EP1815256B1 - Elektronischer tachograph für ein kraftfahrzeug - Google Patents
Elektronischer tachograph für ein kraftfahrzeug Download PDFInfo
- Publication number
- EP1815256B1 EP1815256B1 EP05818272A EP05818272A EP1815256B1 EP 1815256 B1 EP1815256 B1 EP 1815256B1 EP 05818272 A EP05818272 A EP 05818272A EP 05818272 A EP05818272 A EP 05818272A EP 1815256 B1 EP1815256 B1 EP 1815256B1
- Authority
- EP
- European Patent Office
- Prior art keywords
- unit
- data
- card
- called
- tachographic
- Prior art date
- Legal status (The legal status is an assumption and is not a legal conclusion. Google has not performed a legal analysis and makes no representation as to the accuracy of the status listed.)
- Revoked
Links
- 230000033001 locomotion Effects 0.000 claims description 45
- 230000015654 memory Effects 0.000 claims description 32
- 238000012545 processing Methods 0.000 claims description 25
- 238000003780 insertion Methods 0.000 claims description 17
- 230000037431 insertion Effects 0.000 claims description 17
- 230000000694 effects Effects 0.000 claims description 12
- 238000004422 calculation algorithm Methods 0.000 claims description 11
- 238000004891 communication Methods 0.000 claims description 11
- 230000006870 function Effects 0.000 claims description 10
- 238000000034 method Methods 0.000 claims description 9
- 230000008569 process Effects 0.000 claims description 7
- 230000000737 periodic effect Effects 0.000 claims description 2
- 239000004020 conductor Substances 0.000 claims 1
- 231100000279 safety data Toxicity 0.000 claims 1
- 238000001514 detection method Methods 0.000 description 8
- 230000007717 exclusion Effects 0.000 description 5
- 230000004224 protection Effects 0.000 description 5
- 238000004364 calculation method Methods 0.000 description 4
- 230000007246 mechanism Effects 0.000 description 4
- 238000012544 monitoring process Methods 0.000 description 4
- 230000005540 biological transmission Effects 0.000 description 3
- 238000013461 design Methods 0.000 description 2
- 230000008520 organization Effects 0.000 description 2
- 230000001960 triggered effect Effects 0.000 description 2
- 238000012795 verification Methods 0.000 description 2
- 241001080024 Telles Species 0.000 description 1
- 241000897276 Termes Species 0.000 description 1
- 240000008042 Zea mays Species 0.000 description 1
- 238000012550 audit Methods 0.000 description 1
- 238000013479 data entry Methods 0.000 description 1
- 238000011161 development Methods 0.000 description 1
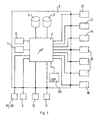
- 238000010586 diagram Methods 0.000 description 1
- 238000007599 discharging Methods 0.000 description 1
- 230000009977 dual effect Effects 0.000 description 1
- 238000011156 evaluation Methods 0.000 description 1
- 230000008571 general function Effects 0.000 description 1
- 238000005286 illumination Methods 0.000 description 1
- 238000007726 management method Methods 0.000 description 1
- 238000004519 manufacturing process Methods 0.000 description 1
- 238000005259 measurement Methods 0.000 description 1
- 230000011664 signaling Effects 0.000 description 1
- 229910052710 silicon Inorganic materials 0.000 description 1
- 239000010703 silicon Substances 0.000 description 1
- 238000012360 testing method Methods 0.000 description 1
Images
Classifications
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07C—TIME OR ATTENDANCE REGISTERS; REGISTERING OR INDICATING THE WORKING OF MACHINES; GENERATING RANDOM NUMBERS; VOTING OR LOTTERY APPARATUS; ARRANGEMENTS, SYSTEMS OR APPARATUS FOR CHECKING NOT PROVIDED FOR ELSEWHERE
- G07C5/00—Registering or indicating the working of vehicles
- G07C5/08—Registering or indicating performance data other than driving, working, idle, or waiting time, with or without registering driving, working, idle or waiting time
- G07C5/0841—Registering performance data
- G07C5/085—Registering performance data using electronic data carriers
- G07C5/0858—Registering performance data using electronic data carriers wherein the data carrier is removable
-
- G—PHYSICS
- G07—CHECKING-DEVICES
- G07C—TIME OR ATTENDANCE REGISTERS; REGISTERING OR INDICATING THE WORKING OF MACHINES; GENERATING RANDOM NUMBERS; VOTING OR LOTTERY APPARATUS; ARRANGEMENTS, SYSTEMS OR APPARATUS FOR CHECKING NOT PROVIDED FOR ELSEWHERE
- G07C7/00—Details or accessories common to the registering or indicating apparatus of groups G07C3/00 and G07C5/00
Definitions
- the invention relates to a unit of a so-called tachograph control device intended to be loaded onto a motor vehicle-in particular a vehicle for transporting goods or passengers-in order to enable the control of the activities of a driver of the vehicle.
- driver designates a person who can in turn exercise the activities of driver or co-driver (also called “conveyor") of the vehicle.
- the tachograph comprises, in addition to this unit, at least one vehicle motion sensor, connected to the unit when the latter is on board.
- a tachograph has the particular function of recording, storing, producing, printing, and possibly exchanging and displaying, data, called driver data, relating to the activities of a driver of the vehicle, with a view to allow control of these activities by a controller.
- the tachographs currently used in Europe are of the tachograph type with graphic discs, such as that described by US 4,782,691 . These are analog and mechanical instruments for retranscribing conductive data on a paper disk by means of a stylus.
- a tachograph unit already has, for this purpose, mechanical protections (reinforced housing possibly equipped with security seals ).
- the implementation of electronic components - including microprocessor circuit (s) and smart card reader (s) - in the tachograph unit now makes it possible to envisage the implementation of electronic protections within the unit, such as cryptographic security mechanisms.
- the tachograph unit must keep cryptographic secrets (private or secret encryption keys, for encryption and decryption) and integrate corresponding encryption algorithms.
- the object of the invention is to provide a secure tachograph unit, not only endowed with such cryptographic algorithms and secrets, but also and above all with enhanced electronic protection capable of offering a high level of resistance to fraudulent attacks.
- the aim is not only to offer control and limitation of access to data managed by the unit, read and / or write, but also and above all to ensure compliance with this limitation by detecting any falsification of these data.
- An object of the invention is to provide a unit able to strongly resist an attack conducted using sophisticated means, whether means implemented directly on the circuits of the unit or remotely.
- the object of the invention is in particular to provide a unit offering a level of security rated E3 FORT according to the ITSEC evaluation methodology.
- Another object of the invention is to provide a more efficient electronic tachograph unit also in terms of functionality.
- the invention aims to achieve the aforementioned objectives at lower cost, by proposing a tachograph unit low cost.
- the invention aims to provide a tachograph unit that fulfills these objectives from means, including electronic components, customary and inexpensive, or possibly new but inexpensive development and manufacturing.
