contenant des zones de chiffres aleatoires | |
| US5367148A (en) | Counterfeit detection using ID numbers with at least one random portion | |
| US8566598B2 (en) | Method for article authentication using an article's authentication code and a second code provided by the party requesting authentication | |
| US4013894A (en) | Secure property document and system | |
| US5841555A (en) | Secure optical identification method and means | |
| US5432329A (en) | Automated holographic optical recognition and decoding system for verification | |
| US6073121A (en) | Check fraud prevention system | |
| JP5612332B2 (ja) | 生体情報を保存した不正防止セキュリティカード及びその使用方法 | |
| US5336871A (en) | Holographic enhancement of card security | |
| US8052040B2 (en) | Negotiable instrument with fraud protection | |
| WO1992016913A1 (fr) | Securisation d'operations financieres | |
| US6560017B1 (en) | Compound secure optical identification method and means | |
| US10414197B2 (en) | Check fraud prevention method | |
| US5661284A (en) | Commercial transaction system | |
| US20090009285A1 (en) | Authentication of Re-Presentable Items | |
| JPH0776981B2 (ja) | カード型記録媒体の記録再生装置及びその不正使用防止方法 | |
| US6463541B2 (en) | Object authentification method using printed binary code and computer registry | |
| JP2003170686A (ja) | 媒体の分配方法 | |
| US7617986B2 (en) | Laminate security feature | |
| GB2398270A (en) | Document with user authentication. | |
| JPH0354664A (ja) | 美術品等高価格商品の保証システム | |
| JPS6019279A (ja) | カ−ドの真偽判別装置 | |
| JP4011943B2 (ja) | 有価証券処理システムと有価証券読み取り装置 | |
| US20040002977A1 (en) | Method and system for veryfing a deed | |
| JP2005010948A (ja) | 真偽判定システム |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PUAI | Public reference made under article 153(3) epc to a published international application that has entered the european phase |
Free format text: ORIGINAL CODE: 0009012 |
|
| 17P | Request for examination filed |
Effective date: 19941206 |
|
| AK | Designated contracting states |
Kind code of ref document: A1 Designated state(s): DE FR GB IT NL |
|
| A4 | Supplementary search report drawn up and despatched | ||
| AK | Designated contracting states |
Kind code of ref document: A4 Designated state(s): DE FR GB IT NL |
|
| 17Q | First examination report despatched |
Effective date: 19960624 |
|
| GRAG | Despatch of communication of intention to grant |
Free format text: ORIGINAL CODE: EPIDOS AGRA |
|
| GRAG | Despatch of communication of intention to grant |
Free format text: ORIGINAL CODE: EPIDOS AGRA |
|
| GRAH | Despatch of communication of intention to grant a patent |
Free format text: ORIGINAL CODE: EPIDOS IGRA |
|
| GRAH | Despatch of communication of intention to grant a patent |
Free format text: ORIGINAL CODE: EPIDOS IGRA |
|
| REG | Reference to a national code |
Ref country code: GB Ref legal event code: IF02 |
|
| GRAA | (expected) grant |
Free format text: ORIGINAL CODE: 0009210 |
|
| RIC1 | Information provided on ipc code assigned before grant |
Free format text: 7G 07D 7/00 A, 7G 07F 7/08 B |
|
| AK | Designated contracting states |
Kind code of ref document: B1 Designated state(s): DE FR GB IT NL |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: NL Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20020327 Ref country code: IT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRE;WARNING: LAPSES OF ITALIAN PATENTS WITH EFFECTIVE DATE BEFORE 2007 MAY HAVE OCCURRED AT ANY TIME BEFORE 2007. THE CORRECT EFFECTIVE DATE MAY BE DIFFERENT FROM THE ONE RECORDED.SCRIBED TIME-LIMIT Effective date: 20020327 Ref country code: FR Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20020327 |
|
| REF | Corresponds to: |
Ref document number: 69232519 Country of ref document: DE Date of ref document: 20020502 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: DE Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20020628 |
|
| NLV1 | Nl: lapsed or annulled due to failure to fulfill the requirements of art. 29p and 29m of the patents act | ||
| EN | Fr: translation not filed | ||
| PLBE | No opposition filed within time limit |
Free format text: ORIGINAL CODE: 0009261 |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: NO OPPOSITION FILED WITHIN TIME LIMIT |
|
| 26N | No opposition filed |
Effective date: 20021230 |
|
| PGFP | Annual fee paid to national office [announced via postgrant information from national office to epo] |
Ref country code: GB Payment date: 20060503 Year of fee payment: 15 |
|
| GBPC | Gb: european patent ceased through non-payment of renewal fee |
Effective date: 20070506 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: GB Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20070506 |