- the invention relates to a tachograph unit intended to be on board a motor vehicle and to be connected to at least one vehicle motion sensor, which unit comprises at least one microprocessor card (s), said main board, for processing and storing data, called tachograph data, comprising at least data, called conductive data, relating to activities of a driver of said vehicle.
- the tachograph unit is also adapted to perform operations, said security operations, implementing encryption algorithms for the purpose of authentication of at least a portion of the tachograph data.
- security data refers to additional data stored and / or created and / or calculated and / or used ... in the context of security operations.
- the security data includes encryption keys, certificates issued by authorized official bodies, security attributes generated by a security operation for a data transmission, such as a signature, a checksum -dite checksum -...
- Some of these data, called secret data are by definition secret: stored in the tachograph unit, they must remain inaccessible to any unauthorized person (the tachograph unit must offer a high level of resistance to attacks to obtain this secret data); it is essentially secret -symmetric encryption keys and private encryption keys.
- CSP circuit (s) can be carried by the main card or by one or more other card (s).
- the invention consists in selecting and separating from all the operations implemented by a tachograph unit, at least part of the operations relating solely to security (operations consisting in authenticating and / or protecting certain data by means of encryption algorithms, with the ultimate aim of guaranteeing the authenticity and integrity of the driver data), and to execute the selected security operations by a specific, physically protected circuit.
- this protected circuit are stored secret security data. It can also store encryption algorithms and / or non-secret security data (such as public keys) relating to the security operations allocated to said CSP circuit.
- the (s) circuit (s) CSP is (are) dedicated (s) essentially to the realization of security operations, the term "essentially” meaning that each circuit CSP is dedicated to operations of security and possibly to specific operations requiring a low capacity of processing and storage, such as the storage of temporary data generated by the processing of tachograph data.
- a cryptographic service provider circuit that is customary and inexpensive, having a low processing and storage capacity, can thus be used as a CSP circuit according to the invention, given that it is "discharged" from the functionalities of tachograph unit that require more capacity.
- the (s) circuit (s) CSP is (are) dedicated (s) essentially to the realization of all security operations. Therefore, the main microprocessor (s) does not perform any security operation. It is therefore possible to use, as main microprocessor, a basic microprocessor, unprotected and therefore inexpensive, such as, for example, a computer usually used in the automotive field. Such a conventional computer has sufficient processing and storage capacity to handle all the tasks (excluding security operations) assigned to the tachograph unit.
- the tachograph unit comprises a single CSP circuit, essentially dedicated to all security operations.
- the main card of the tachograph unit comprises at least one memory, called application memory, associated with a main microprocessor, in which is stored an application (one or more programs), called tachograph application , which can be loaded into this main microprocessor for processing tachograph data.
- this microprocessor main is adapted to verify the authenticity and integrity of at least a portion of the tachograph application using at least one security operation performed by a CSP circuit of the tachograph unit.
- said main microprocessor integrates a protected start program, physically registered in the microprocessor and adapted for, during an operation to implement at least one of a tachograph application (first or new) in the unit, order audit CSP circuit executing at least one security operation for the purpose of authenticating said application or tachograph application part, and not controlling the registration of this application or tachograph application part in the application memory only if it is considered by the CSP circuit to be genuine and honest.
- the startup program is hard-coded (in silicon) in the main microprocessor, it can not be modified. This guarantees the control by the main microprocessor and the execution by the CSP circuit of the aforementioned security operation (s).
- the tachograph application finally stored in the application memory and used by the main microprocessor (s) is therefore necessarily authentic and integrated, that is to say, conceived and implemented by an authorized organization, in a secure environment, according to the specifications imposed by the rules and standards.
- the tachograph application stored in the application memory is itself adapted to, when loaded into the main microprocessor for tachograph data processing, periodically control the associated CSP circuit 1. performing at least one security operation for its own authentication.
- each CSP circuit is connected to a main microprocessor, said associated CSP and main microprocessor circuit being adapted to operate in a master / slave relationship in which the main microprocessor is the master and the CSP circuit is the slave .
- the tachograph unit comprises a reader / writer device for smart cards, called tachograph cards, able to receive at least two tachograph cards in parallel.
- the tachograph unit also comprises a connection interface, called a tachograph card interface, for wireless communication (and in particular at a distance) of the unit with a card reader / writer device.
- a connection interface called a tachograph card interface
- tachograph external to the unit (in its simplest version, this external device is adapted to receive only one tachograph card at a time).
- each tachograph card belonging to one of these types: driver cards, controller cards, business cards and shop cards.
- Each type of tachograph card opens right on the one hand to a restricted access to certain predetermined data stored in the unit, and on the other hand to the execution of certain predetermined operations according to the type of tachograph card.
- the insertion of a tachograph card into the card reader / writer device (whether it is the device of the integrated device unit or an external device capable of communicating with the unit) makes it possible to open an operating session of the unit corresponding to the type of card inserted.
- any tachograph card inserted in the card reader / writer device must be able to be authenticated, as well as the data exchanged between the tachograph card and the tachograph unit.
- the reader / recorder device is controlled by at least one main microprocessor of the unit, which is associated with a CSP circuit.
- This main microprocessor (or possibly these main microprocessors) is adapted to control said circuit CSP performing security operations for the mutual authentication of the unit and a tachograph card present in the reader / writer device (integrated or external), and not allowing the opening of a corresponding operating session only if the unit and the tachograph card are considered authentic.
- An authenticated driver card thus gives access to a session of operation called driver session; an authenticated workshop card gives access to an operating session called a workshop session; an authenticated controller card provides access to a session of operation known as a controller session; an authenticated corporate card gives access to a session of operation called business session.
- This mutual authentication between tachograph card and unit is preferably performed as soon as a card is inserted into the card reader / writer device (especially with regard to the integrated device).
- the main microprocessor is adapted to monitor card insertions and withdrawals in the reader / writer device and to trigger the aforementioned security operations as soon as an insertion of a tachograph card into the reader / writer device is detected.
- Opening an operating session allows operations to be performed, the nature of which depends on the type of the session. Some of these operations may lead to data exchanges between tachograph card and unit.
- the main microprocessor is adapted to control the circuit CSP execution of at least a security operation to authenticate said data, and to process the exchanged data only if they are considered to be authentic and honest.
- the tachograph unit must also be able to authenticate the motion sensor with which it communicates when it is on board a vehicle, as well as the data, called motion data, that it receives from said sensor. Note that the movement data are tachograph data.
- the tachograph unit For its connection to the motion sensor, the tachograph unit comprises a connection interface, called sensor interface.
- this connection is preferably wired, in which case the sensor interface consists of one or more connector (s). But it is not excluded that this connection is wireless and that the sensor interface comprises (possibly in combination with a connector) an emitter-receiver device of electromagnetic waves.
- the main board of the unit comprises at least one main microprocessor connected to said sensor interface and which is associated with a CSP circuit, said main microprocessor being adapted to control said execution of the CSP circuit.
- the pairing operation can be implemented only if an authentic and authenticated workshop tachograph card is present in the unit reader / recorder integrated in the unit.
- the main microprocessor (s) of the unit is (are) adapted to allow the execution of a pairing operation only in the context of a workshop session (which can only be opened by authentication of a workshop card).
- the tachograph unit also comprises a connection interface, called the unloading interface, for the communication of the unit with an external device called unloading device, in particular able to store tachograph data.
- the unloading interface may include a connector, for wired connection of the unloader with the unit, and / or an emitter / receiver for electromagnetic waves, for wireless communication between the unit and an optionally remote unloading device.
- a data unloading operation can be implemented, on the order of a user, only if a tachograph card of a controller, a workshop or an enterprise (excluding a driver) authentic and authenticated is present in the device reader / chart recorder (integrated or external).
- the main microprocessor (s) is (are) adapted to allow the execution of a data unloading operation to an unloading device "connected" to the unit (wired or wireless connection) via the unload interface, only in the context of a controller or workshop or enterprise session (opened by the authentication of a corresponding card).
- the downloaded tachograph data are accompanied by a security attribute, such as an electronic signature, for subsequent authentication by the unloading device or by another tool.
- the main microprocessor is also adapted for, in the context of a data unloading operation, commanding the circuit CSP the execution of at least one security operation for the protection of the data to be unloaded.
- the unit also advantageously comprises a connection interface, called a calibration interface, comprising at least one connector, for the communication of the unit with an external device called calibration device, for the purpose of calibrating unit.
- a calibration operation can not be implemented, on the control of a user, by means of a calibration device connected to the unit via the calibration interface, only if an authentic and authenticated workshop tachograph card is present in the card reader / writer device integrated into the unit.
- the main microprocessor (s) is (are) adapted to allow the execution of a calibration operation only in the context of a workshop session ( opened by the authentication of a workshop card).
- calibration data are transmitted to the unit by the calibration device.
- the data calibration stored in the unit at the end of the calibration operation are tachograph data.
- a main microprocessor of the unit is adapted to monitor card insertions and withdrawals in the card reader / writer device (integrated or external) and, as soon as a withdrawal of a tachograph card of the reader / writer device is detected, interrupt any operation in progress in the corresponding operating session.
- the operations are interrupted during sensor matching, updating the tachograph application, calibration, tachograph data unloading and of course read / write on the tachograph card (which does not is more connected ).
- the invention also relates to a tachograph unit characterized in combination by all or some of the features mentioned above and below.
- the invention extends to a motor vehicle equipped with such a tachograph unit.
- the tachograph comprises a vehicle motion sensor, connecting cables for connecting the motion sensor and the sensor connector 12 of the onboard unit.
- the motion sensor is formed in particular by a motion detection element, a microprocessor (to which the detection element is connected) and a connector for connecting the microprocessor of the sensor to the onboard unit.
- the security operations for the mutual authentication of the unit and a tachograph card preferably implement encryption calculations by means of asymmetric keys (private and public keys). .
- the main microprocessor 4 is indeed adapted to identify card insertions and withdrawals according to the signals it receives from the detection device (s) of said reader device / recorder: the presence of a card 60 in the read / write position - reception of a detection signal - after a period of absence of a card - no detection signal - translates the insertion of a card; the absence of a card following a period of card presence reflects the withdrawal of a card.
- mutual authentication of a tachograph card present in the reader / writer device is also triggered periodically (while no card withdrawal has been noted since the authentication precedence) by the main microprocessor 4 and / or by the tachograph card.
- the security operations for the authentication of data exchanged between the unit and the motion sensor or between the unit and a tachograph card preferably implement encryption calculations using session keys, that is, symmetric keys (secret keys).
- session keys that is, symmetric keys (secret keys).
- the session keys are stored in the (protected) memory of the CSP circuit 20.
- the reading of tachograph data on a previously authenticated tachograph card gives rise to the operations illustrated in FIG. figure 3 , which make it possible to guarantee the integrity of the data read (these operations are intended to verify that the data received by the main microprocessor 4 correspond to those sent by the tachograph card and that the latter were therefore not falsified during the transmission).
- the main microprocessor 4 prepares the read command (step 30): the control code is provided with data, called ancillary data, necessary for its execution, such as the address and the length of the tachograph data to be read (with a view to their location in the memory of the tachograph card).
- step 31 It transmits (step 31) the data annexed to the circuit CSP 20, with a command to execute a corresponding security operation, in order to protect the integrity of said data.
- the circuit CSP 20 calculates (step 32) a checksum, called checksum, of the ancillary data, encrypts said checksum by means of its session key and transmits (step 33) the encrypted checksum to the main microprocessor 4.
- the microprocessor main 4 prepares (step 34) and transmits (step 35) the entire read command (command code + ancillary data + checksum) to the tachograph card 60 (i.e., to its electronic chip 61) via the connector of the reader / writer device 8.
- the tachograph card 60, 61 checks the integrity of the data received (step 36) by decrypting the checksum received by means of its session key, calculating the checksum of the received ancillary data and comparing both values. If the latter coincide, the tachograph card 60, 61 transmits (step 38) the requested tachograph data, after having previously calculated and encrypted - by means of its session key - their checksum (step 37). Upon receipt of the data (step 39), the main microprocessor 4 transmits (step 40) to the CSP circuit 20 the tachograph data and the encrypted checksum received, as well as a command to execute a corresponding security operation to check the integrity of tachograph data received.
- the CSP circuit 20 calculates the checksum tachograph data and decrypts the encrypted checksum that accompanies them by means of its session key and compares the two values obtained (step 41). If they coincide, it sends a signal of agreement to the main microprocessor 4; otherwise, it transmits to the latter a signal of disagreement (step 42).
- the main microprocessor 4 only operates the tachograph data if the received signal is a tuning signal (step 43). If the tachograph data are not considered authentic (disagreement signal), the microprocessor stores the anomaly and possibly emits a signal corresponding to the attention of the user (step 43).
- Motion data received from the motion sensor is also subject to security operations for authentication.
- the motion sensor previously authenticated in the context of a pairing operation with the unit, continuously transmits pulses that it transmits to the unit, each pulse being transmitted at the instant when a predetermined distance has been traveled by the vehicle since the previous impulse.
- the motion sensor also has a counter, which it increments with each pulse emitted.
- the main microprocessor of the unit has a counter, which it increments with each pulse received. Periodically, the main microprocessor triggers a secure operation to compare the sensor and unit counters.
- the reading of the sensor counter is performed, for example, as previously explained with regard to the reading of tachograph data in a tachograph card: the value of the sensor counter transmitted to the unit is in particular authenticated by a security attribute of type encrypted checksum.
- a relative value of the sensor counter and a relative value of the unit counter are calculated by the main microprocessor and then compared. This procedure verifies the authenticity and integrity of the data (pulses) transmitted by the sensor during the period since the last comparison operation.
Landscapes
- Physics & Mathematics (AREA)
- General Physics & Mathematics (AREA)
- Time Recorders, Dirve Recorders, Access Control (AREA)
Claims (21)
- Tachograph (1) zur Mitnahme in einem Kraftfahrzeug, der an mindestens einen Bewegungssensor des Fahrzeugs angeschlossen wird und mindestens eine Mikroprozessor(en)karte (3), Hauptkarte genannt, enthält, zur Verarbeitung und Speicherung von Daten, Tachographendaten genannt, wobei besagte Tachographendaten mindestens Daten über die Aktivitäten eines Fahrers besagten Fahrzeugs, Fahrerdaten genannt, enthalten und besagter Tachograph geeignet ist, sogenannte Sicherheitsoperationen auszuführen, bei denen Chiffrieralgorithmen zum Einsatz kommen, um zumindest einen Teil der Tachographendaten zu authentifizieren, dadurch gekennzeichnet, dass- besagte Hauptkarte (3) mindestens einen Mikroprozessor (4), Hauptmikroprozessor genannt, zur Verarbeitung der Tachographendaten enthält,- der Tachograph mindestens einen physisch geschützten Schaltkreis (20), CSP-Schaltkreis genannt, enthält, der kryptographische Funktionen erfüllt und sich vom (von den) Hauptmikroprozessor(en) unterscheidet und in dem mindestens die sogenannten geheimen Sicherheitsdaten gespeichert sind, wobei dieser CSP-Schaltkreis (20) geeignet ist, zumindest einen Teil der Sicherheitsoperationen auszuführen, wenn sich der Tachograph in einem Fahrzeug befindet.
- Tachograph nach Anspruch 1, dadurch gekennzeichnet, dass die Hauptkarte (3) zumindest einen Speicher (5) besitzt, der Applikationsspeicher genannt wird, einem Hauptmikroprozessor (4) zugeordnet ist, und in dem eine Applikation, Tachographenapplikation genannt, gespeichert ist, die in diesen Hauptmikroprozessor zur Verarbeitung der Tachographendaten geladen werden kann, und dass dieser Hauptmikroprozessor geeignet ist, die Authentizität zumindest eines Teils der Tachographenapplikation mit Hilfe mindestens einer mit dem CSP-Schaltkreis (20) des Tachographen durchgeführten Sicherheitsoperation zu überprüfen.
- Tachograph nach Anspruch 2, dadurch gekennzeichnet, dass in diesen Hauptmikroprozessor (4) ein geschütztes Startprogramm integriert ist, das physisch in den Mikroprozessor eingeschrieben und geeignet ist, bei einer Operation, die darauf abzielt, zumindest einen Teil einer Tachographenapplikation in den Tachographen zu implementieren, besagtem CSP-Schaltkreis (20) den Befehl zur Ausführung mindestens einer Sicherheitsoperation zu geben, im Hinblick auf die Authentifizierung besagter Tachographenapplikation oder eines Teils dieser Applikation, und den Befehl zur Aufzeichnung dieser Tachographenapplikation oder eines Teils davon im Applikationsspeicher (5) erst dann zu geben, wenn sie vom CSP-Schaltkreis als authentisch und sicher eingestuft wurde.
- Tachograph nach einem der Ansprüche 2 oder 3, dadurch gekennzeichnet, dass die im Applikationsspeicher (5) gespeicherte Tachographenapplikation geeignet ist, wenn sie in den Hauptmikroprozessor geladen wurde, dem CSP-Schaltkreis (20) periodische Befehle zur Ausführung mindestens einer Sicherheitsoperation im Hinblick auf die Authentifizierung besagter Tachographenapplikation zu geben.
- Tachograph nach einem der Ansprüche 1 bis 4, dadurch gekennzeichnet, dass der (die) CSP-Schaltkreis(e) (20) im Wesentlichen der Ausführung von Sicherheitsoperationen dienen.
- Tachograph nach einem der Ansprüche 1 bis 5, dadurch gekennzeichnet, dass der (die) CSP-Schaltkreis(e) (20) im Wesentlichen der Ausführung aller Sicherheitsoperationen dienen.
- Tachograph nach einem der Ansprüche 1 bis 6, dadurch gekennzeichnet, dass jeder CSP-Schaltkreis (20) mit einem Hauptmikroprozessor (4) verbunden ist, wobei besagter CSP-Schaltkreis und der diesem zugeordnete Hauptmikroprozessor geeignet sind, nach einer Master-Slave-Beziehung zu arbeiten, bei der der Hauptmikroprozessor der "Master" und der CSP-Schaltkreis der "Sklave" ist.
- Tachograph nach einem der Ansprüche 1 bis 7, dadurch gekennzeichnet, dass sich der (die) CSP-Schaltkreis(e) (20) auf der Hauptkarte (3) befindet (befinden).
- Tachograph nach einem der Ansprüche 1 bis 8, dadurch gekennzeichnet, dass- der Tachograph ein Chipkartenlese-/registriergerät (8) beinhaltet, das geeignet ist, mindestens zwei Chipkarten, Tachographenkarten genannt, nebeneinander aufzunehmen, wobei jede Karte einem vorbestimmten Kartentyp entspricht,- das Kartenlese-/registriergerät (8) von mindestens einem Hauptmikroprozessor (4) gesteuert wird, dem ein CSP-Schaltkreis (20) zugeordnet ist, wobei besagter Hauptmikroprozessor geeignet ist, besagtem CSP-Schaltkreis den Befehl zur Ausführung mindestens einer Sicherheitsoperation zu geben, im Hinblick auf eine gegenseitige Authentifizierung des Tachographen und einer im Kartenlese-/registriergerät befindlichen Tachographenkarte, und erst dann eine der Art der vorliegenden Tachographenkarte entsprechende Betriebsphase zuzulassen, wenn Tachograph und besagte Karte als authentisch gelten.
- Tachograph nach Anspruch 9, dadurch gekennzeichnet, dass der Hauptmikroprozessor (4) geeignet ist, das Einführen von Karten in das bzw. das Herausnehmen von Karten aus dem Kartenlese-/registriergerät (8) zu überwachen und den Befehl zur Ausführung dieser Sicherheitsoperation(en) zu geben, sobald festgestellt wird, dass eine Tachographenkarte in das Kartenlese-/registriergerät eingeschoben wurde.
- Tachograph nach einem der Ansprüche 1 bis 10, dadurch gekennzeichnet, dass- der Tachograph eine Verbindungsschnittstelle (16), Kartenschnittstelle genannt, für die drahtlose Verbindung des Tachographen mit einem externen Chipkartenlese-/registriergerät beinhaltet, wobei diese Chipkarten Tachographenkarten genannt werden, und jede Karte einem vorbestimmten Kartentyp entspricht,- besagtes externes Lese-/registriergerät von mindestens einem Hauptmikroprozessor (4) gesteuert wird, dem ein CSP-Schaltkreis (20) zugeordnet ist, wobei besagter Hauptmikroprozessor geeignet ist, besagtem CSP-Schaltkreis den Befehl zur Ausführung mindestens einer Sicherheitsoperation zu geben, im Hinblick auf eine gegenseitige Authentifizierung des Tachographen und einer im Kartenlese-/registriergerät befindlichen Tachographenkarte, und erst dann eine der Art der vorliegenden Tachographenkarte entsprechende Betriebsphase zuzulassen, wenn Tachograph und besagte Karte als authentisch gelten.
- Tachograph nach einem der Ansprüche 9 bis 11, dadurch gekennzeichnet, dass bei jedem Datenaustausch zwischen dem Tachographen (1) und einer im Kartenlese-/registriergerät befindlichen Tachographenkarte (60) besagter Hauptmikroprozessor (4) geeignet ist, besagtem CSP-Schaltkreis (20) den Befehl zur Ausführung mindestens einer Sicherheitsoperation zu geben, im Hinblick auf die Authentifizierung besagter Daten, und die ausgetauschten Daten erst dann zu verarbeiten, wenn sie als authentisch und sicher gelten.
- Tachograph nach Anspruch 12, dadurch gekennzeichnet, dass der Hauptmikroprozessor (4) geeignet ist,- wenn der Tachograph Daten von besagter Tachographenkarte erhält, dem CSP-Schaltkreis (20) den Befehl zur Ausführung mindestens einer Sicherheitsoperation zu geben, im Hinblick auf die Authentifizierung der erhaltenen Daten, und besagte Daten erst dann zu verarbeiten, wenn sie vom CSP-Schaltkreis als authentisch und sicher eingestuft wurden,- wenn Daten vom Tachographen an besagte Tachographenkarte übertragen werden müssen, dem CSP-Schaltkreis (20) den Befehl zur Ausführung mindestens einer Sicherheitsoperation zu geben, im Hinblick auf den Schutz der Integrität der zu übertragenden Daten.
- Tachograph nach einem der Ansprüche 1 bis 13, beinhaltend eine Verbindungsschnittstelle (12), Sensorschnittstelle genannt, zur Verbindung des Tachographen mit dem Bewegungssensor, dadurch gekennzeichnet, dass die Hauptkarte (3) mindestens einen Hauptmikroprozessor (4) enthält, der mit besagter Sensorschnittstelle (12) verbunden ist, und dem ein CSP-Schaltkreis (20) zugeordnet ist, wobei besagter Hauptmikroprozessor (4) geeignet ist, besagtem CSP-Schaltkreis (20) dem Befehl zur Ausführung von Sicherheitsoperationen zu geben, im Hinblick einerseits auf die gegenseitige Authentifizierung des Bewegungssensors und des Tachographen, und andererseits auf die Authentifizierung der vom Bewegungssensor an den Tachographen gelieferten Bewegungsdaten, und die erhaltenen Bewegungsdaten erst dann zu verarbeiten, wenn Bewegungssensor und Tachograph als authentisch und die erhaltenen Daten als authentisch und sicher gelten.
- Tachograph nach Anspruch 14, dadurch gekennzeichnet, dass besagter Hauptmikroprozessor (4) geeignet ist,- im Rahmen einer ersten Inbetriebnahme, "Paarung" eines Bewegungssensors mit dem Tachographen genannt, besagtem CSP-Schaltkreis (20) den Befehl zur Ausführung mindestens einer Sicherheitsoperation zu geben, im Hinblick auf die gegenseitige Authentifizierung des Sensors und des Tachographen, und einen späteren Datenaustausch zwischen besagtem Sensor und dem Tachographen erst dann zuzulassen, wenn letztere als authentisch gelten,- im Rahmen eines periodischen Betriebs, Prüfung der Bewegungsdaten genannt, dem CSP-Schaltkreis (20) den Befehl zur Ausführung mindestens einer Sicherheitsoperation im Hinblick auf die Authentifizierung der Daten, Prüfdaten genannt, zu geben, die zwischen dem Sensor und dem Tachographen im Rahmen dieser Prüfung ausgetauscht werden, und die Verarbeitung der vom Tachographen über einen abgelaufenen Zeitraum empfangenen Bewegungsdaten erst dann zuzulassen, wenn besagte Prüfdaten als authentisch und sicher gelten.
- Tachograph nach Anspruch 15 und 9, dadurch gekennzeichnet, dass der (die) Hauptmikroprozessor(en) (4) geeignet ist (sind), die Ausführung einer "Paarung" genannten Operation nur im Rahmen eines Werkstattbesuchs zuzulassen.
- Tachograph nach einem der Ansprüche 1 bis 16 und nach einem der Ansprüche 9 oder 11, dadurch gekennzeichnet, dass- er eine Verbindungsschnittstelle (13, 14), Entladeschnittstelle genannt, beinhaltet, zur Verbindung des Tachographen mit einer externen Vorrichtung, Entladevorrichtung genannt, die geeignet ist, Tachographendaten zu speichern,- der (die) Hauptmikroprozessor(en) (4) geeignet ist (sind), das Entladen von Daten in eine mit dem Tachographen über die Entladeschnittstelle verbundene Entladevorrichtung nur im Rahmen eines Besuchs des Prüfers, der Werkstatt oder der Firma zuzulassen.
- Tachograph nach einem der Ansprüche 1 bis 17 und nach Anspruch 9, dadurch gekennzeichnet, dass- er eine Verbindungsschnittstelle (13, 14), Kalibrierschnittstelle genannt, zur Verbindung des Tachographen mit einer externen Vorrichtung, Kalibriervorrichtung genannt, beinhaltet,- der (die) Hauptmikroprozessor(en) (4) geeignet ist (sind), das Kalibrieren des Tachographen mittels einer mit dem Tachographen über die Kalibrierschnittstelle verbundenen Kalibriervorrichtung nur im Rahmen eines Werkstattbesuchs zuzulassen.
- Tachograph nach einem der Ansprüche 1 bis 18, und nach Anspruch 9, dadurch gekennzeichnet, dass ein Hauptmikroprozessor (4) des Tachographen geeignet ist, das Einführen von Karten in das bzw. das Herausnehmen von Karten aus dem Kartenlese-/registriergerät (8) zu überwachen, und, sobald die Herausnahme einer Tachographenkarte aus dem Kartenlese-/registriergerät festgestellt wird, jede laufende Operation während der entsprechenden Betriebsphase zu unterbrechen.
- Tachograph nach einem der Ansprüche 1 bis 19, dadurch gekennzeichnet, dass- die Hauptkarte (3) einen einzigen Hauptmikroprozessor (4) zur Verarbeitung der Tachographendaten beinhaltet, dem ein Speisestromkreis (6) zugeordnet ist, der permanent von einer permanenten Stromquelle des Fahrzeugs gespeist wird, sowie ein nichtflüchtiger Massenspeicher (5), Applikationsspeicher genannt, zur Speicherung mindestens einer Applikation, Tachographenapplikation genannt, ein nichtflüchtiger Massenspeicher (17), Datenspeicher genannt, zur Speicherung mindestens der Tachographendaten, eine Echtzeituhr mit Kalender (7), ein Chipkartenlese-/registriergerät (8), wobei diese Chipkarten Tachographenkarten genannt werden, und das Gerät geeignet ist, mindestens zwei Tachographenkarten nebeneinander aufzunehmen, einen Verbinder (12), Sensorverbinder genannt, um den Tachographen an den Bewegungssensor anzuschließen, einen Verbinder (13), Entlade-/Kalibrierverbinder genannt, um an den Tachographen ein externes Kalibriergerät oder ein externes Entladegerät anzuschließen,- der Tachograph einen einzigen CSP-Schaltkreis (20) beinhaltet, der zur Durchführung aller Sicherheitsoperationen dient, wobei besagter Hauptmikroprozessor (4) und der CSP-Schaltkreis (20) verbunden und geeignet sind, nach einer Master-Slave-Beziehung zu arbeiten, bei der der Hauptmikroprozessor der "Master" und der CSP-Schaltkreis der "Sklave" ist,- der Tachograph einen Drucker (10), einen Bildschirm (9) und eine Vorrichtung (11) zur Datenerfassung durch einen Nutzer beinhaltet.
- Kraftfahrzeug, dadurch gekennzeichnet, dass es mit einem Tachographen nach einem der Ansprüche 1 bis 20 ausgestattet ist.
Priority Applications (1)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| PL05818272T PL1815256T3 (pl) | 2004-11-22 | 2005-11-22 | Jednostka tachografu elektronicznego dla pojazdu samochodowego |
Applications Claiming Priority (2)
| Application Number | Priority Date | Filing Date | Title |
|---|---|---|---|
| FR0412379A FR2878355B1 (fr) | 2004-11-22 | 2004-11-22 | Unite de tachigraphe electronique pour vehicule automobile |
| PCT/FR2005/002893 WO2006053998A1 (fr) | 2004-11-22 | 2005-11-22 | Unite de tachygraphe electronique pour véhicule automobile |
Publications (2)
| Publication Number | Publication Date |
|---|---|
| EP1815256A1 EP1815256A1 (de) | 2007-08-08 |
| EP1815256B1 true EP1815256B1 (de) | 2013-01-02 |
Family
ID=34951974
Family Applications (1)
| Application Number | Title | Priority Date | Filing Date |
|---|---|---|---|
| EP05818272A Revoked EP1815256B1 (de) | 2004-11-22 | 2005-11-22 | Elektronischer tachograph für ein kraftfahrzeug |
Country Status (6)
| Country | Link |
|---|---|
| EP (1) | EP1815256B1 (de) |
| BR (1) | BRPI0517699A (de) |
| ES (1) | ES2401592T3 (de) |
| FR (1) | FR2878355B1 (de) |
| PL (1) | PL1815256T3 (de) |
| WO (1) | WO2006053998A1 (de) |
Cited By (2)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| DE102013214798A1 (de) | 2013-07-29 | 2015-01-29 | Continental Automotive Gmbh | Tachografenanordnung und Verfahren zum Betreiben einer Tachografenanordnung |
| EP4019979A3 (de) * | 2020-12-23 | 2022-08-10 | Continental Automotive Technologies GmbH | Tachographensystem für ein kraftfahrzeug, kraftfahrzeug und verfahren zum betreiben eines tachographensystems |
Families Citing this family (6)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| DE102007058163A1 (de) | 2007-09-28 | 2009-04-23 | Continental Automotive Gmbh | Tachograph, Maut-On-Board-Unit, Anzeigeinstrument und System |
| DE102009051350A1 (de) | 2009-10-30 | 2011-05-05 | Continental Automotive Gmbh | Verfahren zum Betreiben eines Tachographen und Tachograph |
| EP2362357B1 (de) | 2010-02-22 | 2020-02-12 | Stoneridge Electronics AB | Erweiterte Fahrtenschreiberfunktionen |
| EP2369555B1 (de) | 2010-02-22 | 2014-07-02 | Stoneridge Electronics AB | Temporärer Download |
| BE1020818A3 (fr) * | 2012-07-05 | 2014-05-06 | Hennekinne Yves | Systeme de cartes a puces pour automobile. |
| RU209414U1 (ru) * | 2021-12-02 | 2022-03-16 | Общество с ограниченной ответственностью "НОВЫЕ РЕШЕНИЯ ДРАЙВА" | Цифровой тахограф |
Family Cites Families (5)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| DE3505068C1 (de) * | 1985-02-14 | 1986-06-19 | Mannesmann Kienzle GmbH, 7730 Villingen-Schwenningen | Fahrtschreiber fuer Kraftfahrzeuge |
| GB9220875D0 (en) * | 1992-10-05 | 1992-11-18 | Matra Marconi Space Uk Ltd | A tachograph |
| US5497419A (en) * | 1994-04-19 | 1996-03-05 | Prima Facie, Inc. | Method and apparatus for recording sensor data |
| US6556905B1 (en) * | 2000-08-31 | 2003-04-29 | Lisa M. Mittelsteadt | Vehicle supervision and monitoring |
| AU2002211692A1 (en) * | 2000-10-12 | 2002-04-22 | Southwest Research Institute | Method and apparatus for personnel transportable data recording |
-
2004
- 2004-11-22 FR FR0412379A patent/FR2878355B1/fr not_active Expired - Fee Related
-
2005
- 2005-11-22 BR BRPI0517699-9A patent/BRPI0517699A/pt not_active Application Discontinuation
- 2005-11-22 ES ES05818272T patent/ES2401592T3/es not_active Expired - Lifetime
- 2005-11-22 WO PCT/FR2005/002893 patent/WO2006053998A1/fr not_active Ceased
- 2005-11-22 EP EP05818272A patent/EP1815256B1/de not_active Revoked
- 2005-11-22 PL PL05818272T patent/PL1815256T3/pl unknown
Cited By (3)
| Publication number | Priority date | Publication date | Assignee | Title |
|---|---|---|---|---|
| DE102013214798A1 (de) | 2013-07-29 | 2015-01-29 | Continental Automotive Gmbh | Tachografenanordnung und Verfahren zum Betreiben einer Tachografenanordnung |
| EP4019979A3 (de) * | 2020-12-23 | 2022-08-10 | Continental Automotive Technologies GmbH | Tachographensystem für ein kraftfahrzeug, kraftfahrzeug und verfahren zum betreiben eines tachographensystems |
| EP4212884A1 (de) * | 2020-12-23 | 2023-07-19 | Continental Automotive Technologies GmbH | Tachographensystem für ein kraftfahrzeug, kraftfahrzeug und verfahren zum betreiben eines tachographensystems |
Also Published As
| Publication number | Publication date |
|---|---|
| ES2401592T3 (es) | 2013-04-22 |
| FR2878355B1 (fr) | 2007-02-23 |
| EP1815256A1 (de) | 2007-08-08 |
| WO2006053998A1 (fr) | 2006-05-26 |
| BRPI0517699A (pt) | 2008-10-14 |
| FR2878355A1 (fr) | 2006-05-26 |
| PL1815256T3 (pl) | 2013-06-28 |
Similar Documents
| Publication | Publication Date | Title |
|---|---|---|
| EP3547270B1 (de) | Überprüfungsverfahren einer biometrischen authentifizierung | |
| EP0037762A1 (de) | Verfahren und System zur Übertragung signierter Nachrichten | |
| EP1964307A1 (de) | Verfahren zum erzeugen eines sicheren zählers auf einem onboard-computersystem mit einer chipkarte | |
| EP2500872A1 (de) | Gesichertes Steuerungsverfahren zur Öffnung von Schließvorrichtungen mit Hilfe eines kommunizierenden Objekts vom Typ Handy | |
| FR2922396A1 (fr) | Procede d'authentification biometrique, programme d'ordinateur, serveur d'authentification, terminal et objet portatif correspondants | |
| EP0531241A1 (de) | Elektronisches Zugangskontrollsystem | |
| EP1293062B1 (de) | Verfahren zur gesicherten biometrischen authentifizierung oder identifizierung, erfassungsmodul und modul zur prüfung biometrischer daten | |
| WO2012160298A1 (fr) | Acces et personnalisation d'un vehicule automobile par telephone | |
| FR2989799A1 (fr) | Procede de transfert d'un dispositif a un autre de droits d'acces a un service | |
| FR2950450A1 (fr) | Procede de verification de la validite d'un ticket electronique de stationnement. | |
| FR2996947A1 (fr) | Procede securise de commande d'ouverture de dispositifs de serrure a partir de messages mettant en oeuvre un cryptage symetrique | |
| EP1815256B1 (de) | Elektronischer tachograph für ein kraftfahrzeug | |
| WO2015135793A1 (fr) | Procédé de contrôle d'accès à une zone réservée avec contrôle de la validité d'un titre d'accès stocké dans la mémoire d'un terminal mobile | |
| FR2795579A1 (fr) | Procede de securisation d'une communication de donnees entre un support de donnees et un vehicule et dispositif de surveillance du fonctionnement d'un vehicule | |
| EP0856624B1 (de) | Sicherheitsvorrichtung für Kraftfahrzeuge und Lernverfahren dafür | |
| EP1683112A1 (de) | System zur steuerung von informationen in bezug auf ein fahrzeug | |
| FR2835951A1 (fr) | Systeme d'authentification electronique | |
| EP1653415A1 (de) | Verfahren und Ausrüstung zur Verwaltung von Zugangskontrollkarten | |
| EP1825441B1 (de) | Einheit eines elektronischen tachographen für ein kraftfahrzeug | |
| FR2774494A1 (fr) | Systeme d'affranchissement postal securise | |
| WO2017005644A1 (fr) | Procédé et système de contrôle d'accès à un service via un média mobile sans intermediaire de confiance | |
| FR3117655A1 (fr) | Système de tachygraphe, dispositif de tachygraphe et procédé de fonctionnement d’un système de tachygraphe | |
| FR3156555A1 (fr) | Procede d’enregistrement renforce d’un fichier numerique associe a des donnees internationales | |
| FR3090026A1 (fr) | Demande d'acces et autorisation d'acces mains libres a un objet apte a etre verrouiller | |
| WO2023094744A1 (fr) | Procédé d'établissement d'une transaction entre un objet communicant et un module de controle de la transaction associé à un dispositif de fourniture de bien(s) ou de service(s) |
Legal Events
| Date | Code | Title | Description |
|---|---|---|---|
| PUAI | Public reference made under article 153(3) epc to a published international application that has entered the european phase |
Free format text: ORIGINAL CODE: 0009012 |
|
| 17P | Request for examination filed |
Effective date: 20070614 |
|
| AK | Designated contracting states |
Kind code of ref document: A1 Designated state(s): AT BE BG CH CY CZ DE DK EE ES FI FR GB GR HU IE IS IT LI LT LU LV MC NL PL PT RO SE SI SK TR |
|
| AX | Request for extension of the european patent |
Extension state: AL BA HR MK YU |
|
| RAP1 | Party data changed (applicant data changed or rights of an application transferred) |
Owner name: ACTIA AUTOMOTIVE |
|
| REG | Reference to a national code |
Ref country code: DE Ref legal event code: R079 Ref document number: 602005037754 Country of ref document: DE Free format text: PREVIOUS MAIN CLASS: G01P0001120000 Ipc: G07C0007000000 |
|
| GRAP | Despatch of communication of intention to grant a patent |
Free format text: ORIGINAL CODE: EPIDOSNIGR1 |
|
| RIC1 | Information provided on ipc code assigned before grant |
Ipc: G07C 7/00 20060101AFI20120425BHEP Ipc: G07C 5/08 20060101ALI20120425BHEP Ipc: G01P 1/12 20060101ALI20120425BHEP |
|
| GRAS | Grant fee paid |
Free format text: ORIGINAL CODE: EPIDOSNIGR3 |
|
| GRAA | (expected) grant |
Free format text: ORIGINAL CODE: 0009210 |
|
| AK | Designated contracting states |
Kind code of ref document: B1 Designated state(s): AT BE BG CH CY CZ DE DK EE ES FI FR GB GR HU IE IS IT LI LT LU LV MC NL PL PT RO SE SI SK TR |
|
| AX | Request for extension of the european patent |
Extension state: AL BA HR MK YU |
|
| REG | Reference to a national code |
Ref country code: GB Ref legal event code: FG4D Free format text: NOT ENGLISH |
|
| REG | Reference to a national code |
Ref country code: CH Ref legal event code: EP Ref country code: AT Ref legal event code: REF Ref document number: 591970 Country of ref document: AT Kind code of ref document: T Effective date: 20130115 |
|
| BECA | Be: change of holder's address |
Owner name: 5 RUE JORGE SEMPRUN,F-31432 TOULOUSE CEDEX 4 Effective date: 20130102 Owner name: ACTIA AUTOMOTIVE Effective date: 20130102 |
|
| REG | Reference to a national code |
Ref country code: IE Ref legal event code: FG4D Free format text: LANGUAGE OF EP DOCUMENT: FRENCH |
|
| REG | Reference to a national code |
Ref country code: DE Ref legal event code: R096 Ref document number: 602005037754 Country of ref document: DE Effective date: 20130307 |
|
| RAP2 | Party data changed (patent owner data changed or rights of a patent transferred) |
Owner name: ACTIA AUTOMOTIVE |
|
| REG | Reference to a national code |
Ref country code: SE Ref legal event code: TRGR |
|
| REG | Reference to a national code |
Ref country code: ES Ref legal event code: FG2A Ref document number: 2401592 Country of ref document: ES Kind code of ref document: T3 Effective date: 20130422 |
|
| REG | Reference to a national code |
Ref country code: NL Ref legal event code: T3 |
|
| REG | Reference to a national code |
Ref country code: AT Ref legal event code: MK05 Ref document number: 591970 Country of ref document: AT Kind code of ref document: T Effective date: 20130102 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: SI Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 |
|
| REG | Reference to a national code |
Ref country code: EE Ref legal event code: FG4A Ref document number: E007912 Country of ref document: EE Effective date: 20130401 |
|
| PLBI | Opposition filed |
Free format text: ORIGINAL CODE: 0009260 |
|
| REG | Reference to a national code |
Ref country code: LT Ref legal event code: MG4D |
|
| REG | Reference to a national code |
Ref country code: PL Ref legal event code: T3 |
|
| 26 | Opposition filed |
Opponent name: STONERIDGE ELECTRONICS AB Effective date: 20130605 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: CY Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 Ref country code: LT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 Ref country code: AT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 Ref country code: BG Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130402 Ref country code: IS Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130502 Ref country code: CZ Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: PT Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130502 Ref country code: GR Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130403 Ref country code: FI Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 Ref country code: LV Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 |
|
| REG | Reference to a national code |
Ref country code: DE Ref legal event code: R026 Ref document number: 602005037754 Country of ref document: DE Effective date: 20130605 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: RO Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 Ref country code: DK Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 Ref country code: SK Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 |
|
| PLAX | Notice of opposition and request to file observation + time limit sent |
Free format text: ORIGINAL CODE: EPIDOSNOBS2 |
|
| PLAF | Information modified related to communication of a notice of opposition and request to file observations + time limit |
Free format text: ORIGINAL CODE: EPIDOSCOBS2 |
|
| PLAF | Information modified related to communication of a notice of opposition and request to file observations + time limit |
Free format text: ORIGINAL CODE: EPIDOSCOBS2 |
|
| REG | Reference to a national code |
Ref country code: CH Ref legal event code: PL |
|
| PLBB | Reply of patent proprietor to notice(s) of opposition received |
Free format text: ORIGINAL CODE: EPIDOSNOBS3 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: LI Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20131130 Ref country code: MC Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 Ref country code: CH Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20131130 |
|
| REG | Reference to a national code |
Ref country code: IE Ref legal event code: MM4A |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: IE Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20131122 |
|
| PLAB | Opposition data, opponent's data or that of the opponent's representative modified |
Free format text: ORIGINAL CODE: 0009299OPPO |
|
| PLAB | Opposition data, opponent's data or that of the opponent's representative modified |
Free format text: ORIGINAL CODE: 0009299OPPO |
|
| R26 | Opposition filed (corrected) |
Opponent name: STONERIDGE ELECTRONICS AB Effective date: 20130605 |
|
| R26 | Opposition filed (corrected) |
Opponent name: STONERIDGE ELECTRONICS AB Effective date: 20130605 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: TR Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT Effective date: 20130102 |
|
| PG25 | Lapsed in a contracting state [announced via postgrant information from national office to epo] |
Ref country code: LU Free format text: LAPSE BECAUSE OF NON-PAYMENT OF DUE FEES Effective date: 20131122 Ref country code: HU Free format text: LAPSE BECAUSE OF FAILURE TO SUBMIT A TRANSLATION OF THE DESCRIPTION OR TO PAY THE FEE WITHIN THE PRESCRIBED TIME-LIMIT; INVALID AB INITIO Effective date: 20051122 |
|
| REG | Reference to a national code |
Ref country code: FR Ref legal event code: PLFP Year of fee payment: 11 |
|
| PLAB | Opposition data, opponent's data or that of the opponent's representative modified |
Free format text: ORIGINAL CODE: 0009299OPPO |
|
| R26 | Opposition filed (corrected) |
Opponent name: STONERIDGE ELECTRONICS AB Effective date: 20130605 |
|
| PGFP | Annual fee paid to national office [announced via postgrant information from national office to epo] |
Ref country code: IT Payment date: 20151118 Year of fee payment: 11 Ref country code: GB Payment date: 20151014 Year of fee payment: 11 Ref country code: DE Payment date: 20151109 Year of fee payment: 11 Ref country code: EE Payment date: 20151026 Year of fee payment: 11 |
|
| PGFP | Annual fee paid to national office [announced via postgrant information from national office to epo] |
Ref country code: PL Payment date: 20151026 Year of fee payment: 11 Ref country code: NL Payment date: 20151014 Year of fee payment: 11 Ref country code: SE Payment date: 20151117 Year of fee payment: 11 Ref country code: ES Payment date: 20151125 Year of fee payment: 11 Ref country code: BE Payment date: 20151123 Year of fee payment: 11 Ref country code: FR Payment date: 20150925 Year of fee payment: 11 |
|
| RDAF | Communication despatched that patent is revoked |
Free format text: ORIGINAL CODE: EPIDOSNREV1 |
|
| APBM | Appeal reference recorded |
Free format text: ORIGINAL CODE: EPIDOSNREFNO |
|
| APBP | Date of receipt of notice of appeal recorded |
Free format text: ORIGINAL CODE: EPIDOSNNOA2O |
|
| APAH | Appeal reference modified |
Free format text: ORIGINAL CODE: EPIDOSCREFNO |
|
| REG | Reference to a national code |
Ref country code: DE Ref legal event code: R064 Ref document number: 602005037754 Country of ref document: DE Ref country code: DE Ref legal event code: R103 Ref document number: 602005037754 Country of ref document: DE |
|
| APBU | Appeal procedure closed |
Free format text: ORIGINAL CODE: EPIDOSNNOA9O |
|
| RDAG | Patent revoked |
Free format text: ORIGINAL CODE: 0009271 |
|
| STAA | Information on the status of an ep patent application or granted ep patent |
Free format text: STATUS: PATENT REVOKED |
|
| 27W | Patent revoked |
Effective date: 20160808 |
|
| GBPR | Gb: patent revoked under art. 102 of the ep convention designating the uk as contracting state |
Effective date: 20160808 |
|
| REG | Reference to a national code |
Ref country code: EE Ref legal event code: MF4A Ref document number: E007912 Country of ref document: EE Effective date: 20161025 |
|
| REG | Reference to a national code |
Ref country code: SE Ref legal event code: ECNC |